Highlighting growth of phishing and digital scams targeting United States citizens, Bolster released a research that identified 24 separate nation-state threat actor groups attempting to exploit rising political tensions across the US to interfere with the 2024 presidential election.
“We know the frequency of phishing attacks is increasing, as hackers utilize AI to execute more scams than ever before. In fact, phishing scams are being hosted in the US at a rate of nearly double, compared to 2023. The trend is only accelerating. In May alone, we logged a daily average of more than 45K malicious phishing sites,” said Abhilash Garimella, VP of Research at Bolster.
“More troubling, our researchers identified packages of voter data stolen over the past decade, for sale on the dark web and used by threat actors to create fake identification cards, potentially leading to identity theft or voter fraud.”
Cyber threats and the 2024 U.S. presidential election
Attackers are leveraging AI to automate mass spam campaigns, and also to reply in real-time. This targeting and interactivity at scale increases their chances of gaining access to more sensitive data.
The influx of election-themed spam is a significant cyber threat, causing widespread confusion among citizens and undermining trust in legitimate election communications. Attackers aim to capture sensitive financial information, login credentials, or personal data from unsuspecting individuals by exploiting their trust in familiar communication channels and creating a false sense of urgency by sending messages through multiple channels.
US military and government email accounts targeted and sold on dark web
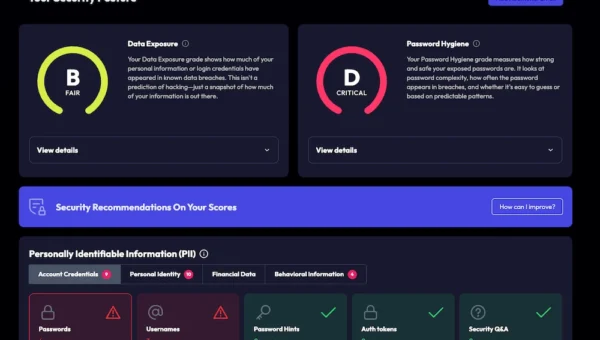
Of the 24 threat actor groups targeting the US election, 75% came from either China, Russia or Iran. Data breaches have exposed voter information, giving threat actors access to databases of personal identifiable information (PII), making fraud and identity theft easier to perpetrate. Bolster has also identified databases of voter data with more than 100,000 data points from state-level breaches dating back to 2015 for sale on the dark web.
Multiple threat actors are also capitalizing on this stolen data by providing fully editable PSD templates with complete Know Your Customer (KYC) details for identification cards, potentially leading to identity theft and voter fraud at scale. These templates enable individuals to build counterfeit IDs including personal information obtained through phishing or data breaches.
Unfortunately, not even the US military and government are immune from being targeted through .mil and .gov email addresses. The report found that threat actors are breaching accounts and selling access to them on the dark web. Criminals then exploit the credibility associated with a US government email account to deceive users into believing requests are legitimate, and resulting in disclosure of confidential data, for example, using counterfeit Emergency Data Requests (EDRs).