A new NGate malware variant that hides inside a trojanized version of HandyPay, a legitimate NFC payment relay app for Android, to steal card data and PINs for ATM cash-outs and fraudulent payments.
The injected code shows clear signs of being produced with generative AI, highlighting how low‑skill actors can now weaponize NFC payment apps at scale.
HandyPay is a legitimate app, available on Google Play since 2021, that lets users relay NFC card data between devices so a linked phone can perform tap‑to‑pay transactions on behalf of the cardholder.
Threat actors obtained a clean HandyPay APK, injected malicious logic into it, and distributed the altered build outside Google Play, never through the official store.
Once installed, the trojanized app behaves much like the original: it asks to be set as the default NFC payment app and walks the user through tapping their card on the back of the device.
ESET Research has discovered a new variant of the NGate malware family that abuses a legitimate Android application called HandyPay.
Under the hood, however, NGate intercepts the NFC payload and transparently relays it to an attacker‑controlled Android device that can emulate the victim’s card for contactless payments and ATM withdrawals.
Unlike many banking trojans, the app requests almost no additional permissions beyond what HandyPay legitimately needs, helping it appear harmless and bypass user suspicion.
The attacker device is pre‑linked via hard‑coded email addresses, ensuring all relayed NFC traffic routes only to the operators’ infrastructure.
AI‑generated malicious code
ESET’s analysis of the patched HandyPay package found log strings containing emojis, a pattern strongly associated with code or comments produced by large language models and GenAI assistants.
HandyPay, on the other hand, is significantly cheaper, only asking for the €9.99 per month donation, if even that. In addition to the price, HandyPay natively does not require any permissions.
These artifacts suggest the threat actors likely used GenAI to generate or refactor parts of the malicious code, even though there is no definitive proof of the exact toolchain.
This aligns with a broader trend where cybercriminals use GenAI to lower the barrier to entry, quickly creating workable Android malware without deep programming expertise.
In this case, AI appears to have assisted in building the exfiltration logic that packages PIN data and sends it to a command‑and‑control (C&C) server over HTTP.
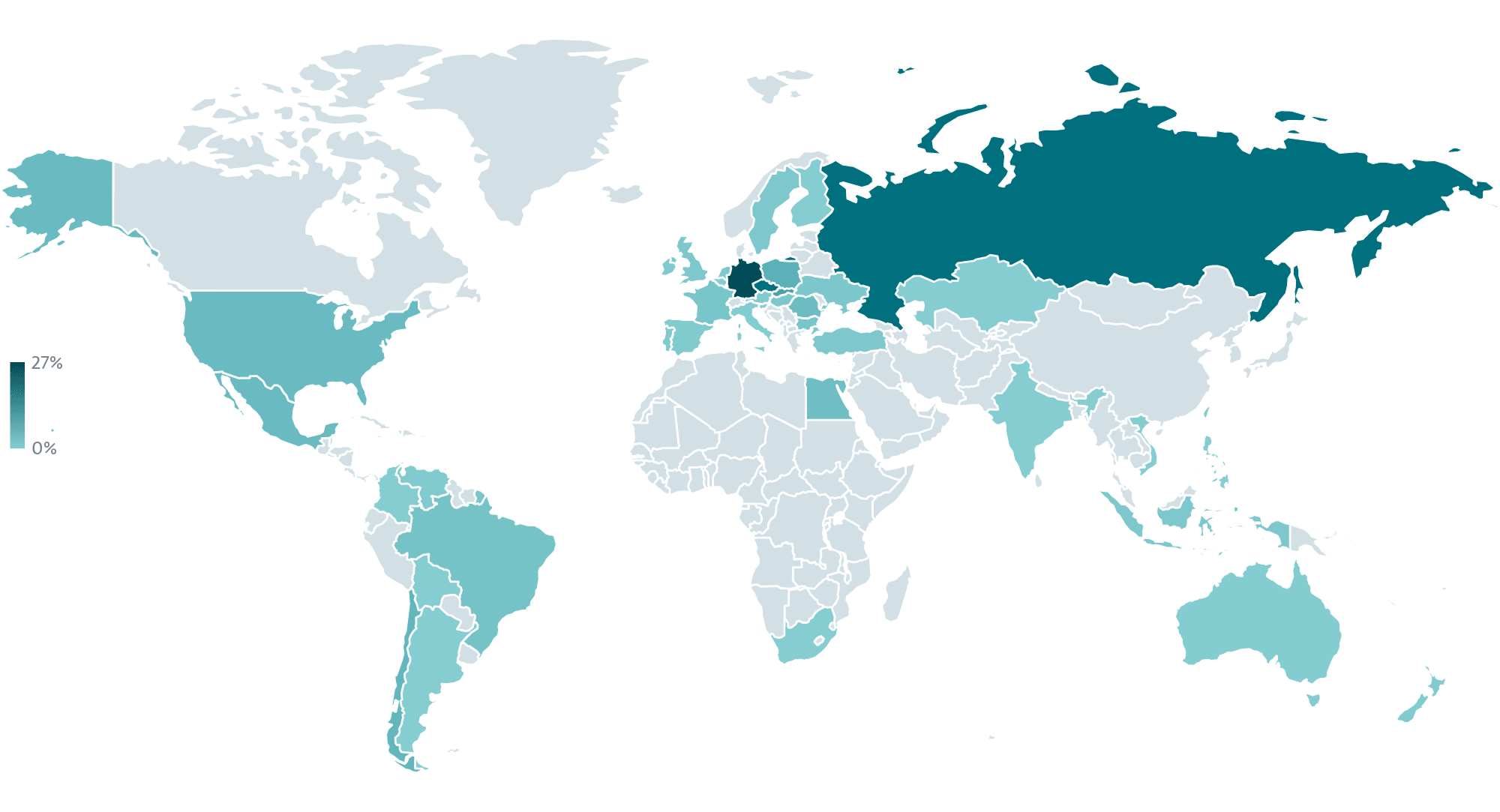
The current NGate campaign has been active since around November 2025 and is focused on Android users in Brazil.
ESET found logs from multiple compromised devices on the attackers’ C&C server, all geolocated in Brazil and containing captured PINs, IP addresses, and timestamps.
Investigators saw two main distribution vectors, both hosted on the same domain and thus likely operated by a single threat group.
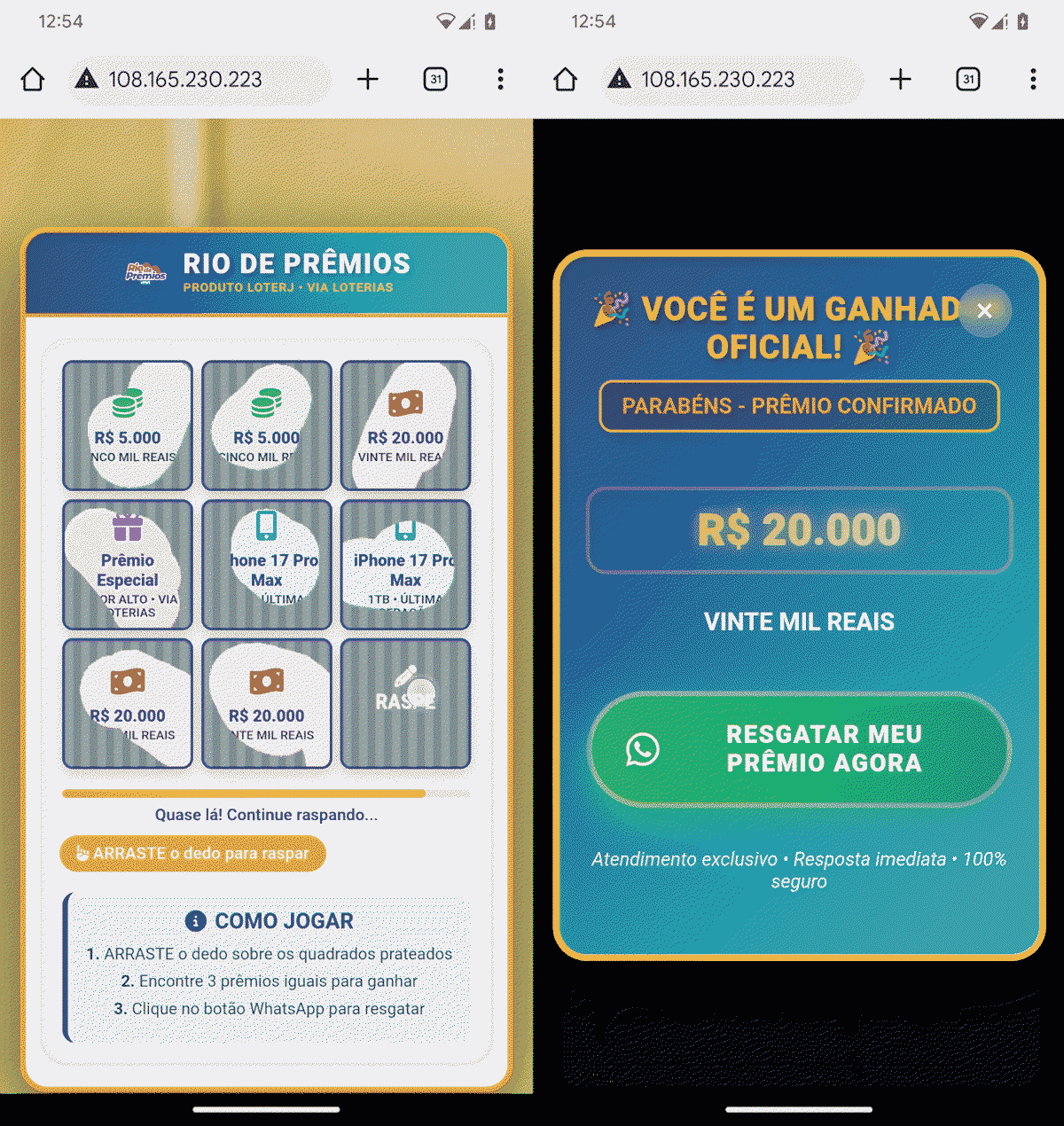
- A fake Rio de Prêmios lottery site that rigs a scratch‑card game so users always “win” R$20,000, then pushes them to WhatsApp to “claim” the prize and ultimately delivers the trojanized HandyPay APK.
- A spoofed Google Play web page advertising an app called “Proteção Cartão” (Card Protection), which tricks users into sideloading the same patched HandyPay build.
This is not the first time NGate or its PhantomCard variant has targeted Brazil, but it shows an evolution from using tools like NFCGate and MaaS kits such as NFU Pay or TX‑NFC to abusing a cheaper, legitimate relay app instead.
Data theft and ATM cash‑out flow
After the victim enables installation from unknown sources and sideloads the malicious APK, the app prompts them to enter their payment card PIN and perform an NFC tap inside the interface. At that point, NGate:
- Captures the full NFC transaction data and sends it to an operator device that can emulate the card for in‑person tap‑to‑pay and ATM cash‑outs.
- Separately exfiltrates the PIN to a dedicated C&C endpoint over HTTP, which also doubles as the malware distribution server.
To increase credibility, the associated WhatsApp account uses a profile image that impersonates Caixa Econômica Federal, Brazil’s government-owned bank that manages the majority of lotteries in the country.
With both live NFC data and the correct PIN, attackers can rapidly withdraw cash from NFC‑enabled ATMs or perform high‑value contactless purchases without ever touching the physical card.
Android users remain protected against known NGate variants by Google Play Protect, but only if they avoid sideloading apps from untrusted links and verify that payment apps come from the official Play store.
IOCs
| SHA-1 | Filename | Detection | Description |
| 48A0DE6A43FC6E49318AD6873EA63FE325200DBC | PROTECAO_CARTAO.apk | Android/Spy.NGate.CC | Android NGate malware. |
| A4F793539480677241EF312150E9C02E324C0AA2 | PROTECAO_CARTAO.apk | Android/Spy.NGate.CB | Android NGate malware. |
| 94AF94CA818697E1D99123F69965B11EAD9F010C | Rio_de_Prêmios_Pagamento.apk | Android/Spy.NGate.CB | Android NGate malware. |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.