A security researcher recently uncovered a high-risk Insecure Direct Object Reference (IDOR) vulnerability in ExHub, a cloud hosting and collaboration platform used by over 2 million developers.
The flaw enabled attackers to manipulate web hosting configurations for any project hosted on the platform without authorization, potentially disrupting critical services or enabling further exploits.
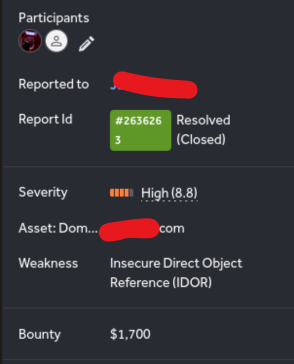
The discovery earned the researcher a $1,500 bounty, with ExHub awarding an additional $200 for the report’s clarity and a $100 retest fee after remediation.
Vulnerability Breakdown
The IDOR vulnerability resided in ExHub’s API endpoint for project deployment configurations (/api/v1/projects/deployment_configuration/
Attackers could exploit this by sending a crafted POST request with a target project’s ID—a trivial identifier often visible in URLs or network logs.
By altering parameters like machine type, ports, or authentication methods, malicious actors could reroute traffic, disable services, or weaken security protocols.
Notably, even users with minimal “reader” permissions could execute administrative actions, violating core security principles like least privilege.
“This flaw essentially handed over the keys to any project’s infrastructure,” explained the researcher, who requested anonymity. “With a single API call, an attacker could destabilize deployments or create backdoors.”
Exploitation Pathway
The researcher replicated the attack using Burp Suite, a penetration testing tool. After obtaining a valid project ID—through guesswork, phishing, or exposed logs—an attacker could send a request to modify settings such as:
{ "machineType":"t32", "port":9901, "dnsAutogen":true, "authentication":"me" }This would reconfigure the project’s hosting environment, potentially overriding firewalls or exposing internal ports. ExHub’s UI immediately reflected these changes, confirming the vulnerability’s severity.
ExHub initially classified the flaw as critical (CVSS 9.8) but later downgraded it to high-risk (8.8), citing assumptions that project IDs required some privilege to obtain.
However, the researcher emphasized that such IDs are frequently exposed in shared links or misconfigured APIs, rendering that mitigation insufficient.
Successful exploitation could lead to:
- Service Disruptions: Malicious port changes could sever user access or crash applications.
- Data Exposure: Disabling authentication mechanisms might expose sensitive data.
- Privilege Escalation: Attackers could abuse misconfigured services to pivot into internal networks.
ExHub patched the vulnerability by implementing role-based access controls (RBAC) and project ID obfuscation.
A retest on October 15, 2024, confirmed the fix’s efficacy. The company praised the researcher’s methodology, highlighting the value of ethical hacking in bolstering platform security.
As cloud platforms grow increasingly complex, rigorous vulnerability disclosure programs remain vital.
ExHub’s prompt response and bounty allocation exemplify how collaboration between researchers and enterprises can mitigate risks before widespread exploitation occurs.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free