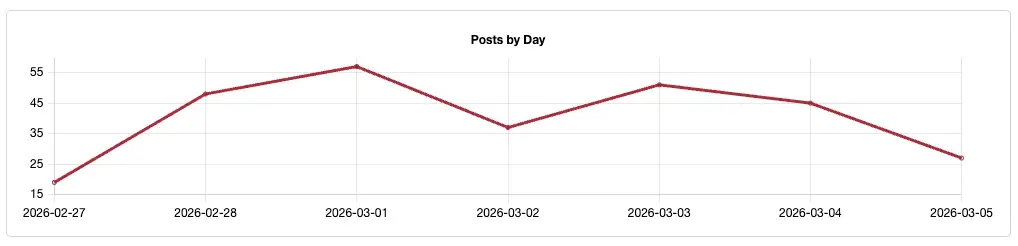
The 2026 Threat Detection Report is here, arming you and your team with actionable insights into the year’s most prevalent security trends, threats, and MITRE ATT&CK® techniques. Our eighth annual retrospective presents an in-depth analysis of more than 110,000 threats detected across over 4.5 million identities, endpoints, and cloud assets over the past year. This report provides you with a comprehensive view of this threat landscape, along with practical guidance on detection, testing, prevention, and mitigation.
Key findings
As the technology that we rely on to conduct business continues to evolve, so do the threats that we face. Here are some of our key findings:
- AI threats materialize in two ways: Adversaries using AI to develop threats and adversaries attempting to compromise corporate AI systems
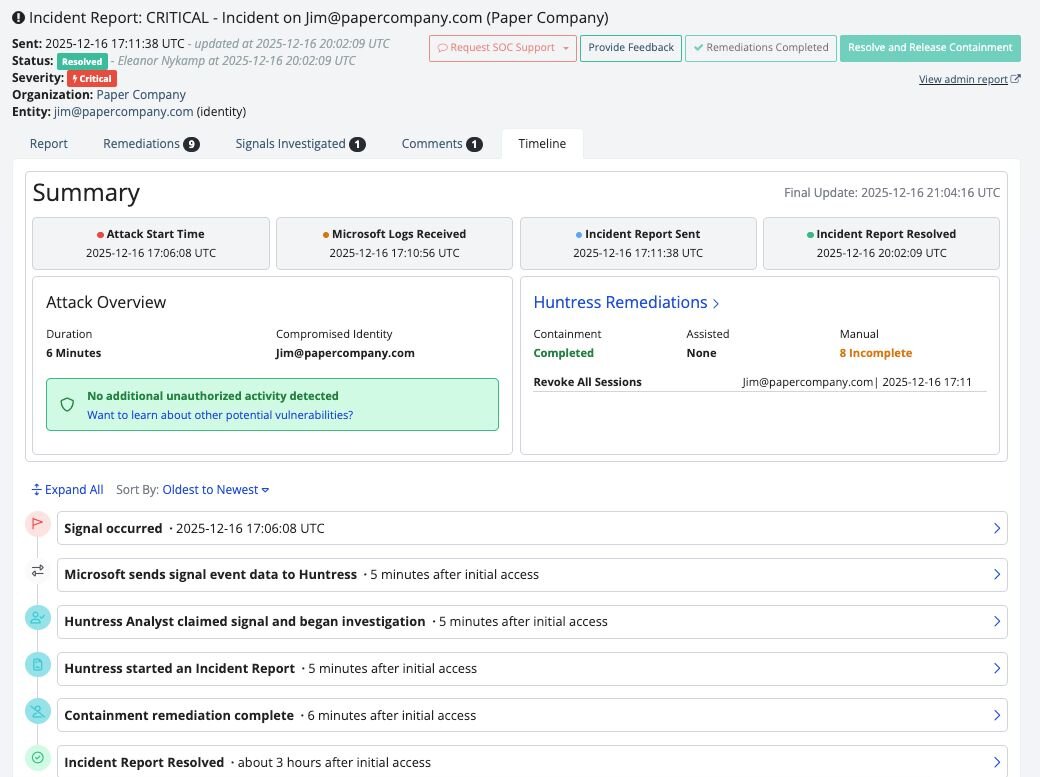
- Cloud account compromises continue to soar, and we detected more identity threats than ever.
- Browsers continue to be a critical focal point for adversaries and defenders alike. In addition to targeting information stored within browsers, adversaries commonly deliver payloads via browsers as well.
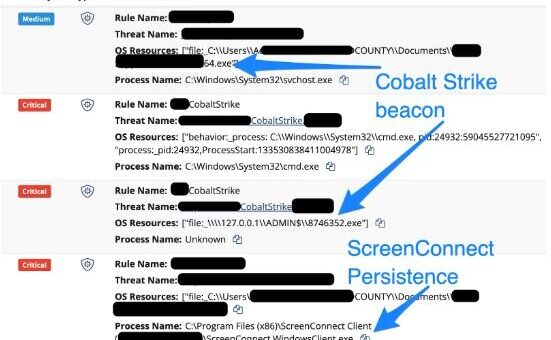
- RMM tools have become the payload of choice for a wide variety of differently motivated adversaries, and are often the payload that follow paste-and-run campaigns.
We also check back on the timeless threats and techniques that are prevalent year-after-year, and explore emerging ones that are worth keeping an eye on. Our Field Guide to Color Bird Threats has been updated with the latest sightings of Red Canary-named threat clusters.
Trends
Since its inception eight years ago, The Threat Detection Report has been anchored by data-driven insights into the most prevalent adversary behaviors we witness on a daily basis. The Trends section allows us to zoom out from our top 10 lists to highlight developments in adversary tradecraft and other patterns that we anticipate making waves in the coming year.

This year’s report covers the AI landscape from two different perspectives: AI-powered threats and threats to AI infrastructure.
We also cover supply chain compromises, infostealers, RMM tool abuse, and much more.
Threats
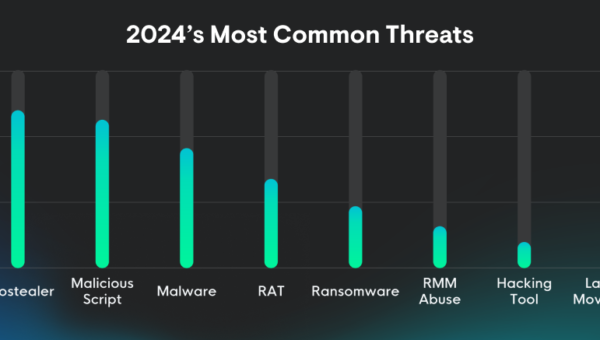
Our top 10 threats list demonstrates how adversaries have shifted their operations to the browser, with the majority of the top threats either executing from the browser or stealing information stored in it. Most of these threats also employed the increasingly popular paste-and-run technique at some point in 2025.
Half of our top 10 threats are new to the rankings this year, including two trojans that execute malicious commands while also delivering on what they claim to do: JustAskJacky and Tampered Chef.
Two Red Canary-named threats updated their tradecraft significantly in 2025, including number 1 Amber Albatross and number 6 Scarlet Goldfinch.


In addition to the top 10, we also share analysis for featured threat CleanUpLoader.
Techniques
Cloud Accounts tops our list of most prevalent techniques for the second year in a row, thanks to increased attention from adversaries and defenders alike. New to the top 10 list are Data From Cloud Storage and Malicious Copy and Paste (aka paste and run or ClickFix).
Rarely do more than two or three net new techniques make into our top 10 technique list. Over the last five years, we’ve detected at least one of the 10 most prevalent techniques in 46 percent of all detections. Over the same time period, we detected at least one of the top 20 techniques in 63 percent of detections.
By focusing on these “forever techniques,” you can virtually cut your organization’s risk in half.


In addition to the top 10, we also share analysis for the Steal Application Access Token technique, which encompasses the many varieties of OAuth content attacks we’ve seen in the wild.
Explore our new Threat Detection Library
Thousands of defenders visit the Threat Detection Report website all year round, implementing the detection opportunities and mitigation guidance as they run into malicious behaviors in their environments. Our new Threat Detection Library makes it even easier to search for threat and technique pages in a central hub.
Get started
The Threat Detection Report is both a timely read and an evergreen resource that practitioners refer to throughout the year. The web version of the report includes even more technical details into visibility, collection, detection, and testing, with actionable guidance should you run into this behavior in your environment.


If you’re intimidated by the PDF’s page count, don’t fret–the Executive Summary provides high-level takeaways for security leaders and any one else who’s short on time. To kick things off, we encourage you to flip through the report, share it with your team, and start a discussion about which threats and techniques should be prioritized in your organization’s threat model.