Recent research by Trend Micro has uncovered a significant evolution in the Albabat ransomware, which now targets not only Windows but also Linux and macOS systems.
This expansion highlights the increasing sophistication of ransomware groups in exploiting multiple operating systems to maximize their impact.
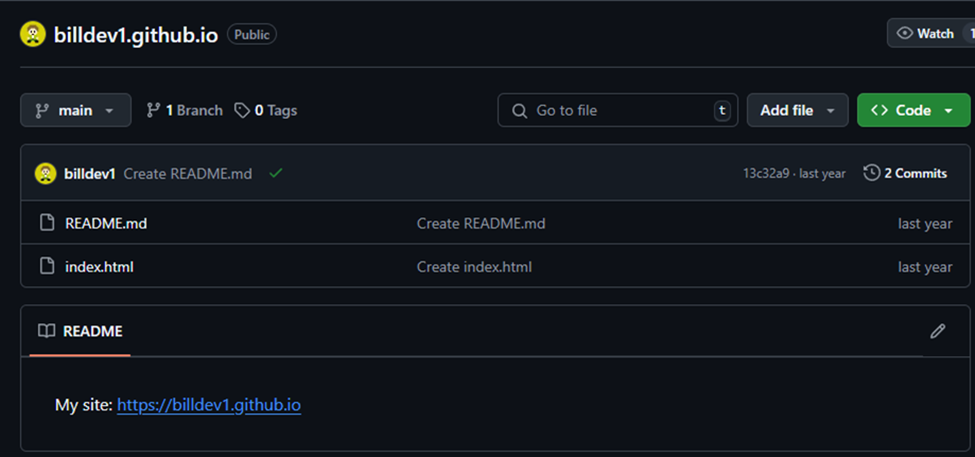
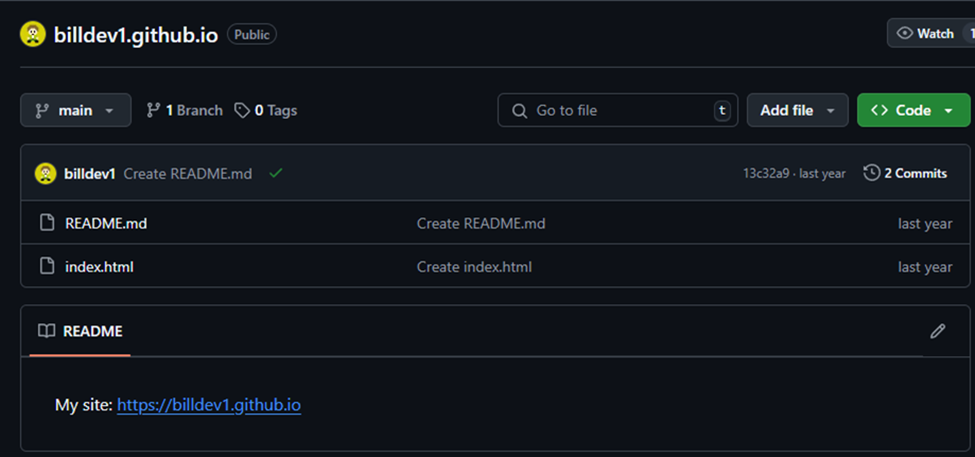
The Albabat group has been leveraging GitHub to streamline its operations, using the platform to manage configuration files and essential components of the ransomware.

Expanding Targets and Operational Efficiency
The latest versions of Albabat ransomware, specifically versions 2.0.0 and 2.5, have been designed to gather system and hardware information from Linux and macOS devices, in addition to Windows.


These versions retrieve their configuration data through the GitHub REST API, utilizing a “User-Agent” string labeled “Awesome App.”
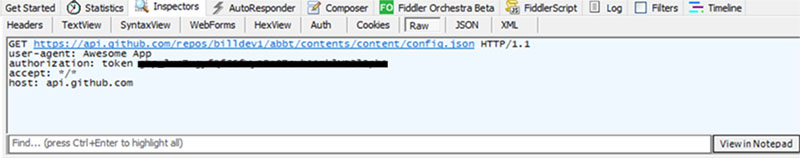
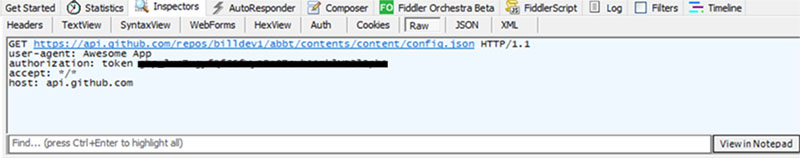
According to Trend Micro Report, this configuration provides crucial details about the ransomware’s behavior and operational parameters, indicating a sophisticated approach to managing and updating the malware.
The use of GitHub allows the attackers to maintain a centralized control over the ransomware’s configuration, making it easier to update and adapt their tactics.
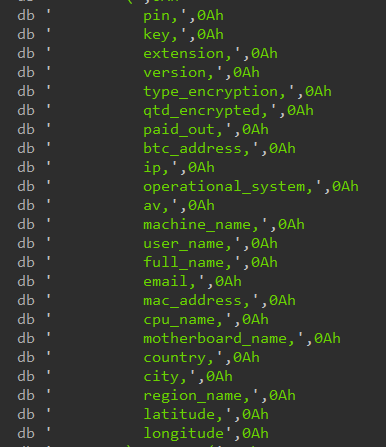
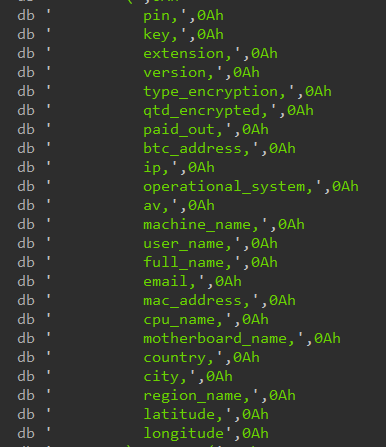
The ransomware encrypts a wide range of file extensions, including common formats like .exe, .lnk, .dll, and .mp3, while skipping specific folders and files to avoid detection or interference with system operations.
It also terminates various processes, such as task managers and productivity software, to prevent users from interfering with its activities.
The attackers store stolen data in a PostgreSQL database, which helps them track infections, monitor payments, and potentially sell sensitive information.
Security Implications and Recommendations
The Albabat ransomware’s ability to target multiple operating systems and its use of GitHub for operational efficiency underscore the need for robust cybersecurity measures.
Organizations should prioritize strong access controls, regular system updates, and secure backups to mitigate the risk of such attacks.
Implementing network segmentation can limit the spread of ransomware, while user training and awareness programs can help prevent initial infections.
Proactive security solutions, such as AI-powered platforms, can provide comprehensive protection by predicting and preventing threats, thereby reducing the risk of ransomware attacks.
The ongoing development of the Albabat ransomware, with a potential version 2.5 in the works, indicates that these threats will continue to evolve.
Therefore, staying informed about indicators of compromise (IoCs) and leveraging threat intelligence are crucial for maintaining effective cybersecurity defenses against emerging threats like Albabat.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup – Try for Free