Android banking Trojan TrickMo evolves using TON network for C2

ThreatFabric found a new TrickMo Android trojan focused on stealth and persistence, moving its command-and-control traffic to the TON network.
Security researchers at ThreatFabric have recently identified a new version of TrickMo, a dangerous Android banking trojan that shows how malware operators are focusing less on flashy new features and more on improving stealth, flexibility, and long-term control over infected devices.
“The variant is a direct evolution of the previously documented TrickMo: the on-device feature set is largely unchanged, but the platform underneath has been deliberately re-engineered for stealth, resilience and operator reach.” reads the report published by ThreatFabric. “The most visible change is at the network layer, where the bot’s command-and-control traffic has been moved off the conventional internet entirely and onto The Open Network (TON).”

Instead of creating completely new malware families, attackers are redesigning existing platforms to survive longer, avoid detection, and give operators more control.
The latest TrickMo variant was discovered between January and February 2026 during campaigns targeting banking and cryptocurrency wallet users in France, Italy, and Austria. Researchers believe this updated version is gradually replacing older TrickMo variants already active in the wild. While many of its visible features remain similar, the malware’s internal structure has changed significantly.
An interesting aspect of TrickMo is its modular design. The main application acts mostly as a launcher and persistence layer, while additional malicious functionality is downloaded later as separate modules. This architecture gives attackers flexibility because new features can be added without reinstalling the malware.
One of the most important updates involves how TrickMo communicates with its operators. Traditionally, malware relies on standard internet infrastructure such as domains and public servers for command-and-control communication. This new version has abandoned that approach almost entirely.
The Open Network (TON) is a legitimate blockchain platform. Researchers said TrickMo C operators abused its infrastructure, without involvement or responsibility from the TON project.
“The most significant change is the migration of command-and-control traffic onto The Open Network (TON).” continues the report. “The single largest architectural change in TrickMo is that the bot no longer reaches its operator over the conventional internet. The primary command-and-control transport has been moved onto The Open Network (TON) — a decentralised peer-to-peer overlay network originally built for Telegram, with its own routing and naming layer (ADNL). Hosts inside TON are not addressed by DNS or by IPs in the public routing table; they are addressed by opaque base32 strings under a .adnl pseudo-TLD which the TON network resolves through its own decentralised infrastructure.”
This makes detection and takedown efforts far more difficult because the infrastructure does not rely on the traditional DNS system.

The malware even includes an embedded TON proxy running locally on the infected phone. All communications pass through this proxy, helping traffic blend in with legitimate TON activity. From a defender’s perspective, malicious traffic becomes much harder to distinguish from normal encrypted network usage.
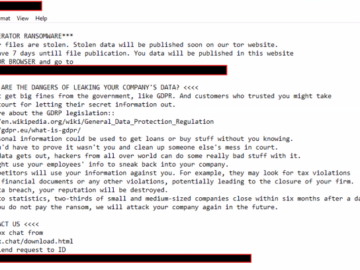
Beyond communication upgrades, TrickMo still performs the classic banking trojan functions that make it so dangerous. Once accessibility permissions are granted, attackers can remotely interact with the device in real time. The malware can display fake banking login pages, capture keystrokes, intercept SMS verification codes, monitor notifications, record screens, and remotely control the phone.
However, the newest variant expands far beyond simple banking fraud. Researchers discovered advanced networking capabilities built directly into the malware. Operators can now perform DNS lookups, ping systems, trace routes, and run HTTP requests directly from the infected device. This effectively turns compromised phones into reconnaissance tools inside corporate or home networks.
What makes this threat especially worrying is its professional evolution. TrickMo is no longer just a banking trojan stealing credentials. It is becoming a flexible cybercrime platform capable of remote surveillance, network pivoting, fraud support, and future feature expansion.
“The largest functional addition in this variant, and the change that justifies framing the family as a managed foothold rather than a banking trojan, is a network-operative subsystem.” states the report. “Five operator commands run network primitives from the device’s vantage point and return the results upstream:
| Command | Description |
| curl | Full curl-CLI HTTP probe (any method, headers, body) |
| dnslookup | Platform-resolver DNS lookup for any hostname |
| ping | ICMP echo via the platform’s /system/bin/ping |
| telnet | TCP-connect probe with timeout, multi-port supported |
| traceroute | Route trace via the platform’s /system/bin/traceroute |
Even more concerning is the addition of SSH tunneling and SOCKS5 proxy features. These tools allow attackers to route traffic through the victim’s own internet connection. In practice, this means cybercriminals can make fraudulent activity appear as if it originates directly from the victim’s device and IP address.
“This latest variant also expands the operational role of infected devices through SSH tunnelling and authenticated SOCKS5 proxying, effectively turning compromised phones into programmable network pivots and traffic-exit nodes whose connections originate from the victim’s own network environment.” states Threat Fabric.
This capability significantly increases the value of infected devices for cybercriminal operations.
Researchers also found signs that TrickMo operators are preparing for future capabilities. The malware contains inactive components linked to NFC permissions and a hooking framework called Pine. Although these features are not currently active, they suggest the developers are building a platform ready for future updates, possibly targeting contactless payment systems or deeper application manipulation.
As Android security continues to improve, malware developers are responding with smarter architectures, decentralized communications, and modular attack frameworks. TrickMo’s evolution demonstrates that the future of mobile malware is not necessarily louder or more visible — it is quieter, more persistent, and far more adaptable.
“Overall, Trickmo can be seen as a ‘reborn’ threat: not entirely new, but refined and adapted to remain effective in a more secure and scrutinized mobile environment.” concludes the report.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, malware)