A large-scale malware operation abusing GitHub to deliver a custom LuaJIT-based trojan to developers, gamers, and everyday users through convincing but trojanized repositories.
The campaign, tracked as “TroyDen’s Lure Factory,” spans more than 300 delivery packages and uses AI-assisted lures ranging from OpenClaw deployment tools to game cheats, Roblox scripts, crypto bots, VPN crackers, and a Telegram-promoted phone tracker.
The centerpiece of the campaign is a fake repository, AAAbiola/openclaw-docker, posing as a Docker deployment helper for the legitimate OpenClaw AI project.
The repo looks credible: it reuses the real upstream OpenClaw source, ships functional Dockerfiles and install scripts, includes multiple listed contributors, and even has a matching GitHub Pages site and SEO-optimized tags such as ai-agents, docker, openclaw, LLM, and security.
To further boost trust, the operator, using the TroyDen persona, seeded stars and forks from throwaway accounts to manufacture social proof before quietly inserting the malicious Diatrymiformes directory under an innocuous “Update README.md” commit.
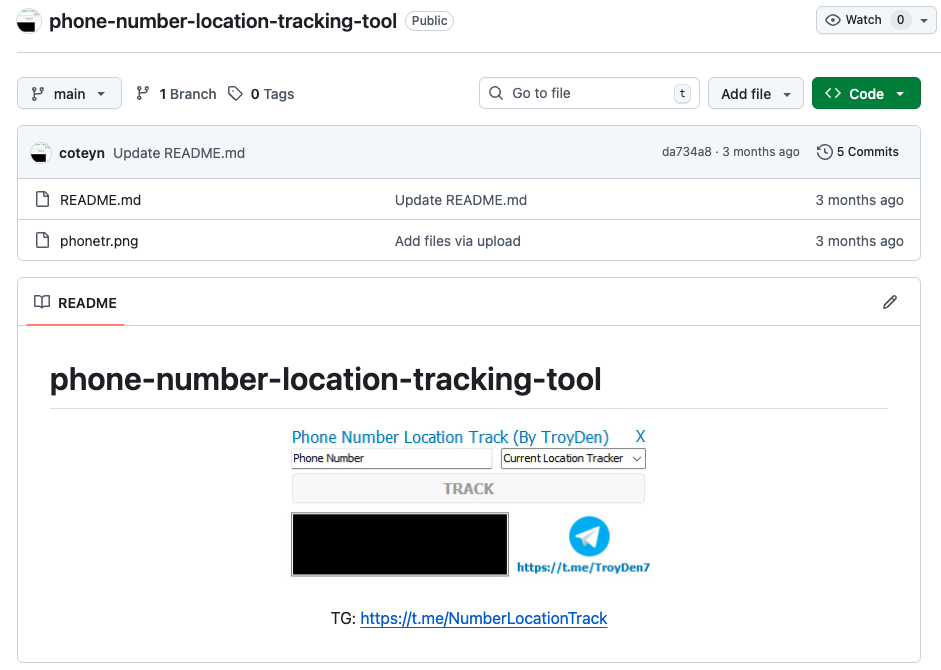
The same 771 KB trojanized binary from this OpenClaw deployer resurfaces in other lures, including a “phone-number-location-tracking-tool” repo and a “fishing-planet-enhanced-menu” cheat, all of which rotate their active payload links in lockstep.
Netskope Threat Labs identified a link to a malware campaign operating across at multiple GitHub repositories, spanning over 300 delivery packages, including an OpenClaw deployment.
Across the broader cluster, lure names mix tool-like labels with obscure biology, Latin, and medical terms (for example, Diatrymiformes and Chelydridae), a pattern that strongly suggests AI-generated naming rather than manual curation at scale.
This mirrors earlier research on AI-assisted fake GitHub repositories used to spread LuaJIT loaders and infostealers such as Lumma Stealer.
AI-Driven OpenClaw Trap
At the core of TroyDen’s toolchain is a two-component LuaJIT loader designed explicitly to defeat automated analysis.
Victims download a ZIP whose Launch.bat simply runs unc.exe with license.txt as an argument, where unc.exe is a stripped LuaJIT 2.1 interpreter and license.txt is an encrypted, Prometheus-obfuscated Lua payload.
Submitted separately, each file appears low-risk: the interpreter looks like a generic Lua runtime and the script resembles opaque data, enabling the pair to slip past many static and behavioral sandboxes that analyze files in isolation.
Earlier variants used a more obvious lua.exe filename, but the current 1.8 payload hides behind the generic unc.exe name while retaining the same behavior.
Once executed together, the script performs five anti-analysis checks, including debugger detection, low-RAM and short-uptime filters, privilege checks, and hostname inspection, before invoking a Sleep call equivalent to roughly 29,000 years to exhaust time-limited sandboxes.
Netskope analysts bypassed this by patching the sleep, revealing that, in real environments, the malware completes its core activity in under thirty seconds.
This design matches a growing family of Prometheus-obfuscated LuaJIT loaders documented since 2024, which use similar anti-tamper tricks, FFI-based Windows API calls, and screenshot-first beacons, especially in gaming-focused campaigns.
As soon as the anti-analysis checks pass, the payload turns off WinINet proxy auto-detection via four registry edits to sidestep corporate inspection proxies, then performs a geolocation lookup through ip-api.com to record the victim’s IP, country, and ISP.
It immediately captures a full desktop screenshot as a 24‑bit BMP and uploads it over HTTP via multipart/form-data to a command-and-control (C2) server hosted on Frankfurt infrastructure, using a hardcoded multipart boundary and static filename field across all observed executions.
The binary distributed by AAAbiola/openclaw-docke” also appears in a second GitHub repository: mikenob39wang/phone-number-location-tracking-tool, which advertises a tool claiming to extract GPS coordinates from a phone number.
The C2 responds with JSON containing encrypted tasks and loader blobs, which are saved into the user’s Documents folder, with additional nodes fronted by nginx load balancing to provide at least eight active HTTP endpoints on the same ASN.
Dynamic analysis shows the loader brings in DPAPI and advapi32 crypto APIs at startup, behavior consistent with browser credential harvesting and aligned with prior LuaJIT loader campaigns that ultimately delivered Lummastealer or RedLine.
Although the exact final payload delivered by TroyDen’s infrastructure has not been recovered its XOR keys are assembled at runtime inside the Lua VM the shared codebase, C2 co-location, and infostealer-like behavior all point to credential theft as the main objective.
Volume-first, AI-assisted malware
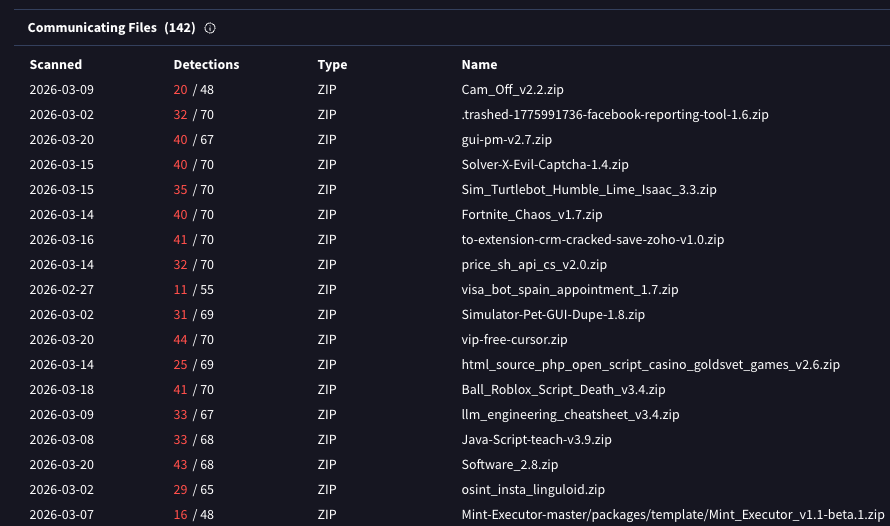
VirusTotal telemetry ties more than 300 distinct delivery packages back to TroyDen’s Frankfurt C2 nodes, cutting across audiences from developers and AI enthusiasts to Roblox players and users seeking cracked VPNs and phone trackers.
This breadth, combined with repeated use of AI-like naming vocabularies and polished but deceptive documentation, supports the picture of an AI-assisted lure factory tuned for volume, not precise targeting.
Netskope notes that the attack chain is explicitly crafted to punch through automated defenses: split-file loaders, extreme sleep delays, interpreter-plus-data pairings, and GitHub-based social proof all ensure the threat only fully reveals itself when a human analyst executes the entire chain in context.
Netskope Advanced Threat Protection ultimately detected the counterfeit OpenClaw deployer and related packages through behavioral heuristics rather than signatures, blocking customers before compromise and reporting the key repositories to GitHub on March 20, 2026.
For defenders, any GitHub-hosted download that couples a renamed scripting runtime with an opaque “data” file especially in AI tool or game-cheat repos should be treated as a high-priority triage candidate and monitored closely for LuaJIT, Prometheus-obfuscated payloads, and screenshot-first C2 beacons.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.