Here’s what’s been hot on the AI scene over the past 12 months, how it’s changing the face of warfare, and how you can fight AI-powered scams

Source link
Related Articles
All welivesecurity →Is Poshmark safe? How to buy and sell without getting scammed
Table of Contents Why is Poshmark a scammer’s favorite? High commission fee Counterfeit goods Seller beware One-and-done accounts Restricted communications What are the most common…
How it preys on personal data – and how to stay safe
Table of Contents A threat is born Malware-as-a-service: A profitable 'business model' Key features How to protect yourself Final thoughts Here’s what to know about…
Facebook exploit allowed attackers to remotely delete photos
A Facebook hack that allowed attackers to remotely delete any photo they wanted to from the social network has been patched by the company. 13…
Why a CVSS score of 7.5 may be a 10 in your organization
Aggregate vulnerability scores don’t tell the whole story – the relationship between a flaw’s public severity rating and the specific risks it poses for your…
How to get into cybersecurity
Cracking the code of a successful cybersecurity career starts here. Hear from ESET’s Robert Lipovsky as he reveals how to break into and thrive in…
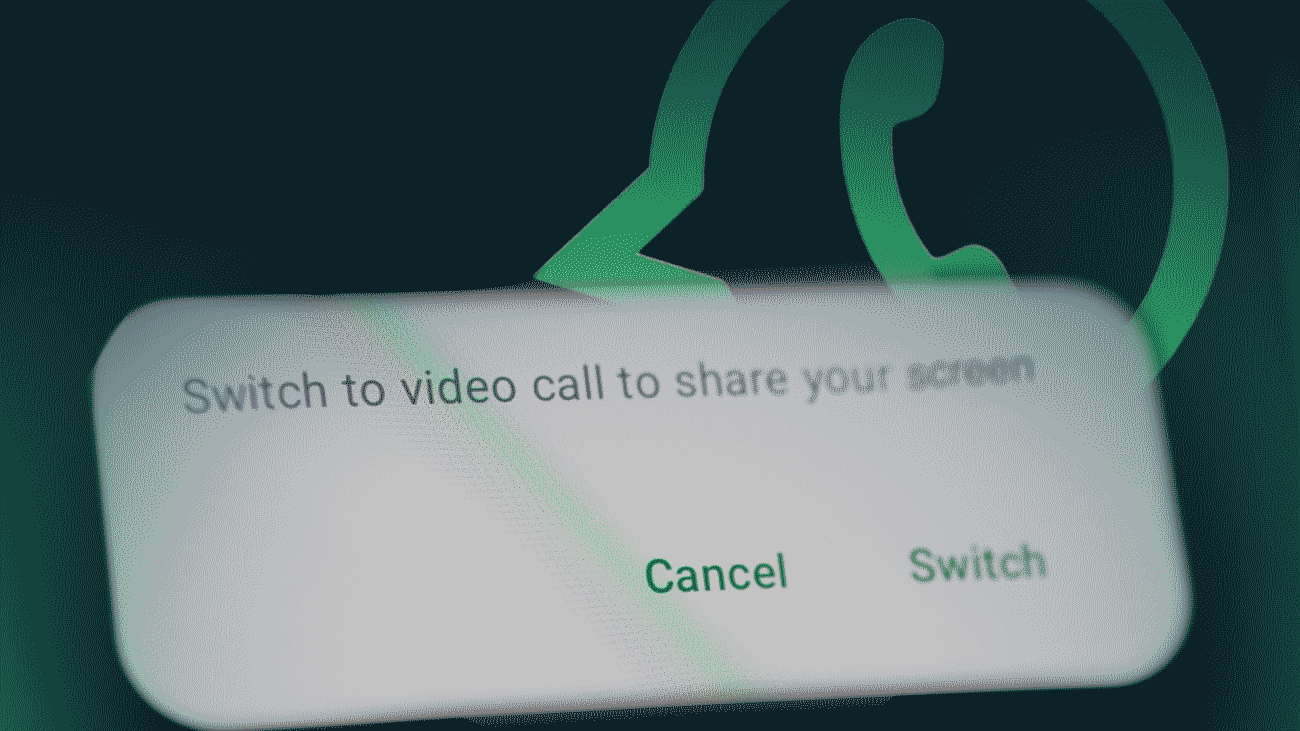
The WhatsApp screen-sharing scam you didn’t see coming
Table of Contents How does the scam unfold? 1. The call 2. The problem 3. Screen sharing 4. Access to personal data 5. Theft of…