Threat actors exploit Cisco AnyConnect vulnerabilities to gain unauthorized access to networks, compromise sensitive information, and potentially execute malicious activities.
Exploiting these vulnerabilities allows attackers to bypass security measures, leading to unauthorized control over network resources, potential disruptions to operations, cyber espionage, data theft, and ransomware deployment.
Cybersecurity analysts at Truesec recently discovered that Akira ransomware is actively exploiting the Cisco Anyconnect vulnerability.
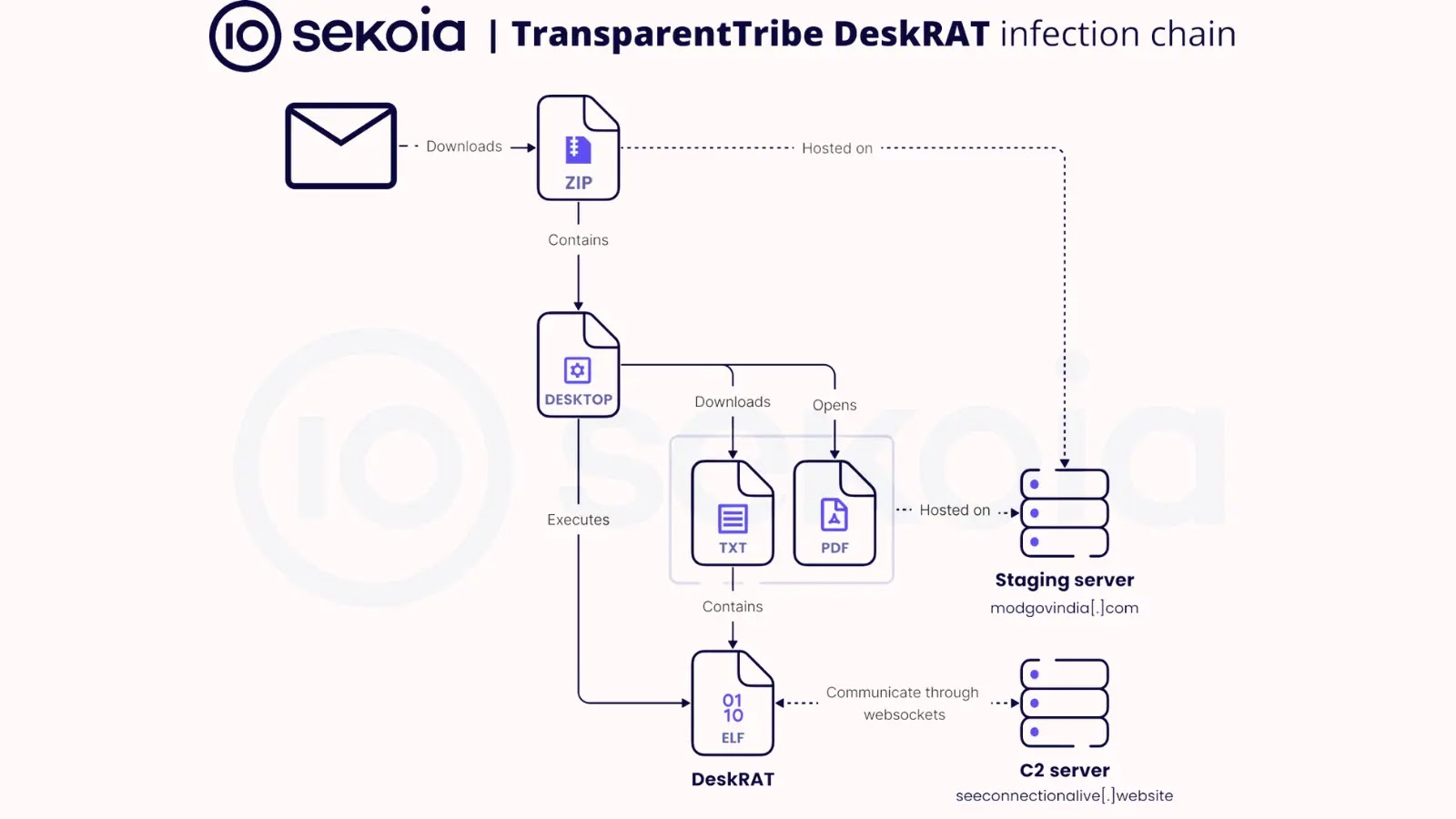
Truesec CSIRT found that 1Akira Ransomware has been actively exploiting the Cisco ASA and FTD flaw, which was tacked as “CVE-2020-3259,” which allows remote attackers to extract usernames and passwords from affected devices.
Akira Ransomware Exploiting CVE-2020-3259
Truesec’s analysis of eight recent Akira ransomware incidents links Cisco AnyConnect SSL VPN as the entry point.
Six compromised devices ran vulnerable software, while data on the other two was inconclusive for CVE-2020-3259 susceptibility.
To exploit this vulnerability, the device must have AnyConnect SSL VPN enabled on the interface exposed to the attacker, typically the internet-facing firewall interface.
Live attack simulation Webinar demonstrates various ways in which account takeover can happen and practices to protect your websites and APIs against ATO attacks.
Besides this, the following configuration should be in place:-
.webp)
.webp)
.webp)
Positive Technologies discovered CVE-2020-3259 in May 2020 but faced US sanctions in April 2021 for alleged ties to Russian Intelligence.
Akira was linked to the defunct Conti ransomware syndicate and may exploit the vulnerability.
However, Truesec doesn’t directly tie Akira’s actions to Russian intelligence, as they warn of potential risks to Western defenses from shared offensive security research.
Recommendations
For organizations running Cisco Anyconnect, it’s crucial to track when your device was updated post-CVE-2020-3259 disclosure.
Even if patched, the exploit indicators suggest potential prior exploitation. If the upgrade was 6 months old,, assume that the usernames/passwords used during that time were compromised.
So, in that case, it’s strongly recommended to reset passwords and change any other device secrets immediately.
Here below, we have mentioned all the other recommendations provided by the security experts:-
- Enable MFA everywhere possible and prioritize Client VPN connections.
- Enforce password changes post-version upgrade, especially for untouched accounts.
- Update secrets and pre-shared keys in device configurations post-version upgrade.
- Patch to a secure version if not already completed.
- Confirm logging is active across all systems.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.