5 Common Pitfalls To Avoid In Bug Bounties

Source link
Related Articles
All Mix →[How] Do You Correct Friends Who Have Poor Written English?
I took the serious risk of correcting a friend today (privately, via Twitter DM) in regard to his use of “their/they’re”, and “your/you’re”. I told…
Using Twitter Lists to See How You’re Perceived Online
People often wonder what others think of them. If you use Twitter to any significant degree there’s a simple way to tell: do a tag…
Detectify Crowdsource Monthly Recap | August 2017 Breaks New Records
Table of Contents August marks the best month so far Top finding: URL path traversal due to url-encoded slashes Severe Flash vulnerabilities This month’s CS…
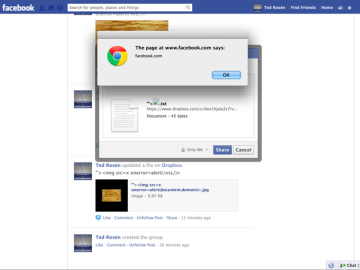
How I hacked Facebook and received a $3,500 USD Bug Bounty
Find out how our Security Researcher Frans Rosén hacked Facebook and found a stored XSS for which he received a bug bounty reward. I recently found…
CORS Misconfigurations Explained – Detectify Blog
Table of Contents How Detectify can help Origin is reflected Insufficient regular expression Allow requests from localhost or 127.0.0.1 Third party hosts Amazon S3 bypass…
My Prediction For Twitter – Daniel Miessler
Created/Updated: November 6, 2022 I’m a bit Elon and Twittered out, but I want to capture a basic prediction about all the shenanigans. As for…
![[How] Do You Correct Friends Who Have Poor Written English?](https://image.cybernoz.com/wp-content/uploads/2025/04/How-Do-You-Correct-Friends-Who-Have-Poor-Written-English.png)