How to Hunt for Zip Slip Exploits in Open Source Bug Bounty | huntr.dev #methodology

Source link
Related Articles
All Mix →My OpenAI Event Predictions (May 2024)
Table of Contents What I anticipate All about agents A personal DA A mix of agent stuff Summary I don’t have any insider knowledge—unless you…
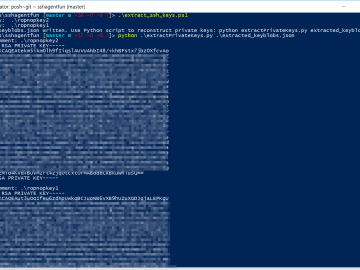
Extracting SSH Private Keys From Windows 10 ssh-agent
This weekend I installed the Windows 10 Spring Update, and was pretty excited to start playing with the new, builtin OpenSSH tools. Using OpenSSH natively…
Enhancing OWASP Noir with AI
Table of Contents Setting Up AI Integration Install and Configure Ollama Running Noir with AI How Does It Work? Next Plan Conclusion References Enhancing Security…
How to Integrate Claude Code with Neovim Using Ghostty Terminal Panes
Table of Contents The Setup The Configuration Why It Works Getting Started If you’re a Neovim user feeling left out watching everyone use Claude Code…
UL NO. 446: AI Ecosystem Components, MS 0-Days, Iranian Campaign Hacks…
Table of Contents TOC NOTES MY WORK SECURITY AI / TECH HUMANS IDEAS DISCOVERY RECOMMENDATION OF THE WEEK APHORISM OF THE WEEK SECURITY | AI…
5 Ways to hack WordPress targets
Table of Contents 1) Enumerating outdated instances 2) Exposed configuration files 3) Misconfigured security settings 4) Weak credentials 5) Exploiting vulnerable WordPress plugins and themes…