- How the Investigation Begins
- The First Signal – Qualys VMDR
- A Second, Independent Confirmation: Microsoft Defender Vulnerability Management
- From Software Inventory to Active Attack Surface with Qualys EASM
- Why Identity Context Changes the Severity?
- The OpenClaw Lesson: Why Visibility Alone is No Longer Enough
- The Power of Contextual Correlation
- Frequently Asked Questions (FAQs)
- Contributors
Executive Summary
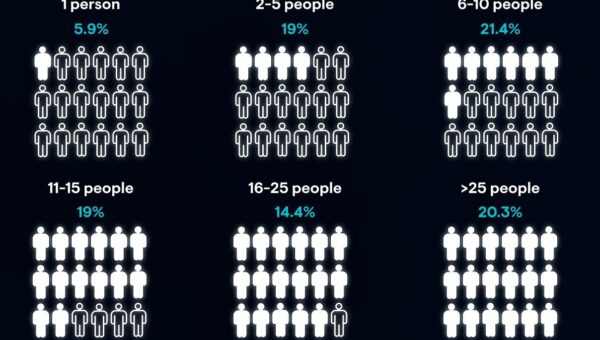
An unauthorized OpenClaw AI agent was detected disguised as a routine package on a Windows Server host. The situation escalated into a priority incident when Qualys ETM analyzed and correlated four distinct signals. While none of these signals alone warranted urgent action, the combination of endpoint, exposure, and identity telemetry indicated an active risk that needed immediate intervention.
Autonomous AI agents are changing how work gets done. By accepting natural-language instructions and executing actions directly on systems, they automate tasks that previously required human involvement. That efficiency is compelling for both users and security teams , but it introduces a new class of operational risk.
In an enterprise environment, an unauthorized autonomous agent can establish persistent communication paths, expose local services, execute commands, or operate with the same permissions as the user or system where it is installed. It is not just another application. It shifts the question from “What is this software?” to “What could this software enable?”
This is where Qualys Enterprise TruRisk Management (ETM) comes in. ETM enables a Risk Operations Center (ROC) analyst to correlate weak signals across endpoint, exposure, and identity telemetry and determine whether an issue belongs in the backlog or requires immediate action. The OpenClaw investigation that follows illustrates how this correlation plays out.
Turn endpoint, exposure, and identity signals into one actionable risk view.
How the Investigation Begins
A ROC analyst rarely starts with a clear, high-confidence incident. More often, the first signal is ordinary: a package vulnerability, an unknown application, or a policy exception on a workstation. The challenge is deciding whether that signal belongs in the backlog or deserves immediate attention.
That is how OpenClaw first appears in this investigation, as a routine detection on a Windows Server host.
The First Signal – Qualys VMDR
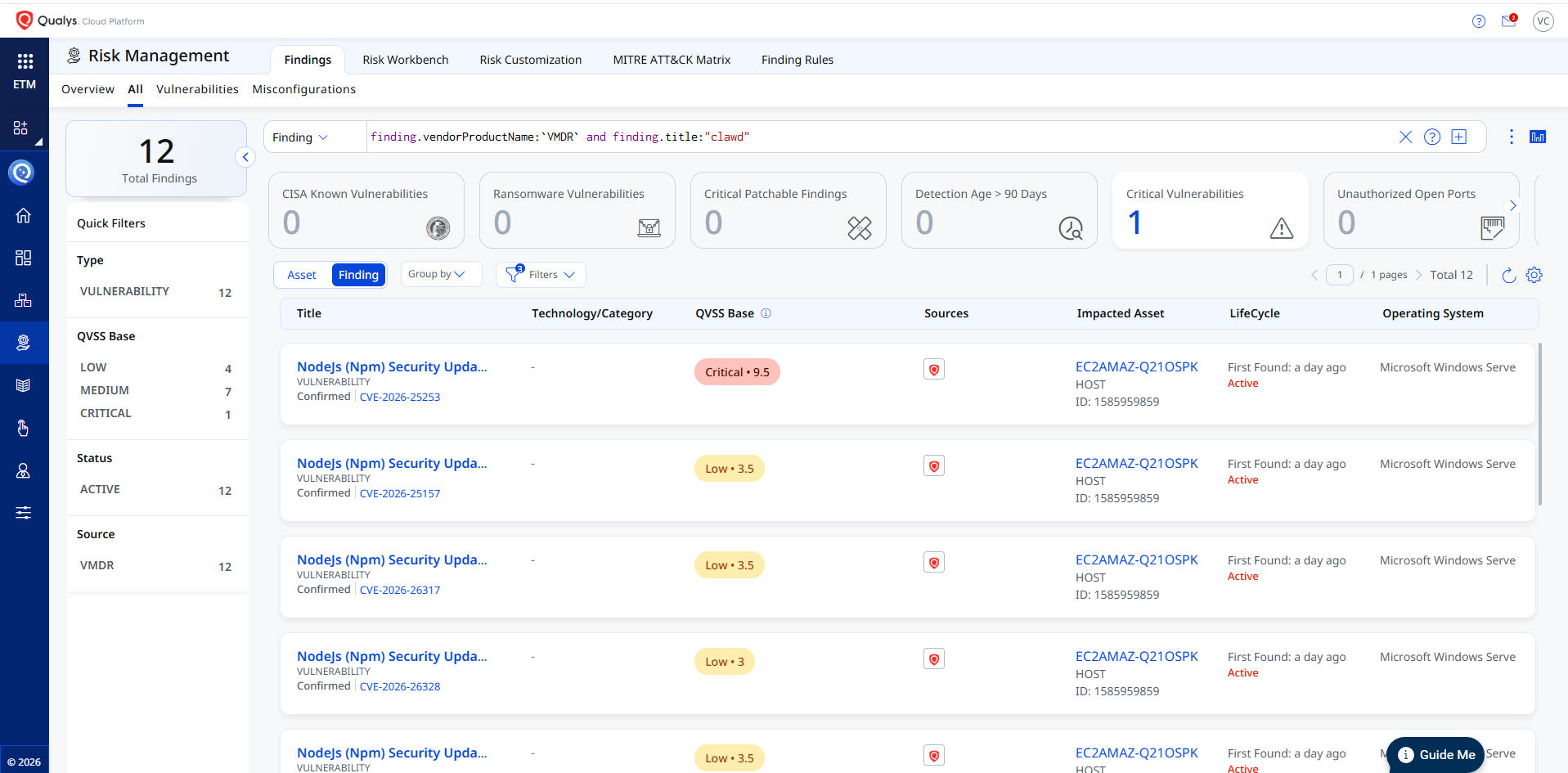
The Qualys scanner identifies a vulnerability in the clawdbot (OpenClaw) package installed on a Windows Server 2025 Datacenter EC2 instance. The detected version is outdated, prior to the patched release 2026.1.29, and is associated with GHSA-g8p2-7wf7-98mq / CVE-2026-25253.
The vulnerability stems from a flaw in the Control UI that trusts the gatewayUrl parameter from the query string without validation. When the UI loads, it initiates a WebSocket connection and transmits a stored gateway token, potentially exposing authentication tokens to unauthorized endpoints.
This detection establishes the presence of a vulnerable package. Qualys ETM builds on this by adding risk context. CVE-2026-25253 carries a CVSS base score of 8.8 and a QVSS of 9.5 (Critical), along with Real-Time Threat Indicators indicating a public exploit and active attacks.

For a ROC analyst, this still represents an incomplete picture. The presence of a vulnerable package and active exploitation signals is meaningful, but not sufficient to determine risk. The analyst must determine whether the package is in active use, reachable, and what downstream impact it may have. The next step is to correlate this signal with additional telemetry.
This first signal from VMDR is still actionable. Teams can begin with a QQL-based inventory sweep to identify all assets where clawdbot or OpenClaw is present, grouping results by TruRisk score and business criticality. From there, VMDR patch management can be used to deploy version 2026.1.29 or later. Tagging impacted assets (for example, openclaw-remediation) and creating a saved search for CVE-2026-25253 helps maintain visibility and detect reintroduction in subsequent scans. This brings the environment to a defensible position: known scope, prioritized remediation, and continuous monitoring.
A Second, Independent Confirmation: Microsoft Defender Vulnerability Management
One signal can be dismissed. Two independent signals are harder to ignore.
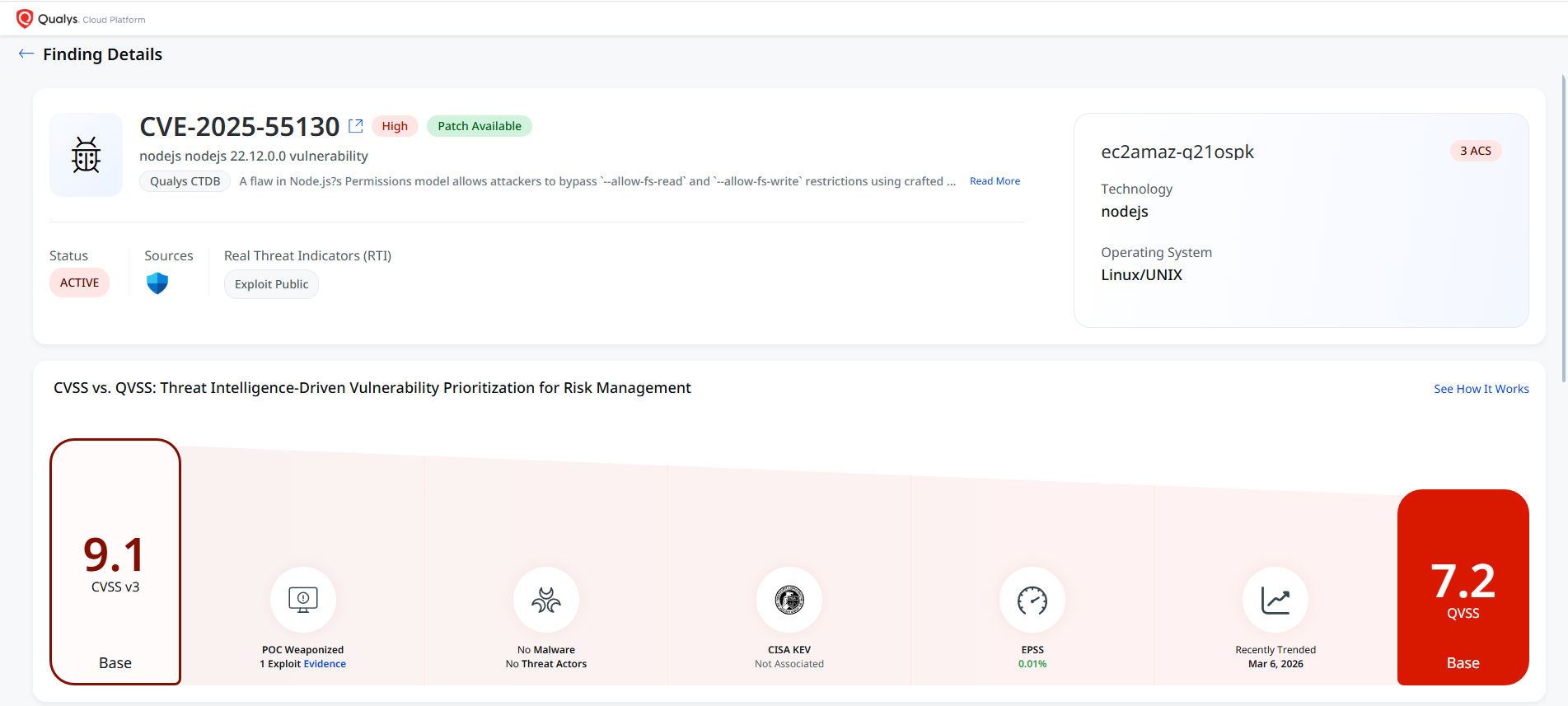
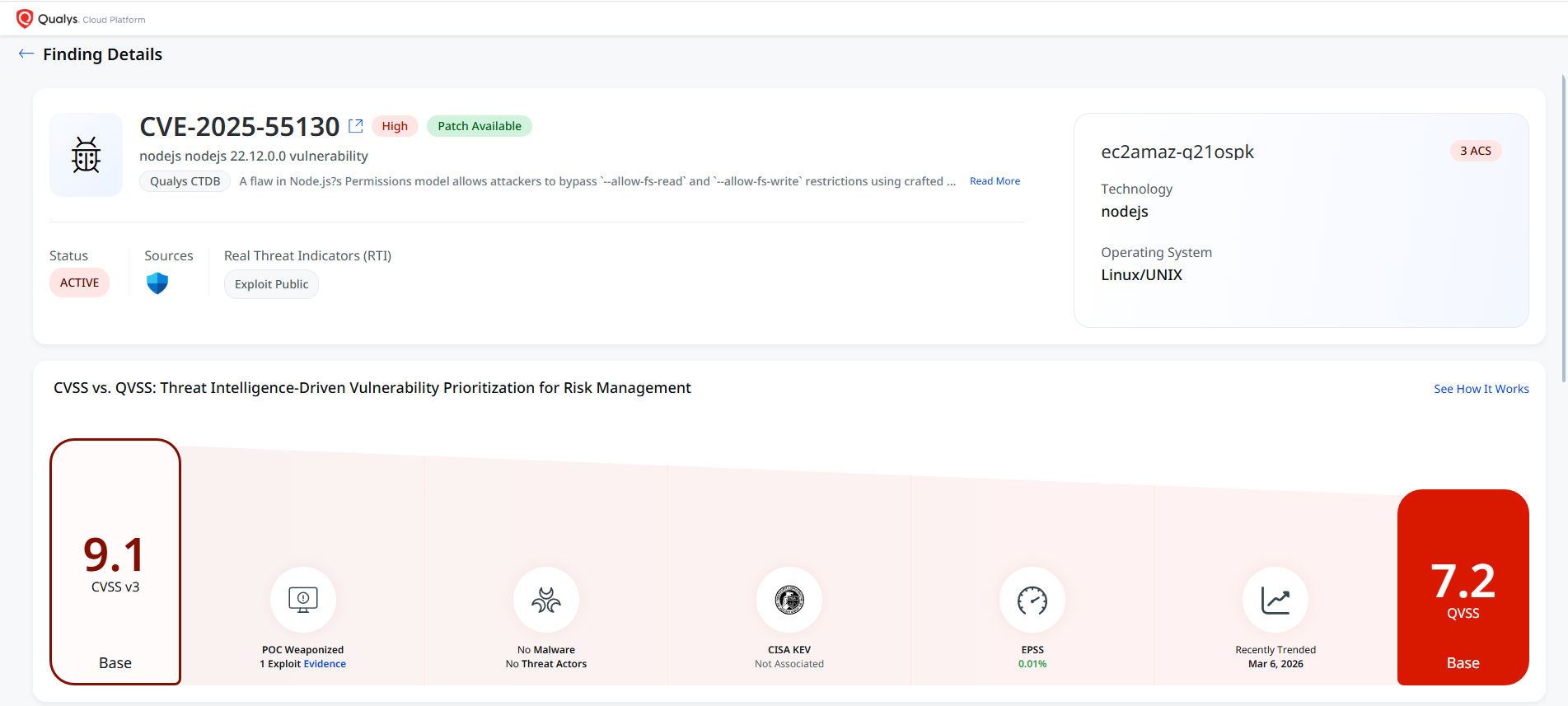
Microsoft Defender Vulnerability Management, surfaced inside Qualys ETM as a second source, independently flagged a Node.js vulnerability tied to OpenClaw components on the same host. confirms CVE-2025-55130 affecting Node.js 22.12.0 as an active, confirmed local finding, with a patch available and public exploit intelligence. ETM assigns the issue a QVSS base score of 7.2 alongside a CVSS v3 base score of 9.1, helping the analyst assess both severity and real-world risk in context.

For the ROC analyst, this changes the signal. This issue is no longer a single-source artifact. Two independent controls, Qualys VMDR and Microsoft Defender, confirm the presence of vulnerable Node.js components associated with OpenClaw on the same host. This convergence increases confidence and reduces the likelihood of false positives.
However, the question is still unresolved. The “vulnerable software exists on disk” is still different from “vulnerable software is actively running and reachable.” The investigation requires one more telemetry layer to make that determination.

From Software Inventory to Active Attack Surface with Qualys EASM
The next question is simple: does this stay local, or does it create reachable exposure?
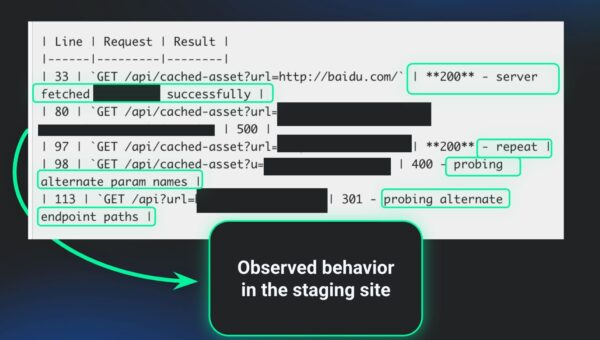
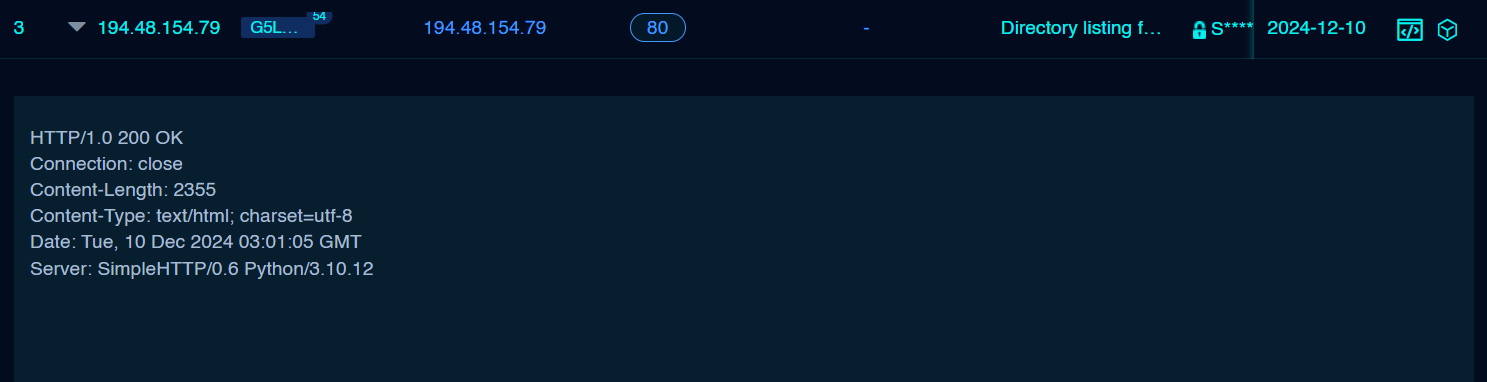
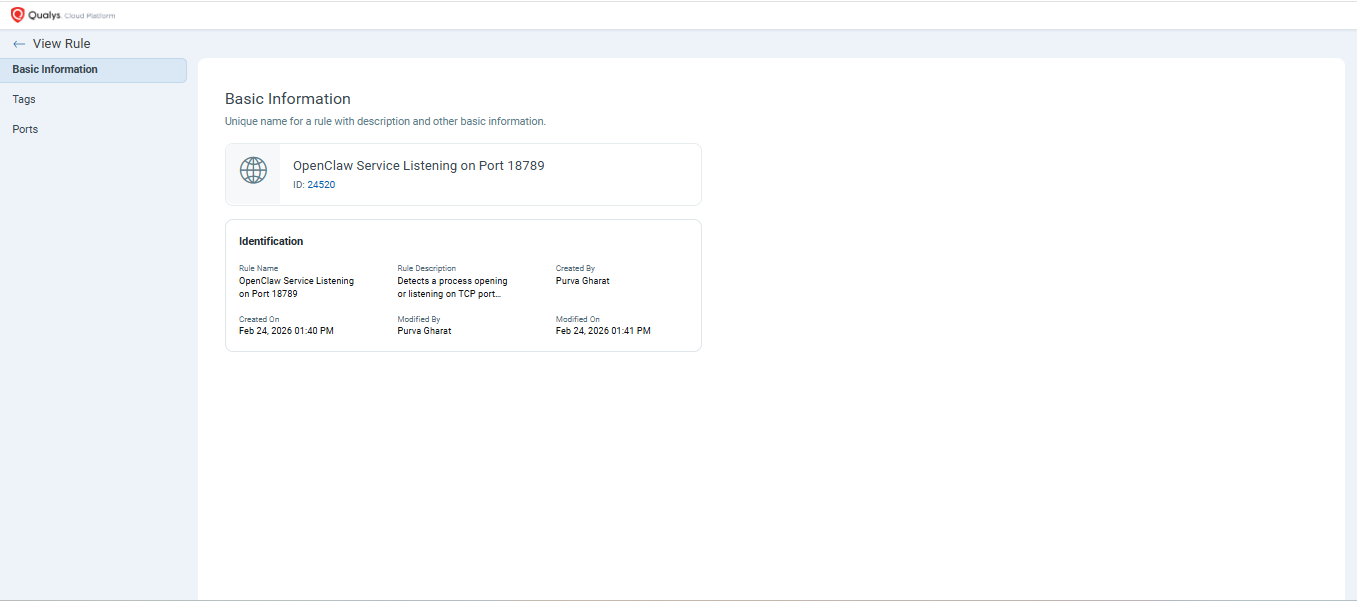
This is where Qualys External Attack Surface Management (EASM) adds critical context. OpenClaw uses port 18792 as its default communication port, and the observed service on that port is node.exe.
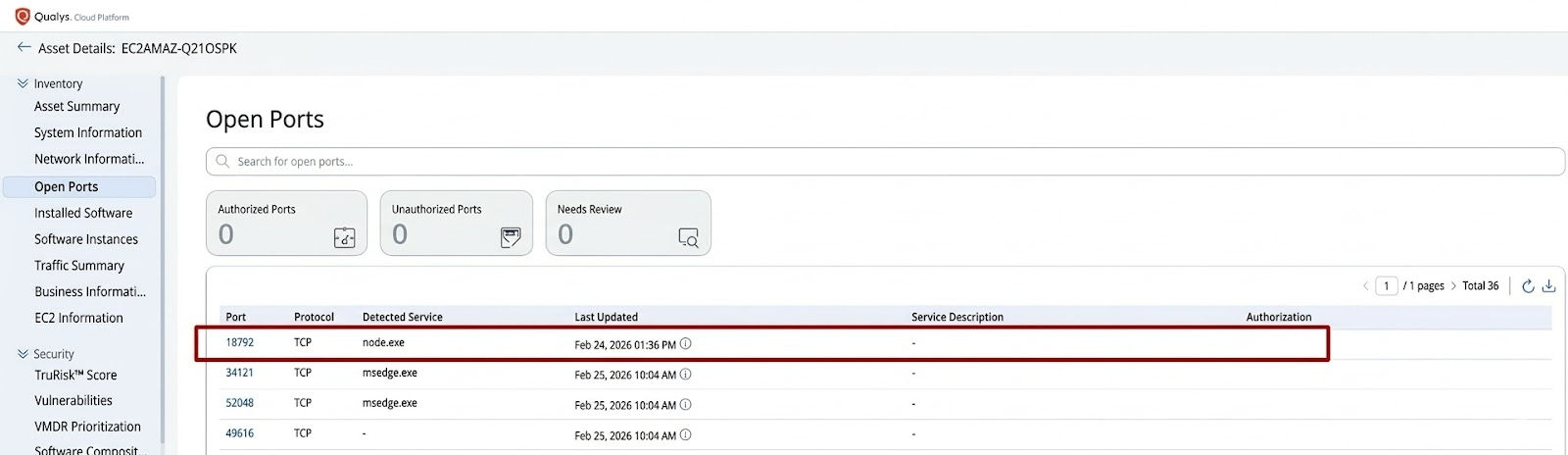
This observation marks the turning point in the investigation. A vulnerable package on disk is one thing. A live runtime service listening on an exposed port is another. It tells the analyst three things at once: the Node.js runtime is active, the OpenClaw software is in use, and the issue has moved from software inventory risk into active attack surface.
- Port: 18792
- Protocol: TCP
- Detected Service: node.exe
For the ROC analyst, prioritization shifts immediately. The finding is now a potentially reachable service tied to an autonomous AI tool, one that already has a public exploit and a known token-leak primitive. It is no longer just about unauthorized software on a host.
Why Identity Context Changes the Severity?
Endpoint findings rarely tell the whole story. Once a suspicious or unauthorized agent is identified, the next question is: what could an attacker do next if they gained leverage through this host?
This is where Qualys ETM Identity extends the investigation beyond the endpoint.
Two identity weaknesses are especially important in this context.
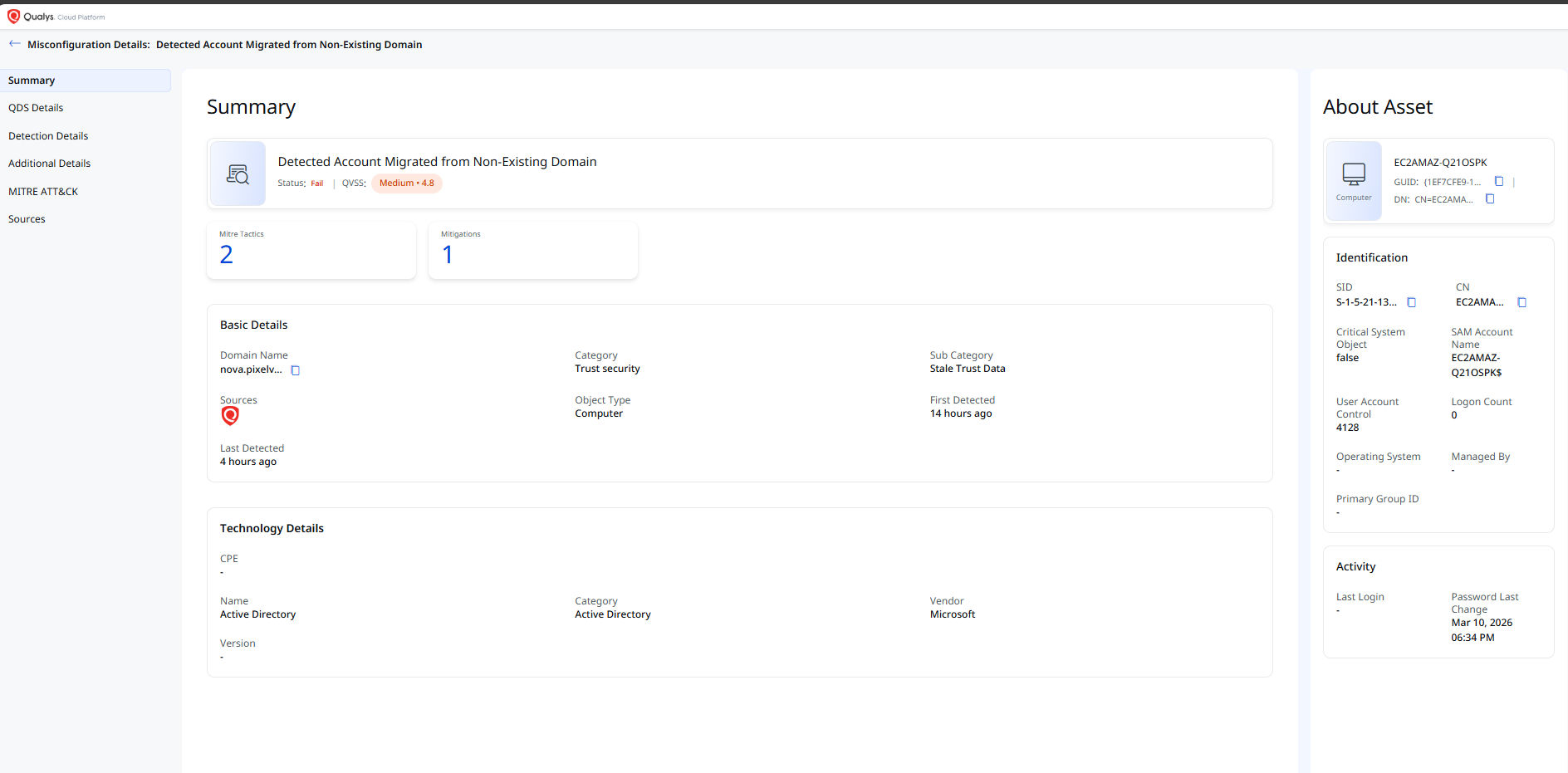
- The presence of accounts with SID History tied to non-existing domains. These stale identifiers can create opportunities for abuse through SID-History Injection, enabling impersonation of privileged identities and creating paths to privilege escalation.
- The presence of accounts that do not require Kerberos pre-authentication. This increases exposure to AS-REP Roasting attacks and raises the risk of credential compromise, lateral movement, and broader domain impact.
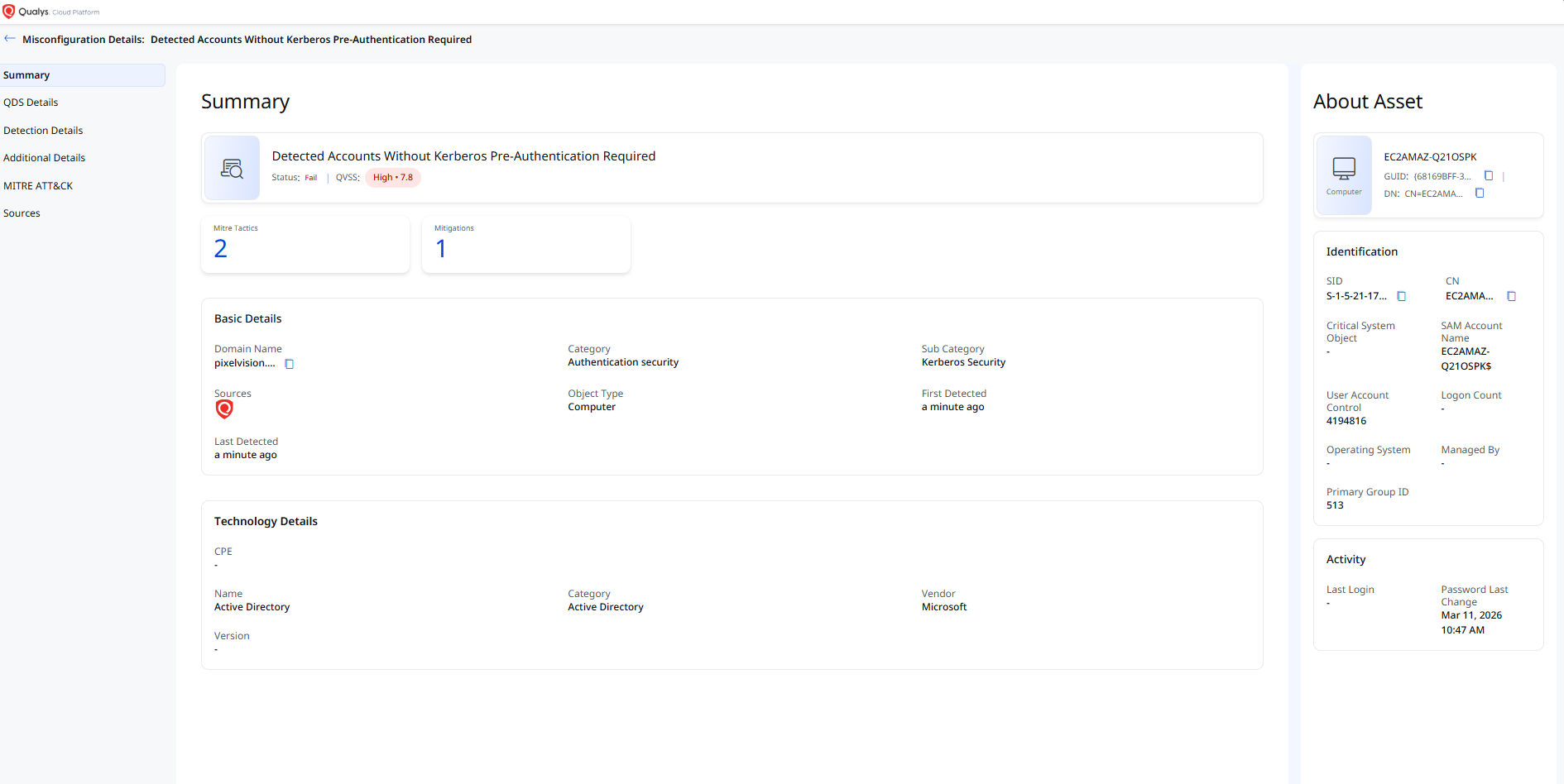
When ETM correlates these identity weaknesses with the OpenClaw findings, an attack path begins to emerge. EASM identifies a reachable Node.js service running the OpenClaw agent. VMDR and Microsoft Defender confirm that the underlying Node.js and clawdbot components are exploitable. ETM Identity shows that once an attacker gains access to the host, the surrounding identity environment offers viable routes toward Domain Admin and the Domain Controllers.
The chain looks like this:

This is the kind of context the ROC teams need. It does not just confirm that OpenClaw is present and active. It shows how the surrounding identity conditions can turn a single endpoint compromise into a broader domain incident. ETM helps answer the critical question: if this host is abused, how far could the attacker go?
The OpenClaw Lesson: Why Visibility Alone is No Longer Enough
OpenClaw is a practical example of why Qualys ETM matters.
A single vulnerability may not look urgent. A package name alone may not justify escalation. Even an unauthorized application might be dismissed as experimentation. But when multiple signals are correlated, the picture changes.
- VMDR identifies vulnerable OpenClaw packages and their exact install paths.
- Microsoft Defender Vulnerability Management independently confirms the underlying Node.js exposure on the same host.
- EASM reveals active runtime behavior and a reachable service on TCP/18792.
- ETM Identity surfaced exposes identity weaknesses that can amplify the impact of a compromise.
Individually, each finding is a line item. Together, they describe a vulnerable, active, reachable autonomous agent operating in an environment with identity conditions that favor an attacker. That is the value ETM brings to ROC analysts: it connects technical findings to operational risk, so prioritization reflects what an adversary could actually do, not just what a scanner reports.
Once the issue is prioritized, the next step is action.
Security teams must determine whether OpenClaw is approved, whether it should be removed, whether the exposed service is externally reachable, and whether the identified identity weaknesses could increase the impact of a compromise. From there, policy and remediation workflows focus on removing unauthorized OpenClaw components, controlling related Node.js activity, hardening affected accounts, and preventing reinstallation or repeat exposure.
The response is no longer guesswork. The same correlated story that justified escalation also tells the responder exactly which controls to act on, in which order, and on which assets.
The Power of Contextual Correlation
OpenClaw highlights a broader challenge for modern security teams. AI-driven tools may first appear as routine software findings, but their significance changes when they are active, reachable, and operating in environments with weak identity controls.
Qualys ETM enables ROC teams to move beyond isolated alerts by correlating endpoint evidence, exposure telemetry, and identity context into a unified risk view. Instead of asking whether OpenClaw is simply installed, analysts can determine whether it is vulnerable, active, externally relevant, and capable of contributing to broader compromise.
That is the difference between seeing a finding and understanding the risk.
Frequently Asked Questions (FAQs)
What is OpenClaw, and why does it introduce risk?
OpenClaw (also known as Clawdbot) is an autonomous AI agent that executes actions based on natural language instructions. When deployed without authorization, it can expose services, maintain persistent connections, and operate with user-level permissions. This creates a potential entry point for token leakage, command execution, and broader system compromise.
How does Qualys ETM help investigate AI agent risks?
Qualys Enterprise TruRisk Management (ETM) correlates signals across endpoint (VMDR), exposure (EASM), and identity telemetry to provide a unified risk view. Instead of treating findings in isolation, ETM connects vulnerabilities, active services, and identity weaknesses into a single attack path, helping analysts determine whether a seemingly minor issue requires immediate action.
What role does identity context play in AI agent risk?
Identity context defines how far an attacker can move after initial access. Misconfigurations such as stale SID History or disabled Kerberos pre-authentication can enable privilege escalation and lateral movement. When combined with a vulnerable and exposed agent like OpenClaw, these weaknesses can turn a single host compromise into a broader domain incident.
Does ETM replace existing security tools?
No. ETM does not replace tools such as vulnerability scanners or endpoint protection platforms. It builds on their findings by correlating them into a unified risk narrative, enabling security teams to prioritize remediation based on real-world attack potential rather than isolated alerts.
Contributors
- Sushant Paithane, Lead Threat Research Engineer, Malware Detection Solutions
- Pratham Patil, Associate Threat Research Engineer, Malware Detection Solutions