ScamAgent is an autonomous, multi-turn AI framework developed by researcher Sanket Badhe at Rutgers University that demonstrates how large language…
rewrite this content and keep HTML tags as is: 100 attacks in first 72 hours of war Hackers target banks,…
bieten im Regelfall agentenlose Konfigurationen, greifen auf Cloud-basierte Modelle zu und belassen Daten auf den vorhandenen Plattformen. Letzteres dient sowohl…
In a world where cyber threats evolve at a blazing-fast pace, relying solely on reactive measures isn’t enough. Enter: threat…
In a world where cyber threats evolve at a blazing-fast pace, relying solely on reactive measures isn’t enough. Enter: threat…
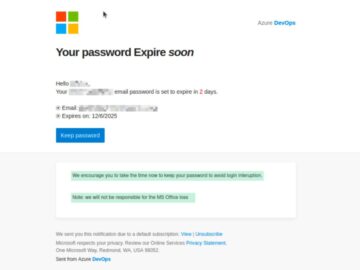
Hackers Attack Over Microsoft Teams A social-engineering campaign abusing Microsoft Teams and Windows Quick Assist is evolving again, with BlueVoyant…
He pointed out that “.arpa” queries are typically pointer (PTR) queries for reverse lookups. In the malicious queries, normal address…
A mass hacking campaign targeting iPhone users in Ukraine and China used tools that were likely designed by U.S. military…
Table Of Contents A deeper look into vulnerabilities, malware, ransomware, and insider threat As 2023 unfolds, Flashpoint continues to see…
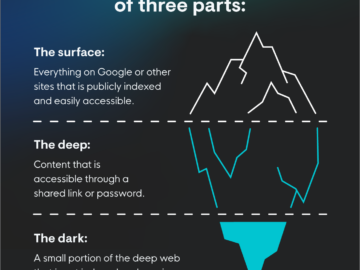
In today’s always-connected world, the line between dark and light is blurring. Well, actually, you’re still protected from finding out…
At Recorded Future, we’re constantly looking for ways to help security teams work more efficiently so they can focus their…
Picture this: it’s 4:59pm on a Friday, and you’re about to slam the work laptop shut for the weekend. You’ve…