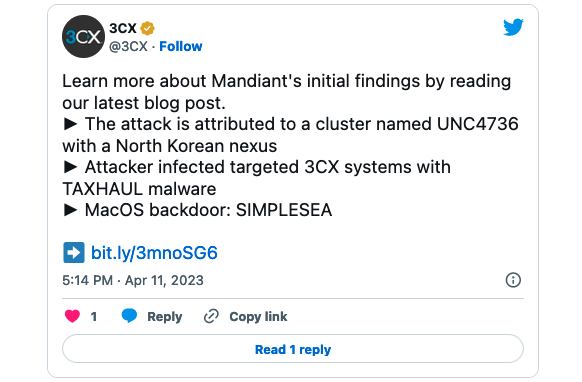
VoIP communications company 3CX confirmed today that a North Korean hacking group was behind last month’s supply chain attack.
“Based on the Mandiant investigation into the 3CX intrusion and supply chain attack thus far, they attribute the activity to a cluster named UNC4736. Mandiant assesses with high confidence that UNC4736 has a North Korean nexus,” 3CX CISO Pierre Jourdan said today.
The attackers infected 3CX systems with malware known as Taxhaul (or TxRLoader), which deployed a second-stage malware downloader named Coldcat by Mandiant.
The malware achieved persistence on compromised systems through DLL side-loading via legitimate Microsoft Windows binaries, making it harder to detect.
Furthermore, it automatically loaded during system start-up on all infected devices, granting the attackers remote access over the internet.
“On Windows, the attacker used DLL side-loading to achieve persistence for TAXHAUL malware. The DLL was loaded by the legitimate Windows service IKEEXT through the legitimate Windows binary svchost.exe,” Jourdan said.
macOS systems targeted in the attack were also backdoored with malware named Simplesea that Mandiant is still analyzing to determine if it overlaps with previously known malware families.
“Supported backdoor commands include shell command execution, file transfer, file execution, file management, and configuration updating. It can also be tasked to test the connectivity of a provided IP and port number,” Jourdan added.
Malware deployed by UNC4736 on 3CX’s network connected to multiple command-and-control (C2) servers under the attackers’ control, including azureonlinecloud[.]com, akamaicontainer[.]com, journalide[.]org, and msboxonline[.]com.
3CX is yet to disclose how the supply chain attack was conducted in the first place, whether its development environment was compromised or through some other method.
Since the attack was first disclosed, Kaspersky also discovered that a backdoor known as Gopuram, used by the North Korean-backed Lazarus hacking group against cryptocurrency companies since at least 2020, was also dropped as a second-stage payload in the same incident onto the compromised devices of a limited number of 3CX customers.
3CX first confirmed its 3CXDesktopApp Electron-based desktop client was compromised in a supply chain attack to deploy malware one day after news of the attack surfaced on March 29 and over a week after customers began reporting the software was being tagged as malicious by security solutions from SentinelOne, CrowdStrike, ESET, Palo Alto Networks, and SonicWall.
The company advised customers to uninstall the impacted Electron desktop client from all Windows and macOS devices (a mass-uninstall script is available here) and immediately switch to the progressive web application (PWA) Web Client App providing similar features.
After the incident (tracked as CVE-2023-29059) was disclosed, BleepingComputer also reported the threat actors exploited a 10-year-old Windows vulnerability (CVE-2013-3900) to camouflage the malicious DLLs bundling the payloads as legitimately signed.
Security researchers have also created a web-based tool to help 3CX users find out if the March 2023 supply chain attack has potentially impacted their IP address.
3CX says its 3CX Phone System is used by over 600,000 companies worldwide and over 12 million users daily, with the customer list including high-profile companies and organizations like American Express, Coca-Cola, McDonald’s, Air France, IKEA, the UK’s National Health Service, and multiple automakers.