Hack the Box: How does linux work?

Source link
Related Articles
All Mix →Shifting Left with Ethical Hackers: A Q&A with GitLab
We sat down with James Ritchey, Application Security Team Manager at GitLab and a three-year member of HackerOne’s Technical Advisory Board. James talked about how…
Why I Love Ruby | Daniel Miessler
If you’re looking for a comprehensive comparison of 15 programming languages based on decades of experience, this isn’t it. I’m a hobbiest programmer. Most of…
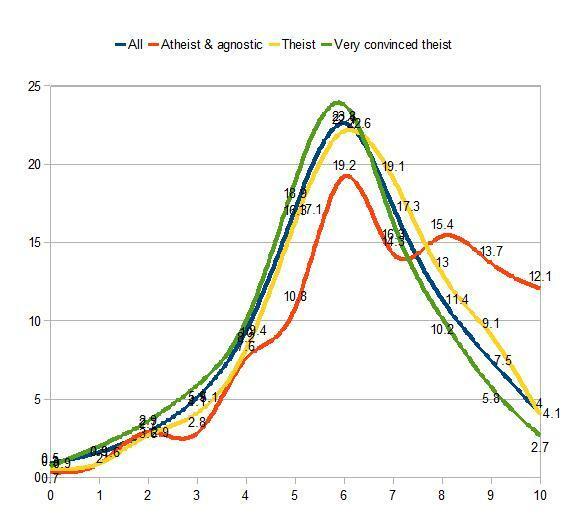
10 Interesting Data Points on IQ and Demographics
Gene Expression recently put up a brilliant post showing data on the GSS‘s WORDSUM scores correlated to various demographic data points, such as educational attainment,…
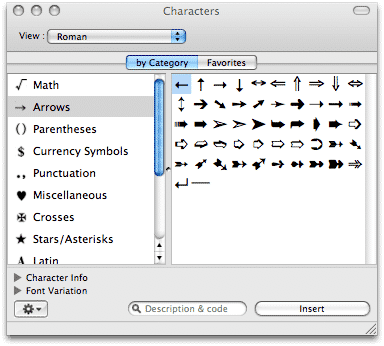
Character Encoding: Which Schemes Encode to Which Sizes?
The subject of character mapping and encoding is formidable, and many confuse the various schemes and standards available. As a reference, the list below gives…
H1 Hackers Walk the Streets of Barcelona at H1-3493!
Live Hacking Events are the ultimate voyage for hackers selected to test their skills. This time our hackers had the chance to experience gothic architecture,…
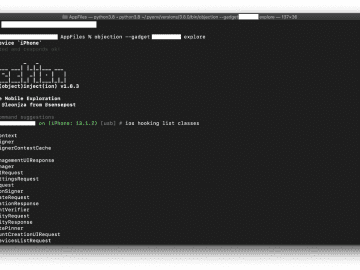
Low-Hanging Apples: Hunting Credentials and Secrets in iOS Apps
Diving straight into reverse-engineering iOS apps can be daunting and time-consuming. While wading into the binary can pay off greatly in the long run, it’s…