How to Hunt for Prototype Pollution Vulnerabilities in Open Source Bug Bounty | #methodology

Source link
Related Articles
All Mix →VR Hacking| Concerns Regarding the Rise of Virtual Reality
2017 may be the year Virtual Reality and Augmented reality truly go mainstream. But is it airtight from a security perspective? Well, the immediate answer…
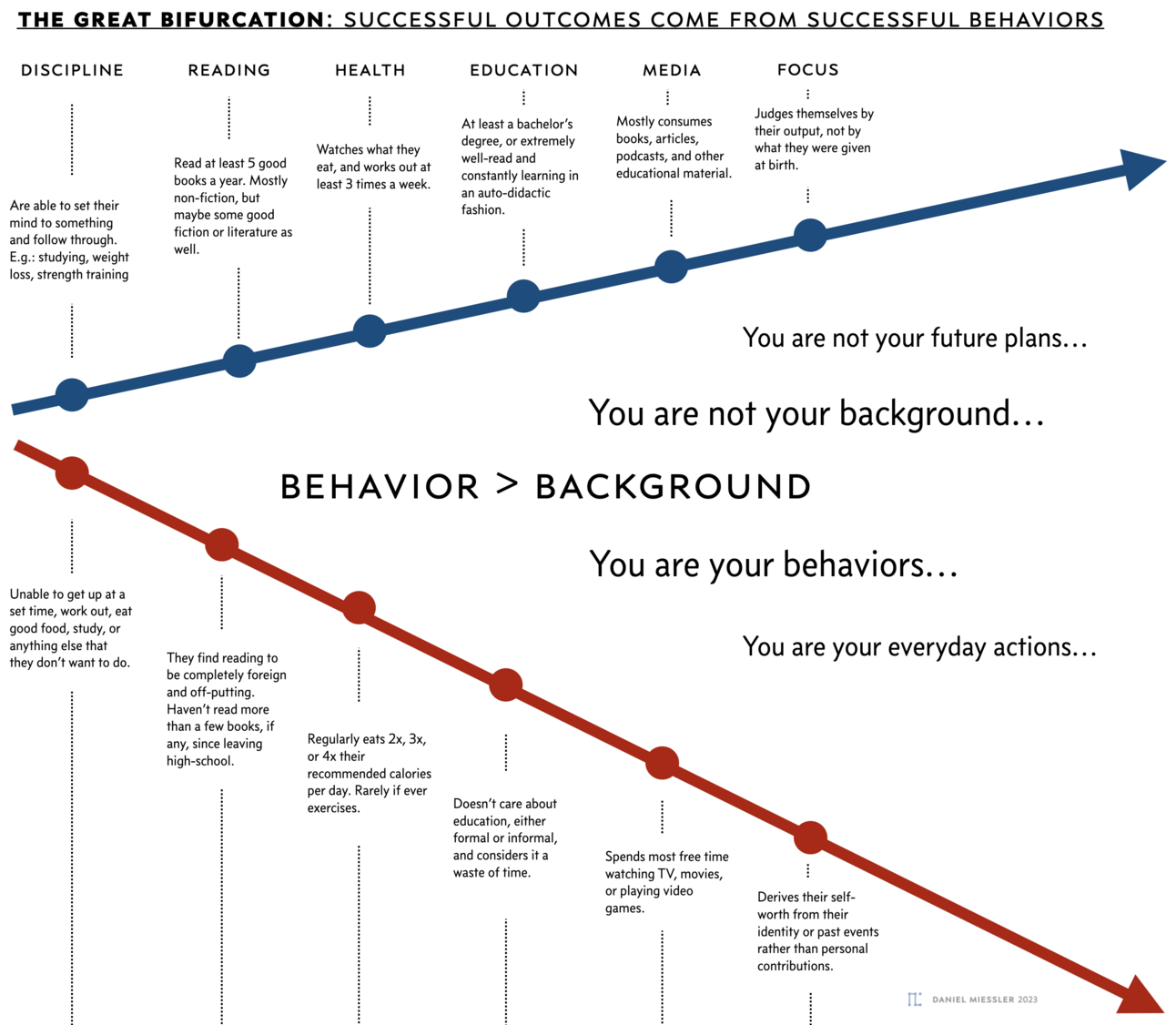
The Great Bifurcation | Daniel Miessler
Table of Contents Behavior > Identity The lie we’re told It’s just behaviors Ok, but so what? The takeaway Clarifications What about being a good…
How I’d Save The United States
I’ve been experiencing growing frustration with social/political issues lately, and each time I get to thinking about various problems that this country faces, I try…
New Security Inbox & Dashboard
Table of Contents New Security Inbox Search Bulk Actions Insights Dashboard Keyboard Shortcuts Integration, Communication, and Automation At HackerOne, we’re on a mission to empower…
CNWPP – API Hacking (3-hour live lesson) – Finishing what we started
CNWPP – API Hacking (3-hour live lesson) – Finishing what we started Source link
Beyond a VDP: How a Challenge Brings Proactive Security to Your Agency
Vulnerability Disclosure Programs create an effective means for researchers and other users to report discovered vulnerabilities and weaknesses. Because federal agencies have a significant impact…