A massive trove of 361 million email addresses from credentials stolen by password-stealing malware, in credential stuffing attacks, and from data breaches was added to the Have I Been Pwned data breach notification service, allowing anyone to check if their accounts have been compromised.
Cybersecurity researchers collected these credentials from numerous Telegram cybercrime channels, where the stolen data is commonly leaked to the channel’s users to build reputation and subscribers.
The stolen data is usually leaked as username and password combinations (usually stolen via credential stuffing attacks or data breaches), username and passwords along with a URL associated with them (stolen via password-stealing malware), and raw cookies (stolen via password-stealing malware).
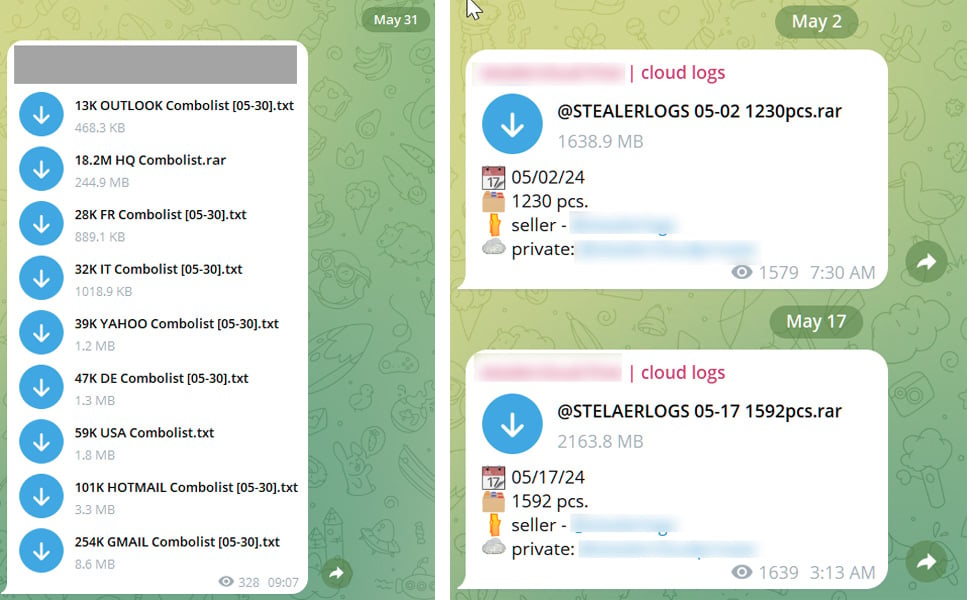
Source: Troy Hunt (left) and BleepingComputer (right)
The researchers, who asked BleepingComputer to remain anonymous, shared 122 GB of credentials with Troy Hunt, the owner of Have I Been Pwned, collected from many Telegram channels.
According to Hunt, this data is massive, containing 361 million unique email addresses, with 151 million never previously seen by the data breach notification service.
“It contained 1.7k files with 2B lines and 361M unique email addresses of which 151M had never been seen in HIBP before,” posted Hunt.
“Alongside those addresses were passwords and, in many cases, the website the data pertains to.”
With a dataset this large, it is impossible to verify that all of the leaked credentials are legitimate.
However, Hunt said that he utilized sites’ password reset forms to confirm that many leaked email addresses are correctly associated with the website listed in the stolen credentials. Hunt could not confirm the password, as that would require him to log into the account, which would be illegal.
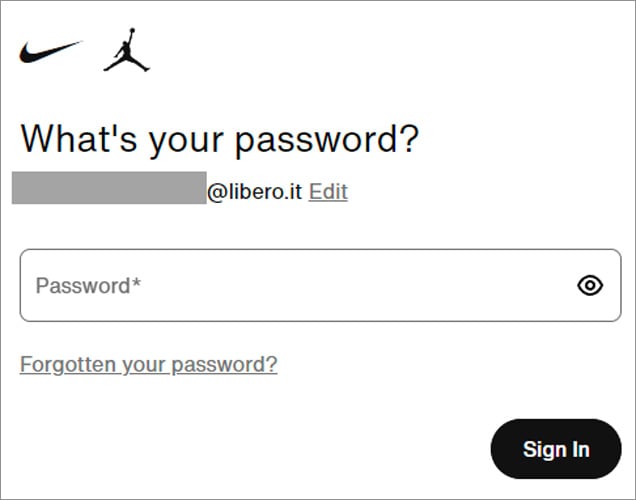
Source: Troy Hunt
No site unaffected
With a dataset this large, no site that allows logins is unaffected by these leaked credentials, including BleepingComputer.
Last week, the same researchers shared with BleepingComputer a list of credentials stolen by information-stealing malware associated with the BleepingComputer forums.
Information-stealing malware is an infection that steals passwords, cookies, browser history, cryptocurrency wallets, and other data from an infected device.
This data is compiled into an archive called a “log” and then transmitted back to the threat actor’s servers, where it is sold on cybercrime marketplaces, shared with other threat actors, or used to breach a victim’s other accounts.
This type of malware is commonly distributed through social media, cracked software, fake VPN products, or simply through malicious email campaigns sent through hacked gaming company support sites.
The data shared with BleepingCompute includes the username, password, and URL that a member used to log into our forums, which was then saved in their browser’s password manager.
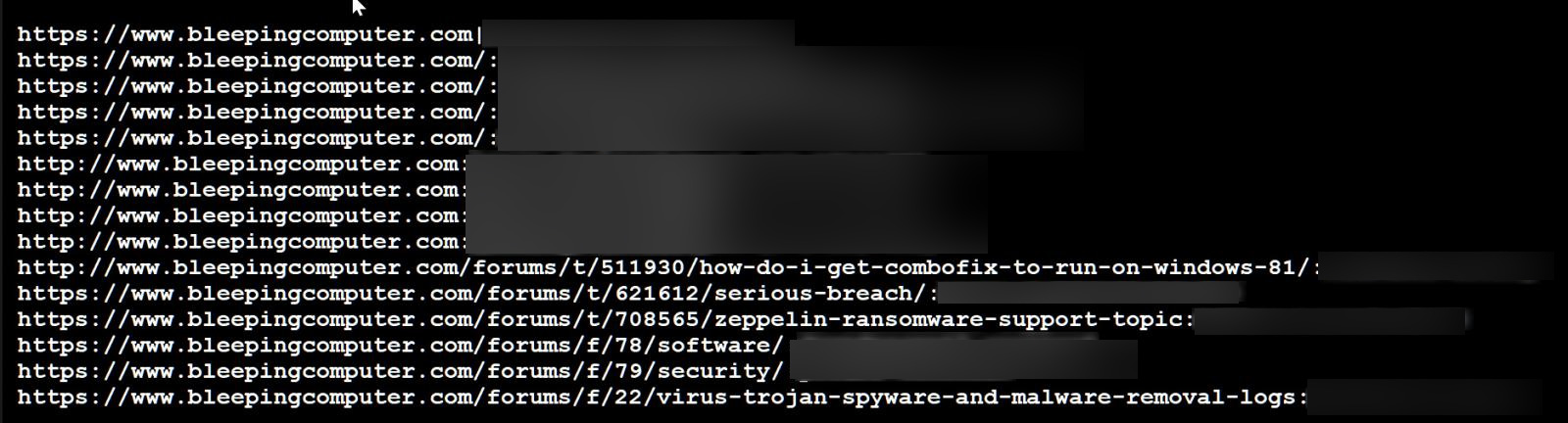
Source: BleepingComputer
As you can see from the URLs above, many users visited BleepingComputer because they suspected their computer was infected, which we now know was true.
BleepingComputer is currently analyzing the data and removing duplicates so we can proactively reset impacted members’ passwords and warn them that they were infected at some point with information-stealing malware.
Users who are infected with information-stealing malware will now have to reset every password on every account that was saved in their browser’s password manager, and any other site using the same credentials.
Unfortunately, stolen credentials are usually not shared with a timestamp to indicate when they are stolen. Therefore, impacted users must consider that all of their credentials have been compromised.
While this will be an arduous task, at least they will know why their accounts and services have exhibited strange behavior over the years.
BleepingComputer is commonly contacted by people who tell us that their accounts continuously get hacked, even when they change the password over and over. These people constantly report strange behavior on their devices or networks, but no malware infections are ever found.
The user can now gain some closure, knowing that they were not crazy, but that the malicious activity is likely attributed to their credentials previously being stolen and threat actors abusing them for their own amusement or malicious activity.
Information-stealing malware has become a scourge of cybersecurity, used by threat actors to conduct massive attacks, such as ransomware and data theft attacks.
Some well known attacks caused by credentials being stolen by information stealing malware, including attacks on the Costa Rican government, Microsoft, CircleCi, and an account at Orange Spain RIPE that led to a intentional BGP misconfiguration.
More recently threat actors stole data from Snowflake databases using what is believed to be compromised credentials stolen using information-stealing malware.
Unfortunately, there is no easy solution to prevent information-stealing attacks, as they are low complexity, making them have have wide distribution through a variety of attacks.
The best defense is to practice good cybersecurity habits, including not opening attachments from untrusted sources, downloading software only from trusted sources, enabling file extensions in Windows, using antivirus software, and keeping your software updated.
A more detailed guide related to ransomware but still applicable can be found here.







