Censys has warned that more than 5,000 Rockwell Automation/Allen-Bradley PLCs are currently exposed to the internet as Iranian-affiliated APT actors actively target these devices across U.S. critical infrastructure.
The same operators were previously associated with a November 2023 campaign that compromised at least 75 Unitronics PLCs in U.S. water and wastewater facilities, showing a continuing focus on OT systems.
On April 7, 2026, the FBI, CISA, NSA, EPA, DOE, and U.S. Cyber Command released a joint advisory (AA26-097A) detailing ongoing exploitation of internet-facing Rockwell/Allen-Bradley PLCs by Iranian-affiliated APT actors linked to the IRGC Cyber Electronic Command, including the group tracked as CyberAv3ngers.
The current activity, observed since at least March 2026, relies on legitimate Rockwell tooling such as Studio 5000 Logix Designer to connect directly to exposed PLCs, modify project files, and manipulate HMI/SCADA display data without exploiting zero‑day vulnerabilities.
Confirmed targets include CompactLogix and Micro850 families, and agencies warn that concurrent probing of Modbus and Siemens S7 traffic suggests broader multi‑vendor targeting.
5,219 Rockwell/Allen-Bradley PLCs Exposed
Censys telemetry shows 5,219 internet-exposed hosts responding on EtherNet/IP (port 44818) and self-identifying as Rockwell Automation/Allen‑Bradley devices, matching the attack surface in scope for AA26‑097A.
The United States accounts for 74.6% of that exposure 3,891 hosts reflecting Rockwell’s dominant footprint in North American industrial automation.
Outside the Anglosphere, Spain (110), Taiwan (78), and Italy (73) stand out. At the same time, Iceland’s 36 exposed devices are notable given its small population and heavy use of industrial control systems in geothermal energy.
The sectors most at risk include government services, water and wastewater systems, and energy, all of which commonly deploy Rockwell PLCs in production environments.
ASN analysis reveals that nearly two‑thirds of exposed Rockwell PLCs sit on consumer and business cellular networks rather than industrial or datacenter providers.
Verizon Business (CELLCO‑PART) alone hosts 2,564 exposed PLC endpoints 49.1% of the global total while AT&T Mobility adds 693 more, or 13.3%.
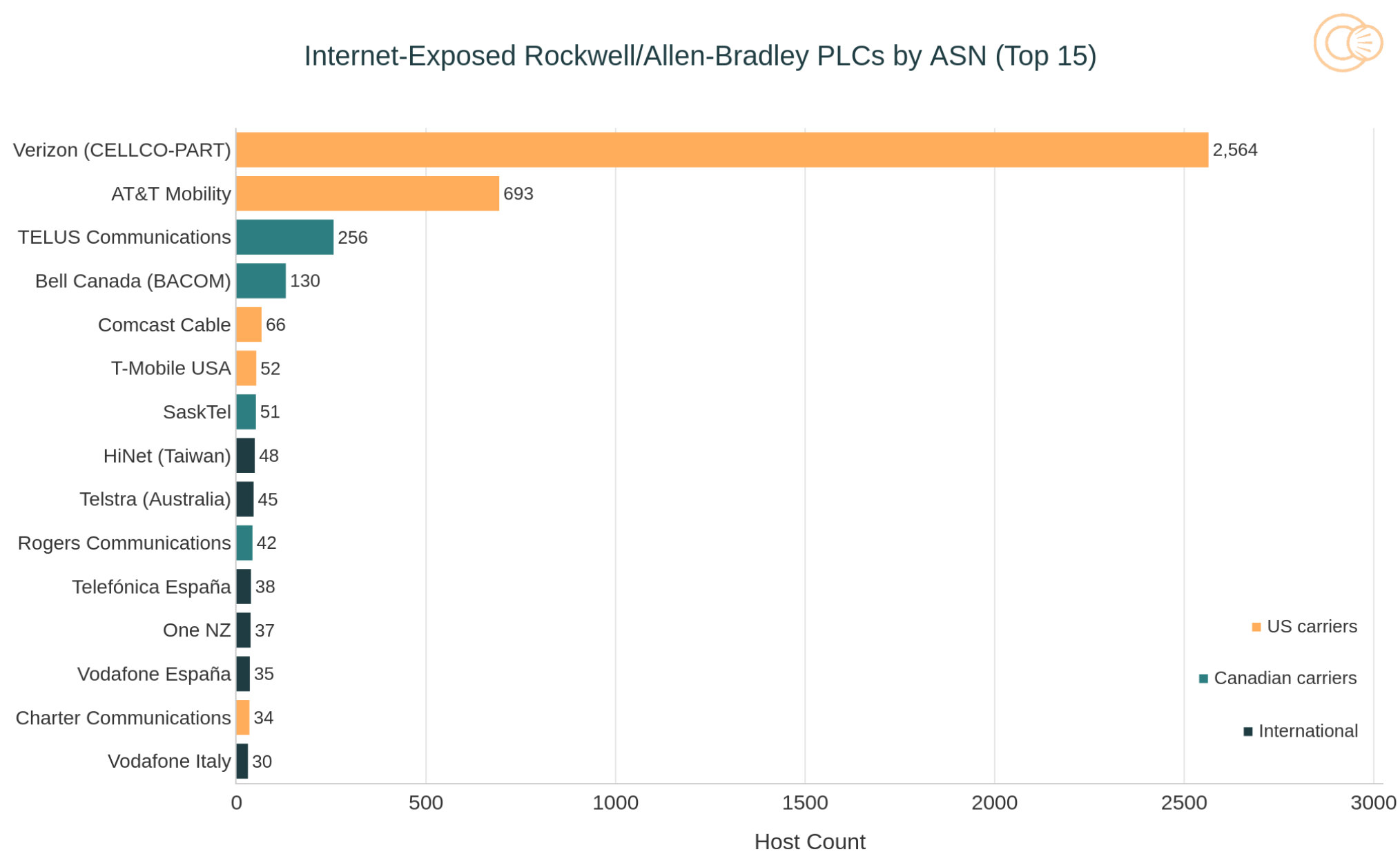
This pattern strongly indicates that many of these controllers are field‑deployed assets, such as pump stations and remote municipal sites, reachable only through cellular modems that have been placed directly on the public internet.
Censys also notes a smaller but important cluster on SPACEX‑STARLINK (24 hosts), highlighting growing exposure of satellite‑connected OT endpoints that are harder to monitor and patch.
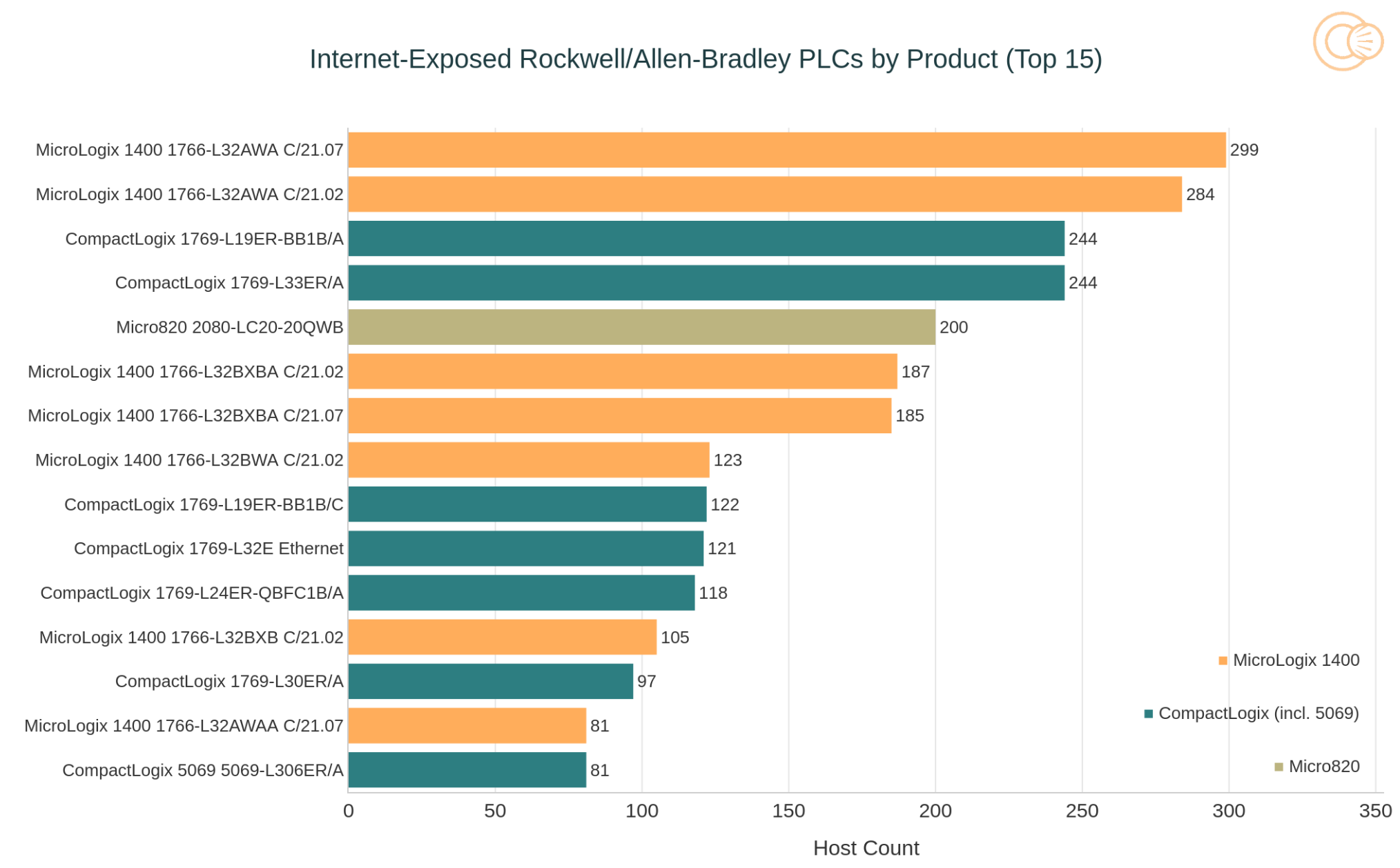
Unauthenticated EtherNet/IP identity responses allow attackers to fingerprint PLC models and firmware versions, and the exposed population is dominated by MicroLogix 1400 and CompactLogix devices.
Many MicroLogix 1400 controllers appear to be running end‑of‑sale firmware builds (such as C/21.02 and C/21.07), creating a persistent pool of legacy, lightly supported devices that adversaries can easily identify and prioritize.
Censys also observes extensive co‑exposure of additional services on the same hosts or networks, including VNC (771 instances), Telnet (280), Modbus (292), and Red Lion Crimson services (256).
These services expand the attack surface by providing potential direct access to HMI workstations, legacy remote shells, and multi‑vendor OT management interfaces, aligning with the advisory’s warning about multi‑protocol probing and HMI/SCADA manipulation.
Operator Infrastructure Behind the Campaign
The CISA advisory includes eight IP indicators, but Censys infrastructure pivot significantly refines this picture.
Seven of the IOCs in the 185.82.73.x range resolves to a single multi‑homed Windows engineering workstation in AS214036 (ULTAHOST), running the full Rockwell toolchain and exposing RDP on a non‑standard port with a shared self‑signed certificate referencing the hostname DESKTOP‑BOE5MUC.
Historical certificate analysis ties 11 IPs in the same /24 to that workstation, revealing four additional operator IPs that are not listed in the advisory yet share identical fingerprints and activity windows.
In contrast, the eighth IOC, 135.136.1.133 in AS9009 (M247 Romania), behaves as a short‑lived staging box provisioned for a single operation, with a tightly scripted service lifecycle that matches the March attack window.
Agencies and researchers are urging asset owners to immediately disconnect Rockwell PLCs from direct internet access and route all remote connectivity through secured, monitored gateways such as VPNs or jump hosts.
Recommended steps include locking down or eliminating services like Telnet, VNC, and exposed web interfaces, enforcing strong authentication on cellular and satellite links, and maintaining offline, tested backups of PLC configurations and HMI/SCADA projects.
With thousands of Rockwell/Allen-Bradley PLCs still visible on the public internet and active Iranian-linked operations targeting them the advisory and Censys data together underline that this is not a theoretical risk but an ongoing OT threat with real-world operational and safety implications.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.





