Two Google Chrome extensions have turned malicious after what appears to be a case of ownership transfer, offering attackers a…
Artificial intelligence (AI) is a rapidly growing technology, becoming more embedded in society and business every day, but is the…
Congrats—you got the green light to move forward with improving identity access management (IAM). While you realize this is great…
Flights canceled. Emergency rooms shut down. Centuries-old companies shuttered. Ransomware and other similar cyberattacks have become so routine that even…
The European Commission has prepared a Communication providing practical guidance on applying the Cyber Resilience Act (CRA). It will help…
Effective exposure management begins by illuminating and hardening risks across the entire attack surface. Some of the most meaningful shifts…
Every security professional knows the drill. You go home for the holidays and, without volunteering, you become the family’s help…
Hikvision Multiple Products Vulnerability A severe vulnerability affecting multiple Hikvision products was added to the Known Exploited Vulnerabilities (KEV) catalog…
Welcome to the Top 10 Web Hacking Techniques of 2023, the 17th edition of our annual community-powered effort to identify…
A wave of fraudulent account registrations to a cybercrime ecosystem operating out of Vietnam. These fake accounts are not just…
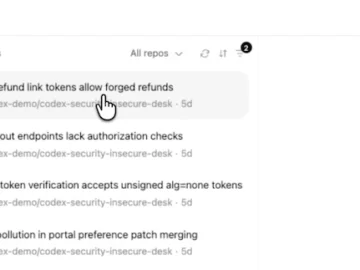
OpenAI introduced Codex Security, an AI agent that reviews codebases to find, verify, and help fix software vulnerabilities. The launch…
Anthropic on Friday hit back after U.S. Secretary of Defense Pete Hegseth directed the Pentagon to designate the artificial intelligence…