- Pre-Penetration Test Considerations
- Scoping
- Timelines
- Choosing the right method
- Pen Testing Team: In-House versus External
- Reporting & Deliverables
- Stakeholder Buy-in
- During the Penetration Test
- Post Pen Testing Review, Risk Analysis and Recommendations
- Keeping Up with New and Evovling Threats
- Hot Tips – Quick Takeaways
- Penetration Testing as a Service (PTaaS)- The Best of Both Worlds?
The frequency and complexity of cyber threats are constantly evolving. At the same time, organizations are now collecting sensitive data that, if compromised, could result in severe financial and reputational damage. According to Cybersecurity Ventures, the cost of cybercrime is predicted to hit $8 trillion in 2023 and will grow to $10.5 trillion by 2025.
There is also increasing public and regulatory scrutiny over data protection. Compliance regulations (such as PCI DSS and ISO 27001), as well as the need for a better understanding of your cybersecurity risks, are driving the need to conduct regular penetration tests.
Pen testing helps to identify security flaws in your IT infrastructure before threat actors can detect and exploit them. This gives you visibility into the risks posed by potential attacks and enables you to take swift corrective action to address them. Here, we outline key factors to consider before, during, and post the penetration testing process.
Pre-Penetration Test Considerations
It’s important to understand the ‘why’ behind the need for a penetration test. Different compliance regulations necessitate different types of tests and report formats.
Scoping
Careful scoping is an essential step in identifying the key areas to be tested. This includes determining the systems, networks, and applications in your environment that could potentially be targeted. Your scoping decision will significantly impact the pen testing process’s efficiency and efficacy, and it should align with your overall business objectives and security requirements. Having a clearly defined scope helps ensure nothing is missed, and the company conducting the tests appreciates a well-defined scope to avoid “scope creep.”
Timelines
Pen testing isn’t an overnight process. It requires careful planning, execution, and review. From the initial consultation to vulnerability scanning, simulated attacks, and a thorough review, every stage requires adequate time allocation. A well-laid timeline can ensure smooth execution and immediate remediation.
Remember, haste can make waste – rushing a pen test could leave you vulnerable to cyber threats.
Choosing the right method
Next, you’ll need to determine how the tests will be conducted. There are primarily three options:
- Blackbox: The pen testing team is given no details or assistance.
- Whitebox: The pen testing team is given full disclosure about your systems, and possibly assistance.
- Greybox: A hybrid approach, where external tests might be conducted as a ‘blackbox’, and internal tests as a ‘whitebox’.
Pen Testing Team: In-House versus External
You can either build an in-house team or outsource to an external agency.
While an in-house team can provide a detailed understanding of your specific environment, external agencies offer broader expertise and an outsider’s perspective. Consider factors like cost, expertise, and resource availability when making this decision.
It’s crucial to ensure you’re comparing like-for-like services when deciding between external vendors offering penetration testing. A simple scorecard could be beneficial in determining whether potential suppliers can answer your specific needs.
Reporting & Deliverables
If you have specific requirements for the report format, be sure to communicate this properly to the partner conducting the tests. Will a technical report suffice, or do you might need a non-technical report for other stakeholders? Ensure you specify any special requirements you might have.
Stakeholder Buy-in
Garnering stakeholder buy-in is critical for the success of your pen testing process. Stakeholders need to understand the importance of pen testing and its contribution to the overall cybersecurity strategy. Clearly communicate the process, potential risks, and anticipated benefits to ensure everyone is on board.
During the Penetration Test
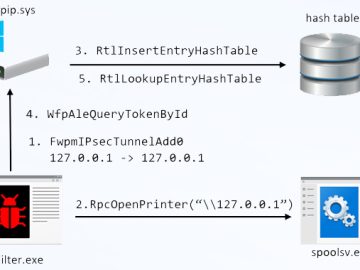
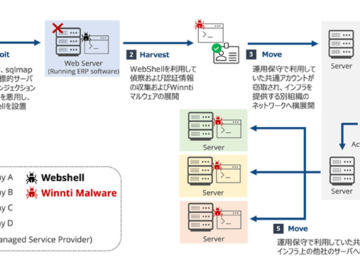
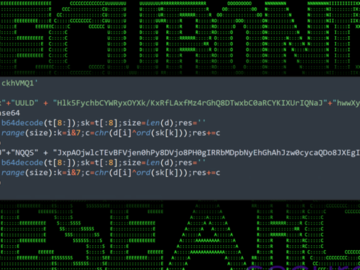
During pen testing, various techniques and tools are used to discover vulnerabilities. The purpose of this exercise is to evaluate the effectiveness of your existing security measures, identify vulnerabilities, and enhance incident response capabilities.
- Scanners: These are automated tools designed to scan your systems for known vulnerabilities. Scanners help identify weaknesses and potential entry points that attackers could exploit. By conducting comprehensive scans, you gain valuable insights into the security posture of your systems.
- Red Team: Mimics the tactics, techniques, and procedures employed by real attackers, attempting to breach your system’s defenses.
- Blue Team: On the other hand, the Blue Team assumes the role of your internal security, defending against these simulated attacks.
The scanners provide automated vulnerability detection, while the Red Team/Blue Team exercise simulates real-world attack scenarios, allowing you to assess the readiness and resilience of your defenses. Together, these components provide a holistic view of your system’s strengths and weaknesses, enabling you to implement targeted security improvements.
Typically, pen tests take an average of 4-6 weeks to complete. Communication between you and your pen testers throughout the entire engagement is vital for a successful test, ensure that you are involved throughout the process, from scheduling to post-test review.
Post Pen Testing Review, Risk Analysis and Recommendations
Once the test is completed, you’ll need to thoroughly review your risk analysis report and determine which vulnerabilities need immediate attention. The report should also include a detailed action plan of recommendations for remediating any identified issues. Depending on your risk tolerance level, some issues might require an immediate fix, while others can be addressed over time.
Make sure you know your security team members who are responsible for implementing the recommended actions and when they need to be completed. This helps ensure that all identified vulnerabilities and threats are addressed promptly.
Keeping Up with New and Evovling Threats
Finally, staying current on the latest trends and attacking techniques is the key to continuous security. Be sure you and your team are well informed of the latest threats as well as best practices in cybersecurity. Keeping up with emerging threats and vulnerabilities can help ensure that you are adequately protected against possible cyber attacks.
Hot Tips – Quick Takeaways
Finally, here are some hot tips to guide you through your pen-testing journey:
- Prioritize: Not all vulnerabilities are created equal. Understand the potential risk each poses and prioritize them accordingly.
- Fix: It’s not enough to identify vulnerabilities. Makes sure your remediation game is on-point.
- Test Regularly: The cyber threat landscape is constantly evolving.
Penetration Testing as a Service (PTaaS)- The Best of Both Worlds?
Organizations are increasingly opting for Penetration Testing as a Service (PTaaS) over traditional pen testing due to several key advantages. PTaaS:
- Offers real-time vulnerability detection and continuous monitoring – ensuring that vulnerabilities are identified promptly and remediated in a timely manner.
- Leverages automated scanning and manual testing – providing comprehensive coverage and accurate vulnerability findings.
- Provides access to security experts, zero false positives, instant notifications, and streamlined report distribution.
- Eliminates the logistical challenges associated with traditional pen testing, such as time constraints and delayed results.
Overall, PTaaS offers a more efficient, flexible, and proactive approach to application security, making it an attractive choice for organizations seeking robust and up-to-date protection against evolving cyber threats.
Penetration testing is an integral part of a solid cybersecurity strategy, offering valuable insights into your system’s vulnerabilities. With Outpost24’s PTaaS solution, you can quickly identify, verify and remediate any potential security issues, enabling your organization to stay ahead of the curve when it comes to cyber threats.