#NahamCon2022EU: Managing a Bug Bounty Program From a Hacker’s Perspective by @0xlupin

Source link
Related Articles
All Mix →If You’re Agnostic, You’re Probably an Atheist
Table of Contents Atheism The Difference Between (A)theism and (A)gnosticism Conclusion Notes Related [ 2009-04-12 : I’ve decided to back off this specific argument of…
Hacking in Sun and Snow H1-303 Colorado
Guess what, hackers? We are back to Live Hacking Events! Hackers greeted each other with open arms after a two-year hiatus. Though the pandemic is…
[Uber 8k Bug] Login CSRF + Open Redirect = Account Take Over – Ron Chan
Have been hunting Uber bugs for quite a while, and this is my first blog post about Uber bug hunting report, hope you like it.…
My OpenAI Event Predictions (May 2024)
Table of Contents What I anticipate All about agents A personal DA A mix of agent stuff Summary I don’t have any insider knowledge—unless you…
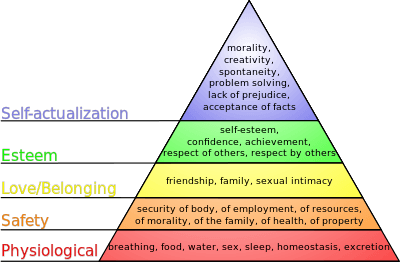
The Highest Stage of Human Awareness
The highest form of human awareness comes through a number of realizations and stages of acceptance regarding the nature of human existence. There is no…
What Happens to Content When Top-Tier Presentation is Commoditized?
I think AI is about to massively improve the quality of our best content. But not for the reason you might expect. Not because AI…