- Key Takeaways
- Why Audit Readiness Still Feels Reactive?
- The Problem: The Gap Between Compliance Activity and Outcomes
- 1. Connect Security Findings to Control Context
- 2. Prioritize the Gaps That Impact Audit Outcomes
- 3. Automate Remediation Workflows
- 4. Leverage Control Mapping Across Frameworks
- 5. Shift to Continuous Audit Readiness
- Modernize Your Audit Readiness Today
- Frequently Asked Questions
- Related

Key Takeaways
- Audit readiness remains reactive in many organizations, even though security and compliance teams generate continuous findings, evidence, and control data across multiple systems.
- The real challenge is the gap between compliance activity and audit outcomes, where large volumes of data still require manual interpretation to become audit-ready insights.
- Connecting security findings to control and asset context helps teams focus on validating controls rather than interpreting raw data.
- Prioritizing gaps based on control impact, asset scope, and risk signals enables organizations to address the issues that meaningfully improve audit readiness.
- Continuous audit readiness integrates control validation, prioritization, and remediation into daily operations, reducing manual audit preparation and improving compliance outcomes.
Why Audit Readiness Still Feels Reactive?
Security and Compliance teams generate continuous findings, evidence, and control data across multiple systems
Yet when an audit approaches, preparation often shifts back to manual coordination. Teams gather information across security, IT, and compliance functions, align evidence to evolving requirements, and assemble what is needed for the audit. Despite ongoing compliance activity, emails, spreadsheets, and ad hoc workflows still become part of the process, especially in large enterprises where audit cycles overlap.
The problem isn’t a lack of configuration checks; it is the gap between ongoing compliance activity and clear audit outcomes. Closing this gap requires rethinking how organizations connect security signals, control validation, and remediation workflows.
The Problem: The Gap Between Compliance Activity and Outcomes
Despite continuous compliance activity, audit readiness often remains reactive. The issue is rarely a lack of data. In fact, most organizations generate more security and compliance information than they can realistically interpret.
Findings are generated across multiple tools, controls are mapped to different frameworks, and evidence is owned by different teams. As environments grow, more technologies fall within audit scope, increasing the number of controls and evidence sources that need to be managed.
This is where the gap emerges. Security and compliance teams spend valuable time deciding which findings require attention, determining priorities, verifying whether evidence is current, and translating technical findings into an audit-ready context. While compliance activity continues throughout the year, converting it into actionable audit outcomes still requires significant manual effort.
Organizations can close this gap by adopting five practical steps that help modernize and operationalize audit readiness.
1. Connect Security Findings to Control Context
The first step in modernizing audit readiness is to recognize that volume does not equal value. Generating billions of findings is meaningless if organizations cannot determine which ones impact their audit posture. This requires moving beyond raw data collection to intelligent interpretation.
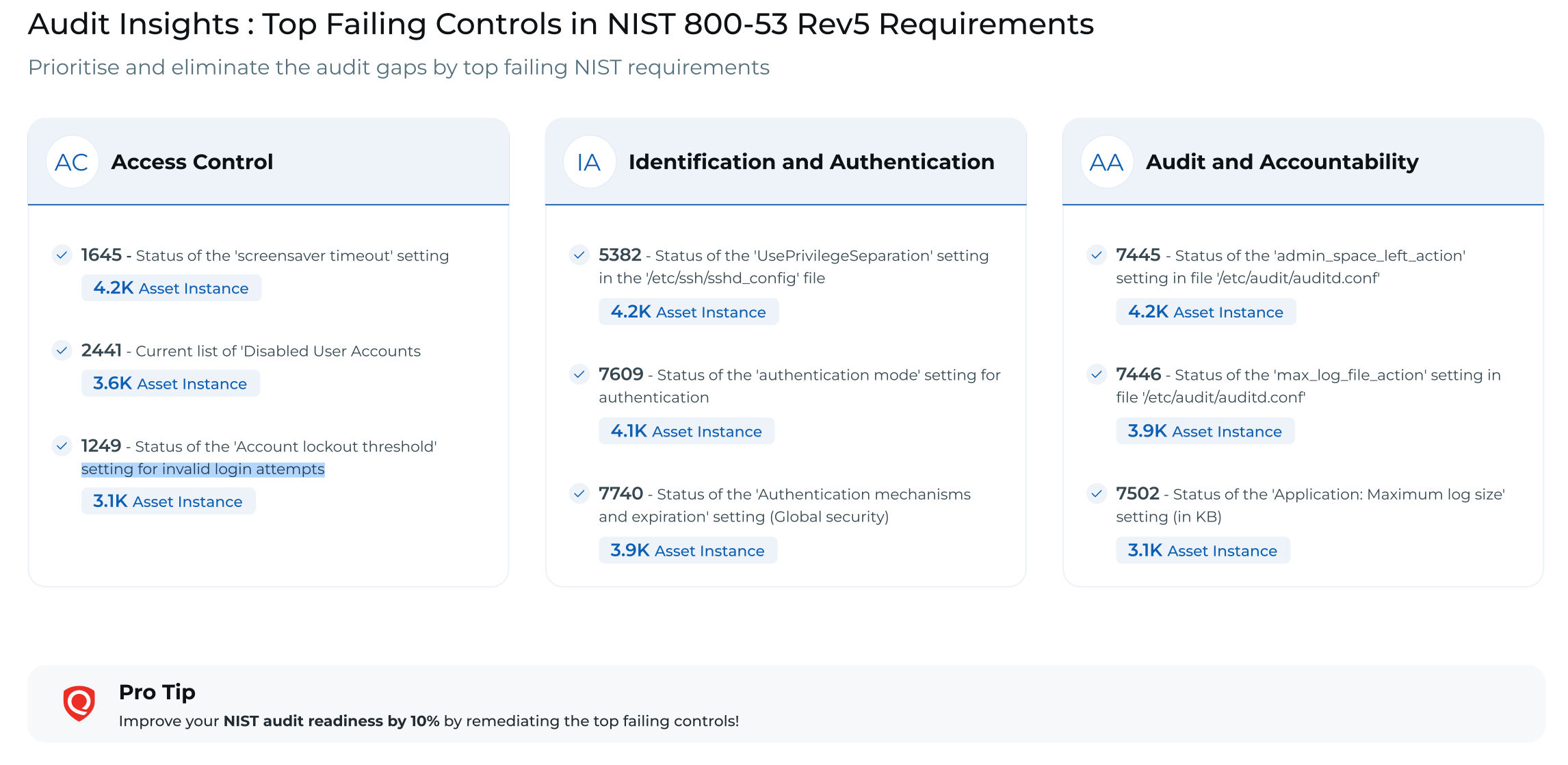
Traditional approaches often stop at configuration assessment and reporting, but modern audit workflows demand more than raw findings. Security and compliance teams need a clear control context, framework mapping, recommended remediation steps, and prioritization based on impact so they can make informed decisions.
Audit preparation should not be a separate effort. Instead, it should be integrated into daily operational workflows. Tools should connect findings directly to the relevant controls and asset context. With pre-mapped findings, teams spend less time interpreting results and more time validating controls.
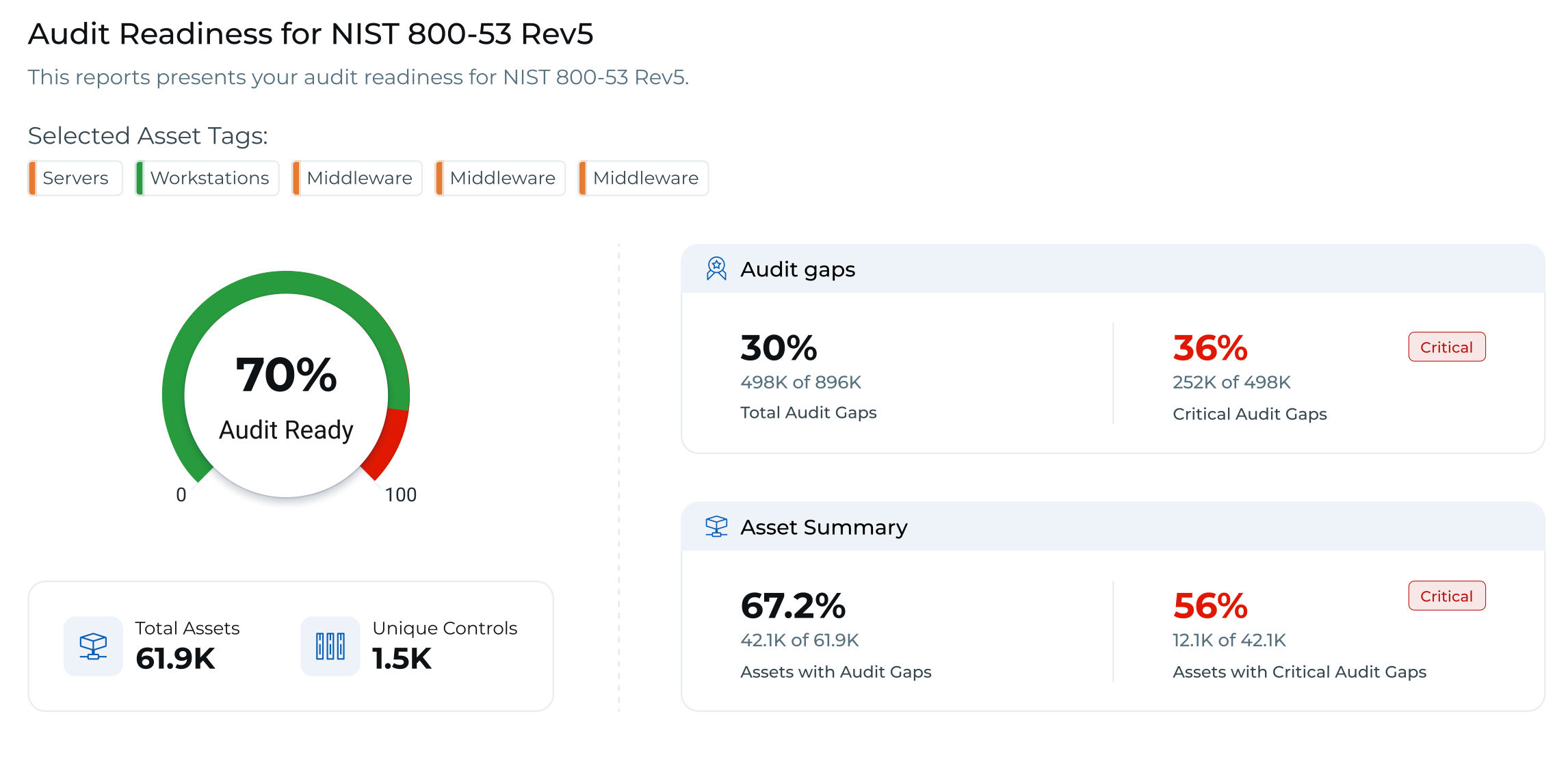
Modern audit readiness platforms like Qualys Policy Audit support this approach by linking findings to control and asset context, automating framework mapping, and enabling risk-based prioritization for remediation. This allows teams to move quickly from insight to action, making audit readiness a continuous part of daily operations rather than a reactive, disconnected effort.
The result is faster, more confident audit preparation and stronger control validation across the environment.
2. Prioritize the Gaps That Impact Audit Outcomes
Even when findings are connected to the control context, organizations still face another challenge: determining which gaps actually require attention.
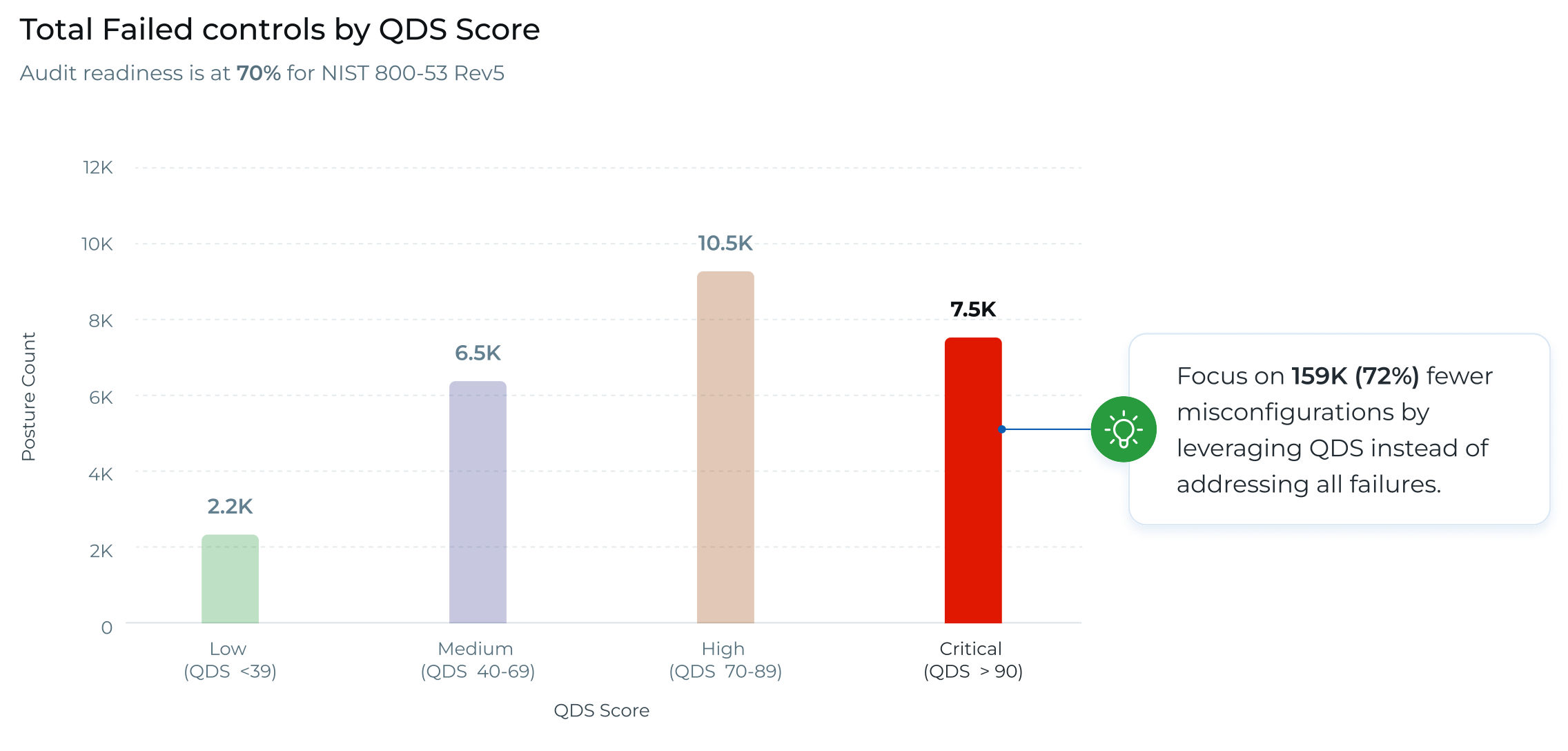
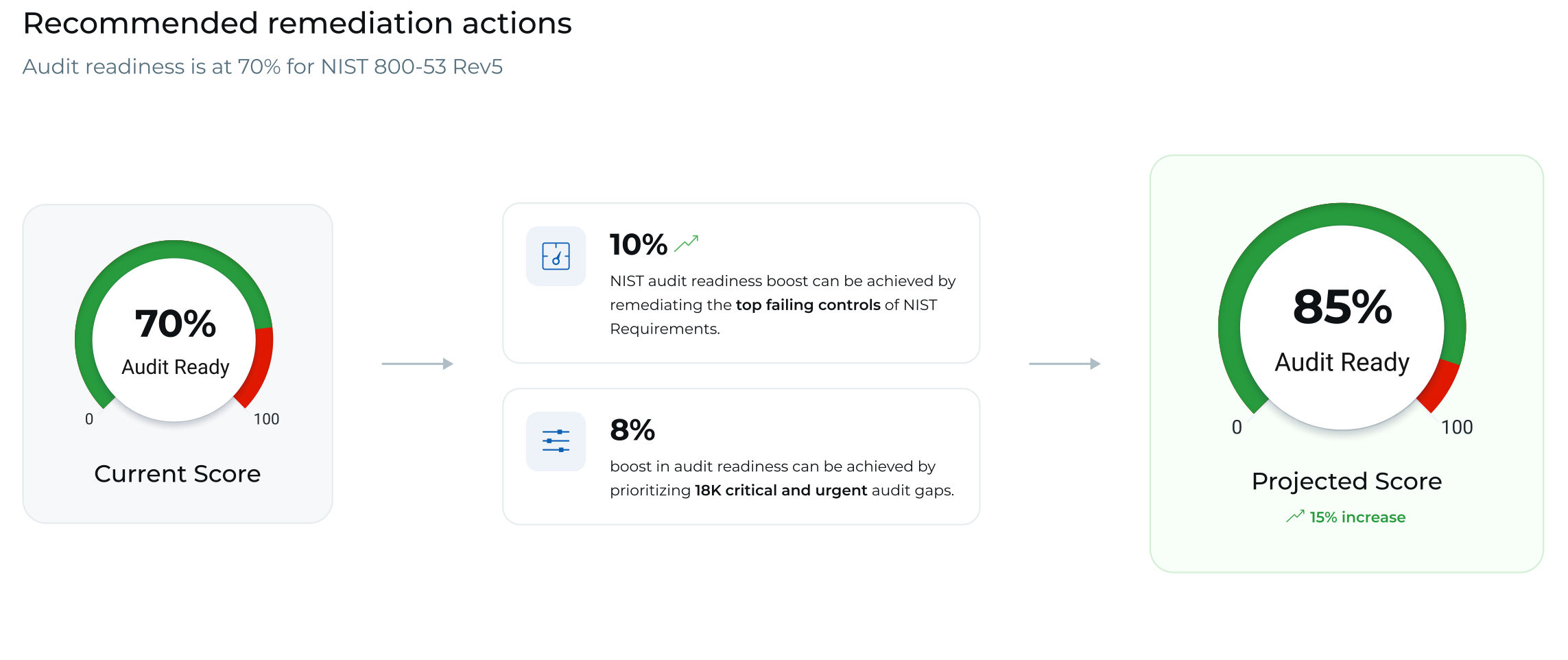
Continuous assessments in large enterprise environments can yield an overwhelming number of findings, yet research shows that fewer than 1% of vulnerabilities pose the highest risk or require immediate action to meaningfully improve audit outcomes. Mature audit workflows focus on control context rather than isolated findings.
Prioritization changes everything when findings are evaluated within a broader security context, including ransomware-related controls, MITRE ATT&CK mappings, and operational risk signals, so teams can clearly identify which gaps have real consequences.
By leveraging control mapping, asset context, and control criticality with pre-built workflows in policy audit, organizations can shift audit preparation from interpretation to validation and execution. This ensures that every action drives meaningful progress rather than simply reducing a number on a dashboard, ensuring remediation efforts improve audit readiness rather than simply reducing findings.
Not all findings carry the same impact. Prioritization changes when findings are evaluated in context. Control criticality, asset scope, and QDS-based risk signals help teams focus effort where it matters most.
As these prioritized gaps are addressed, readiness scores reflect measurable progress rather than static reporting. The result is a remediation process that strengthens audit posture rather than simply reducing the number of findings on a dashboard.
3. Automate Remediation Workflows
Once control gaps are identified and prioritized, the next step is to operationalize audit outcomes by closing the loop between assessment and remediation.
Manual remediation is slow and error-prone. Automation helps ensure that control gaps are addressed consistently as part of ongoing operations.
With Audit Fix, remediation moves beyond recommendations to automated execution workflows that apply policy-aligned remediation across assets. This ensures that prioritized gaps are addressed efficiently and improvements in control effectiveness translate into measurable progress in audit readiness.
4. Leverage Control Mapping Across Frameworks
Performing the same work for every audit is inefficient. Mature audit workflows are built around control context rather than isolated findings. The key is to validate controls once and reuse that validation across multiple compliance frameworks.
When controls are mapped across frameworks and enriched with security context, teams can prioritize controls once and simultaneously improve readiness across multiple mandates Improvements made to a control automatically apply across all mapped frameworks, reducing duplicate effort and simplifying audit preparation
Organizations should identify where the same control is tested repeatedly across frameworks such as SOC 2, ISO 27001, GDPR, and other regulatory mandates. Mapping these controls to a unified framework allows a single validation to satisfy several requirements at once.
Qualys Policy Audit supports this approach by enabling organizations to map controls across frameworks, so improvements to a single control automatically apply to all relevant mandates. This shifts audit preparation from repeatedly gathering evidence to continuously maintaining readiness.
5. Shift to Continuous Audit Readiness
The industry is moving away from audit preparation as a periodic event and toward continuous decision-making built into daily operations. The question is no longer whether organizations have enough findings or reports, but how quickly they can translate security signals into action that improves audit readiness.
As environments expand and mandates evolve, workflows that rely on manual interpretation become increasingly unsustainable. The goal is a model in which prioritization, remediation, and control validation occur continuously, ensuring that audit outcomes reflect the current state of the environment rather than a point-in-time snapshot.
In this model, audit outcomes become part of everyday security operations rather than a separate compliance exercise. Qualys Policy Audit supports this model by connecting control validation, prioritization, and remediation into a continuous audit workflow.
Modernize Your Audit Readiness Today
Audit readiness is no longer about preparing for an event; it is more about operating with clarity. Organizations that embed audit readiness into their daily operations spend less time translating findings and coordinating evidence and more time improving the controls that matter. Efforts shift from periodic preparation to continuous clarity across controls, frameworks, and remediation, and maintaining alignment as environments and requirements evolve.
The result is not just faster audits, but a more predictable and scalable way to manage compliance as part of normal security operations.
Ready to transform your approach? See how Qualys Policy Audit modernizes audit readiness.
Frequently Asked Questions
What is Continuous Audit Readiness?
Continuous audit readiness is a model where prioritization, remediation, and control validation occur consistently as part of daily operations. This approach ensures that audit outcomes reflect the current state of the environment rather than just a snapshot in time. As a result, audit outcomes become intertwined with everyday security operations instead of being treated as a separate compliance exercise.
How to Shift from Checkbox Compliance to a Strategic Capability?
Organizations can transition from checkbox compliance to a strategic capability by linking security findings to their control context, prioritizing the gaps that affect audit outcomes, automating remediation workflows, leveraging control mapping across different frameworks, and embedding audit readiness into continuous operational workflows. This strategy aims to enhance controls and validate changes rather than merely gathering evidence for periodic audits.
Why are Automated Audit Workflows Important in 2026?
Automated audit workflows are essential because manual remediation processes are often slow and prone to errors. As environments grow and regulations evolve, workflows that depend on manual interpretation become increasingly unsustainable. Automation guarantees that control gaps are consistently addressed and that improvements in control effectiveness lead to measurable progress toward audit readiness.
How Does Qualys Policy Audit Support Continuous Compliance?
Qualys Policy Audit facilitates continuous compliance by linking findings to control and asset context, automating framework mapping, enabling risk-based prioritization for remediation, and integrating control validation, prioritization, and remediation into a continuous audit workflow. This helps organizations transition from gaining insights to taking action and maintaining audit readiness as part of their daily operations.
What Frameworks Does Qualys Policy Audit Cover?
Qualys Policy Audit supports mapping controls across multiple frameworks, including SOC 2, ISO 27001, GDPR, and other regulatory mandates.
How to Prioritize Compliance Gaps Effectively?
Compliance gaps can be prioritized by evaluating findings within a broader security context. This includes using control mapping, asset context, control criticality, and risk signals such as ransomware-related controls, MITRE ATT&CK mappings, and QDS-based risk signals. By focusing on gaps with significant consequences, teams can meaningfully improve their audit outcomes.
Related

Source link