Hikvision Multiple Products Vulnerability A severe vulnerability affecting multiple Hikvision products was added to the Known Exploited Vulnerabilities (KEV) catalog…
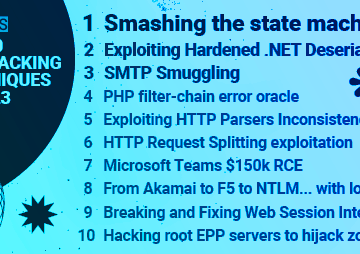
Welcome to the Top 10 Web Hacking Techniques of 2023, the 17th edition of our annual community-powered effort to identify…
A wave of fraudulent account registrations to a cybercrime ecosystem operating out of Vietnam. These fake accounts are not just…
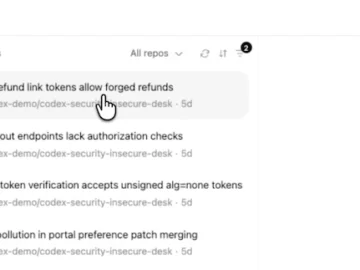
OpenAI introduced Codex Security, an AI agent that reviews codebases to find, verify, and help fix software vulnerabilities. The launch…
Anthropic on Friday hit back after U.S. Secretary of Defense Pete Hegseth directed the Pentagon to designate the artificial intelligence…
Geopolitical tensions in the Middle East following the escalating confrontation among the US, Israel and Iran have raised questions about…
Security teams are optimistic about AI’s impact on their careers, but workloads remain high. Tines’ Voice of Security 2026 report…
Targeted victims: LockBit targeted thousands of victims worldwide in its heyday, including government services, private sector companies, and critical infrastructure…
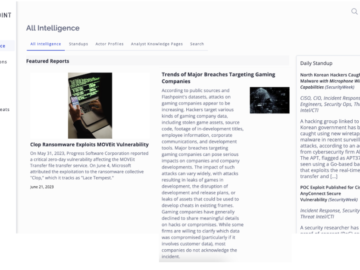
Lessons from Clop It’s been one month since the Clop ransomware group began exploiting the MOVEit vulnerability (CVE-2023-34362 (VulnDB ID:…
Special thanks to Austin Worline for his contributions to this blog post. The Huntress Security Operations Center (SOC) frequently comes…
ExifTool Flaw Malicious Images Trigger Code Execution on macOS A newly discovered vulnerability is challenging the long-held belief that macOS…
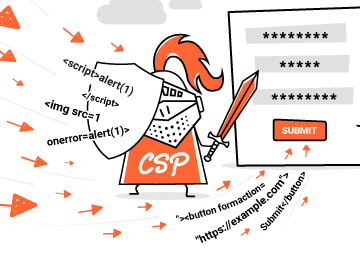
In this post we’ll show you how to bypass CSP by using an often overlooked technique that can enable password…