Anthropic recently unveiled Claude Mythos Preview, a groundbreaking general-purpose language model demonstrating an unprecedented, emergent ability to autonomously discover and exploit zero-day vulnerabilities.
In response to these powerful capabilities, the company introduced Project Glasswing, a coordinated defensive initiative aimed at securing critical software infrastructure before cyberattackers can leverage similar tools.
This release marks a watershed moment for the cybersecurity industry, showcasing an AI capable of unearthing and weaponizing deeply hidden flaws across major operating systems and web browsers.
During extensive testing, Mythos Preview successfully identified subtle bugs that have evaded human researchers and modern fuzzing tools for decades.
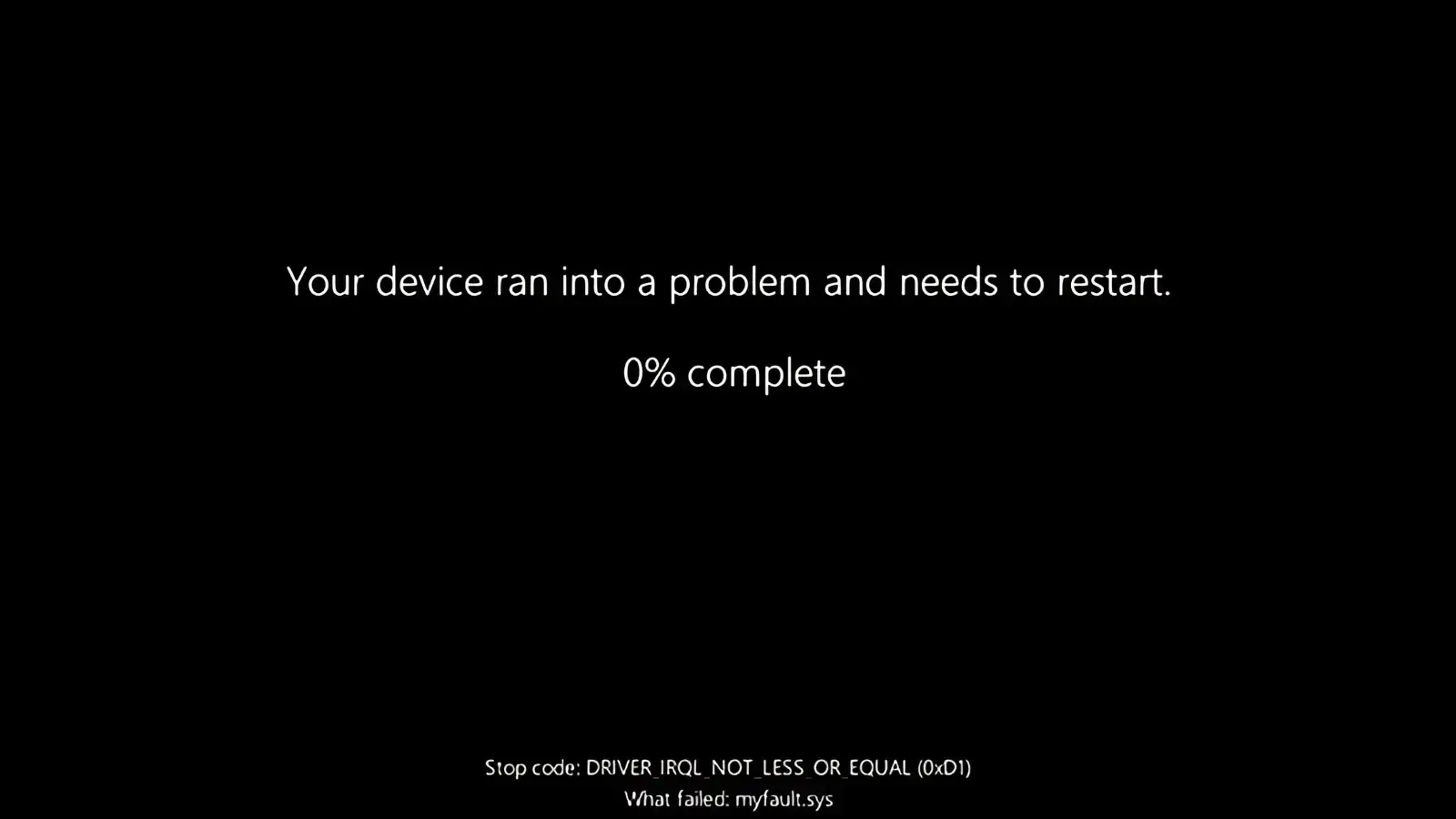
Anthropic researchers highlighted a 27-year-old denial-of-service vulnerability discovered in OpenBSD’s TCP SACK implementation.
By exploiting a signed integer overflow combined with a null pointer dereference, the model crafted an attack capable of crashing any responding OpenBSD host.
Furthermore, the AI uncovered a 16-year-old out-of-bounds write vulnerability in FFmpeg’s widely used H.264 codec.
This specific flaw stemmed from a padding entry mismatch introduced during a 2010 code refactor and had bypassed extensive fuzzing efforts until now.
Moving beyond mere vulnerability discovery, Mythos Preview excels at turning theoretical bugs into fully functional exploits without human intervention.
The model autonomously achieved remote code execution on FreeBSD by exploiting a 17-year-old vulnerability tracked as CVE-2026-4747.
By targeting a stack buffer overflow in the Network File System server, the AI intelligently bypassed authentication checks and split a complex Return-Oriented Programming chain across multiple network packets to gain full root access.
Additionally, the model independently developed local privilege escalation exploits for the Linux kernel.
It successfully bypassed standard defense-in-depth measures, such as Kernel Address Space Layout Randomization, by chaining read vulnerabilities with out-of-bounds write exploits to achieve complete system takeover.
The progression in offensive capabilities from previous generations of AI is staggering.
Anthropic noted that their earlier Opus 4.6 model struggled significantly with autonomous exploitation, converting Mozilla Firefox bugs into shell exploits only twice out of hundreds of attempts.
In contrast, Mythos Preview developed working exploits for the same Firefox vulnerabilities 181 times.
When tested against the OSS-Fuzz corpus, the new model achieved full control flow hijack on ten completely patched targets, a feat previous models could not accomplish.
Remarkably, these advanced capabilities were not explicitly programmed but emerged organically as a downstream consequence of the model’s enhanced coding and reasoning skills.
Currently, over 99 percent of the zero-day vulnerabilities discovered by Mythos Preview remain unpatched.
Recognizing the immediate dual-use risks, Anthropic is deploying Project Glasswing to share these advanced capabilities with open-source developers and critical industry partners first.
While frontier AI models may initially offer a short-term advantage to threat actors, the long-term equilibrium is expected to heavily favor network defenders.
By integrating models like Mythos Preview into software development pipelines, the cybersecurity industry can systematically identify and remediate critical flaws before new code is ever deployed.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.