- Recorded Future is now offering four solutions covering cyber operations, digital risk protection, third-party risk, and payment fraud.
- Three tiered packages (Core, Professional, Elite) bundle these solutions to scale with an organization’s security program.
- Packages include unlimited users and integrations so intelligence reaches everyone who needs it.
The global threat landscape didn’t simplify in 2025. It shattered. Recorded Future’s Insikt Group® 2026 State of Security documented how geopolitical fragmentation, state-sponsored operations, and criminal ecosystem adaptation reshaped global risk. Threats that once stayed in distinct lanes converged, and they converged fast.
Consider what Insikt Group® tracked last year:
- State-sponsored cyber actors shifted from intelligence collection to persistent access, pre-positioning inside target infrastructure so they can disrupt operations the moment geopolitical tensions escalate.
- Weak governance and systemic corruption fueled industrialized cybercrime, enabling payment fraud and criminal operations to scale like legitimate businesses.
- Influence operators and hacktivist groups multiplied alongside rising interstate conflict, amplifying fear, uncertainty, and doubt through exaggerated exploit claims.
- Loosely organized criminal collectives used social engineering to compromise third-party SaaS platforms, rapidly adapting to law enforcement action and traditional defenses alike.
The risk surface has expanded well beyond networks and endpoints. Your brand, your third-party vendors, your payment networks: each has its own threat actors, its own attack methods, and its own intelligence requirements. Yet most intelligence programs only cover one of these domains. Or they monitor them in silos, with no shared context.
The right intelligence, from the right sources, at the right time, is a critical competitive advantage. But intelligence only matters if you can act on it across every critical risk domain before attackers reach their objective.
Re-Imagining How Intelligence Is Delivered And Operationalized
Historically, Recorded Future has been sold on a per-user and per-capability basis – a model that worked well in a simpler world where security teams were focused on solving the most urgent problem in front of them.
Today’s threat landscape is fast, more complex, and deeply interconnected. Customers are no longer looking for point solutions, they’re asking for a fundamentally different way to consume and operationalize intelligence.
Customers are asking us to provide:
- Complete capabilities to support use cases aligned with core risk domains.
- Democratized access to intelligence across teams, workflows and systems.
- A simplified and predictable way to purchase for ease of budgeting and adoption.
In response, we’ve re-imagined Recorded Future is delivered:
“Four Solutions. Three Packages. One Intelligence Foundation.”
A unified approach designed to scale with your organization, accelerate time to value, and embed intelligence into every decision that matters.
Four Solutions for Four Critical Risk Domains
Your threats span your infrastructure, your brand, your vendors, and your payment networks. Your intelligence should too. We’ve re-organized our platform into four purpose-built solutions tied to distinct domains of enterprise risk.
Cyber Operations gives your security team the intelligence, workflows, and autonomous actions to detect, investigate, and respond to threats targeting your infrastructure. Alert triage, real-world vulnerability prioritization, malware analysis, proactive hunting: this is where reactive firefighting becomes predictive, intelligence-led defense.
Digital Risk Protection helps detect and disrupt threats that never touch your network but directly damage your business: brand impersonation, domain abuse, credential leaks, and phishing infrastructure across the open, deep, and dark web. With access to active infostealer logs and automated IAM remediation, your team can act on exposures within hours, not weeks.
Third-Party Risk delivers continuous, intelligence-driven monitoring of your vendor ecosystem. Security ratings combined with real-time threat intelligence surface breaches, ransomware activity, and dark web exposure days or weeks before formal vendor notification, giving your security and GRC teams evidence they can act on and defend to stakeholders.
Payment Fraud Intelligence identifies stolen payment cards, compromised checks, scam merchants, and web-skimming activity earlier in the fraud lifecycle, so financial institutions can stop losses before they materialize.
Each solution delivers complete, end-to-end capability for its risk domain. And because all four run on the same Intelligence Graph®, a signal detected in one domain immediately enriches context across the others.
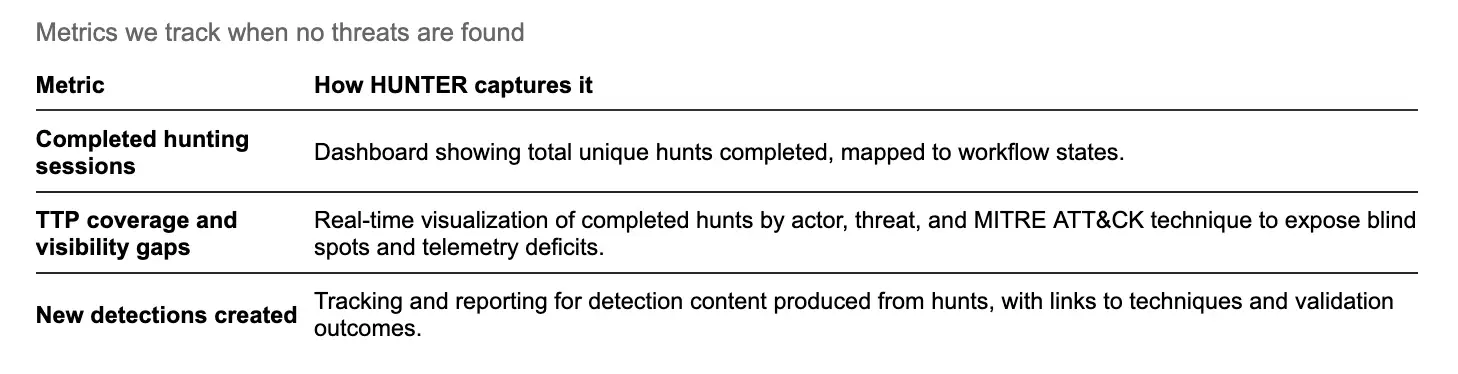
Three Packages That Scale With Your Program
Modern organizations operate across multiple risk domains. We are introducing three packages that reflect that reality, meeting customers where they are and scale as their programs mature.
- Core is the foundation for intelligence-led security. It enables organizations to tackle essential use cases on day one – threat detection and alert triage, vulnerability monitoring, credential exposure detection, domain abuse monitoring, and executive impersonation protection. The package combines capabilities across Cyber Operations and Digital Risk Protection solutions, providing immediate, high-impact coverage.
- Professional is built for organizations ready to mature their program and operationalize intelligence at scale. Building on Core, it introduces deeper insights and automation to extend team capacity – enabling autonomous threat hunting, multi-source correlation, and external asset discovery. The result is broader coverage, faster response, and more leverage for security teams without adding headcount.
- Elite delivers the most comprehensive intelligence coverage available. By unifying Cyber Operations, Digital Risk Protection, and Third-Party Risk, it provides a complete view of risk across infrastructure, brand, and supply chain. With a single pane of glass, Elite operationalizes intelligence across workflows and teams—from CTI to SOC to Risk—driving smarter and faster risk-enabled decision making and response.
Across all packages, customers get full access to the Intelligence Graph®, Recorded Future AI, all compatible integrations, APIs, and Collective Insights. No hidden costs or barriers to connect to your existing security stack.

Built for Everyone Who Needs Intelligence, Not Just Analysts
Intelligence only creates value when the right people can act on it. That’s why our platform packages include unlimited users. Every analyst, every engineer, every stakeholder who needs intelligence gets it, with no seat limits and no trade-offs about who gets access.
For smaller teams building early-stage programs, we still offer flexible user-based licensing so you can start where it makes sense and expand as your program matures. Either way, pricing is predictable. You know what you’re paying, and you can scale with confidence.
Every package also includes unlimited integrations from Recorded Future’s hundreds of supported applications at no additional cost. Your SIEMs, EDRs, SOAR platforms, and ticketing systems all get equipped with real-time intelligence, so every analyst and engineer working in those tools benefits from enriched context without switching screens. Add Autonomous Threat Operations, and those same integrations become the foundation for autonomous hunting, detection, and prevention across your entire stack. Connected tools become an intelligence-led defense system that acts continuously, with minimal human intervention.
One Intelligence Foundation Across Every Domain
What makes this approach powerful isn’t just simpler packaging. All four solutions and all three packages run on the same intelligence foundation: the Intelligence Graph®, correlating over 1.2 million sources and 26 billion entities across cyber, digital, third-party, and fraud domains.
A credential leak detected in Digital Risk Protection immediately informs a Cyber Operations investigation. A vulnerability under active exploitation triggers prioritized patching in your workflow. A third-party vendor breach surfaces before the vendor discloses it. Intelligence flows across your entire risk surface, giving you the correlated, high-confidence context that point solutions can’t deliver.
That’s what it means to be intelligence-led. Not consuming more data. Connecting signals across domains so you can act earlier, with greater confidence, at machine speed.
The Path Forward
Adversaries in 2026 are faster, more coordinated, and more resourceful than they’ve ever been. They operate across every attack surface simultaneously, and they’re accelerating.
Whether you’re a team of three building your first intelligence program or a global enterprise running intelligence-led autonomous operations, there’s a clear path. Start with the solution or package that matches your priorities today. Grow into deeper automation and broader coverage as your program matures. And at every step, you’re backed by the most comprehensive and independent intelligence platform in the industry.
We built this for the threats you’re facing right now, and the ones coming next.