How to Hunt for Prototype Pollution Vulnerabilities in Open Source Bug Bounty | #methodology

Source link
Related Articles
All Mix →IT Security FAQ 4: Is two-factor authentication really necessary online? How do you activate it?
Activating 2-step verification or Two-factor authentication on a service means that you have to identify yourself twice in order to access your account – often…
The $16,000 Dev Mistake. Hello all! | by Daniel Marte
Hello all! Its been a while since my last write up. As a-lot of you know, last year I joined the Bugcrowd team as an…
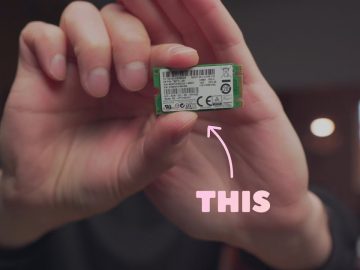
Why I am obsessed with this tiny 16GB M.2 SATA disk
Why I am obsessed with this tiny 16GB M.2 SATA disk Source link
If This Isn’t Intelligence, I Don’t Know What Is
Table of Contents 1. Tagging my entire site 2. Bring my images home 3. Converting super nasty HTML bundles to Markdown The takeaway Summary (my…
Hackers have earned more than $50M in bug bounty cash on HackerOne: Time to celebrate!
Hacking has a storied history. Hackers have always been curious people searching for new and creative ways to understand, deconstruct, and yes break systems. This…
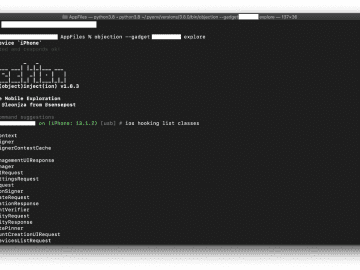
Low-Hanging Apples: Hunting Credentials and Secrets in iOS Apps
Diving straight into reverse-engineering iOS apps can be daunting and time-consuming. While wading into the binary can pay off greatly in the long run, it’s…