The 2025 spam and phishing landscape shows a sharp rise in AI-generated lures and QR code–based “quishing,” alongside complex malware campaigns abusing cracked games and software to deliver information stealers at scale.
These trends highlight how social engineering and multi‑stage loaders now work together to bypass traditional security controls and monetize stolen data.
Threat actors increasingly rely on generative AI to craft convincing phishing emails, instant messages, and fake login pages that closely mimic brand tone, grammar, and localized language patterns.
Large batches of highly tailored messages can now be generated in minutes, allowing campaigns to dynamically adapt subject lines, greetings, and body content to user profiles, geolocation, or ongoing news events.
This reduces the obvious red flags poor language, generic content, inconsistent branding that many users previously relied on to spot scams.
AI also powers look‑alike chatbot interfaces and fraudulent “support assistant” flows that guide victims step‑by‑step to enter credentials or payment data into attacker‑controlled forms.
Combined with deepfake logos and cloned website layouts, these interactions make phishing pages harder to distinguish from legitimate portals, even for experienced users.
The attackers distributed the malware under the guise of a hacked game on a popular gaming web resource.
Organizations report more phishing email compromise (BEC) attempts where AI-polished messages imitate internal tone and style, increasing reply and click-through rates.
QR Code Quishing Surge
QR-based phishing, or quishing, surged in 2025 as attackers shifted away from obvious malicious links toward scannable codes embedded in emails, PDF invoices, office signage, and even printed “parking” or “delivery” notices.
Security tools that heavily weight URL reputation and link scanning often give less scrutiny to QR images, while users typically scan them with personal mobile devices that may be less monitored than corporate endpoints.
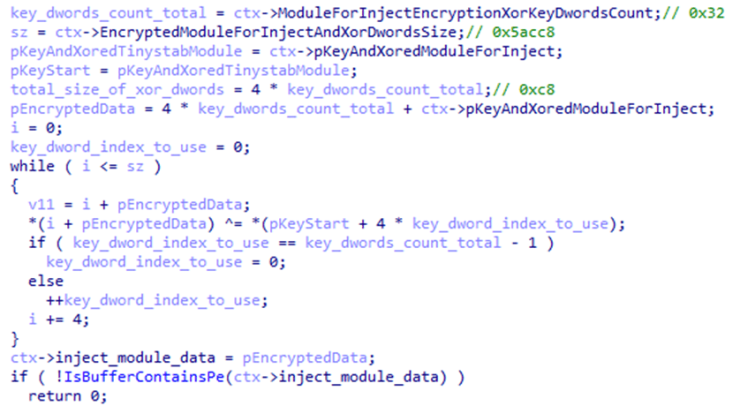
The ti module, launched in the child process, reads the hap.eml file, from which it decrypts the second stage of HijackLoader. The module then loads the pla.dll system library and overwrites the beginning of its code section with the received payload.
Once scanned, codes redirect victims to credential-harvesting portals, MFA token theft pages, or malware-hosting sites disguised as courier portals, SaaS login pages, and tax or payroll portals.
In some campaigns, attackers chain quishing with AI-written follow-up messages, nudging victims to “complete verification” or “fix account issues,” further boosting the success of the initial QR lure.
This channel is especially effective against hybrid workers who frequently use mobile devices to access corporate resources.
Parallel to phishing trends, 2025–2026 saw a large-scale campaign abusing pirated games and cracked software to distribute the RenEngine loader, which in turn deploys HijackLoader and infostealers such as Lumma and ACR Stealer.
The operation uses modified Ren’Py-based game launchers that show a fake loading screen at 100% while Python scripts quietly decrypt and run a hidden malware chain in the background.
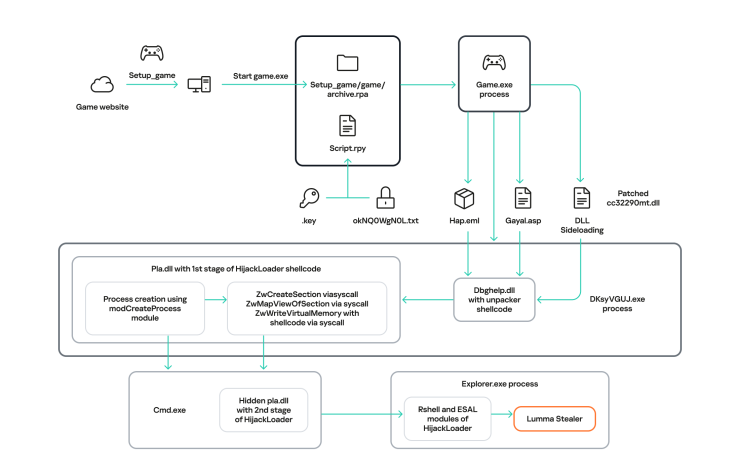
Kaspersky detects RenEngine as Trojan.Python.Agent.nb and HEUR:Trojan.Python.Agent.gen, and has tracked activity since March 2025, initially tied to Lumma stealer distribution.
RenEngine drops multiple components into temporary directories and abuses legitimate executables and DLLs for side-loading, ultimately handing control to HijackLoader, a modular loader first documented in 2023.
HijackLoader then leverages techniques such as DLL side-loading system, module stomping, process hollowing, and process doppelgänging to inject the final payload often ACR Stealer into trusted processes like explorer.exe.
The campaign has impacted hundreds of thousands of systems globally and continues to infect thousands of new victims per day, stealing browser credentials, cookies, crypto wallets, and system data.
What defenders should do
To counter AI-driven phishing and quishing, organizations should combine secure email gateways with computer vision and content analysis capable of detecting QR codes, brand impersonation, and dynamically generated phishing templates, instead of relying only on static URL rules.
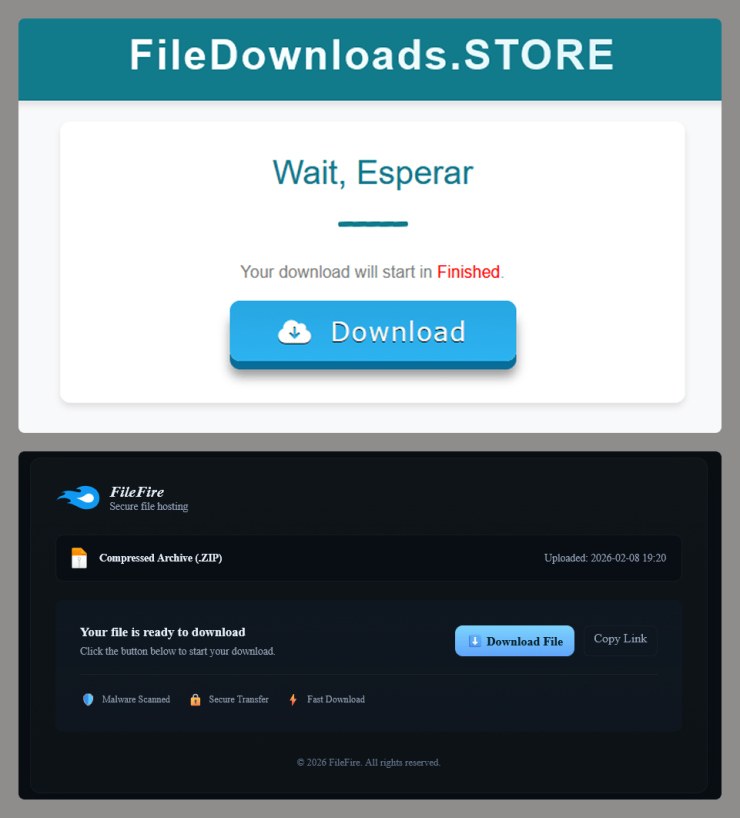
When the user clicks the Descargar Ahora (“Download Now”) button, they are redirected several times to other malicious websites, after which an infected archive is downloaded to their device.
Regular user training must cover QR risks, AI-polished messages, and MFA token theft, with clear guidance to verify codes and links through official channels before entering credentials.
Endpoint protection and behavior-based detection remain critical against loader chains like RenEngine and HijackLoader, especially on systems used for gaming or running unvetted software.
Blocking pirated software, enforcing application control, and monitoring for anomalous process-spawning, DLL side-loading, and credential-stealer activity can significantly reduce the impact of these campaigns.
Ultimately, 2025’s data shows that social engineering and stealthy loaders are converging, and defenders must raise both user awareness and technical detection depth to keep pace.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.