Apple has introduced a security feature in macOS Tahoe 26.4 that blocks pasting and executing potentially harmful commands in Terminal and alerts users to possible risks.
The new mechanism appears to be aimed primarily at blocking ClickFix attacks and has been reported by macOS users since the release candidate version of the operating system. Apple didn’t specifically mention it in macOS Tahoe 26.4 release notes.
ClickFix is a social engineering technique that tricks users into pasting malicious commands into the command line interface under the pretense of fixing a problem or a verification process.
Since it is the user who pastes the command, existing security measures are bypassed, and malware can be delivered to the system.
To protect users against this type of attack, Apple’s latest macOS version delays executing a potentially malicious command in Terminal when the user pastes it, and shows a warning message about the associated risks.
The message informs the user that no damage has been done to the system, as the command’s execution was halted, and explains that scammers often distribute malicious instructions through various channels.
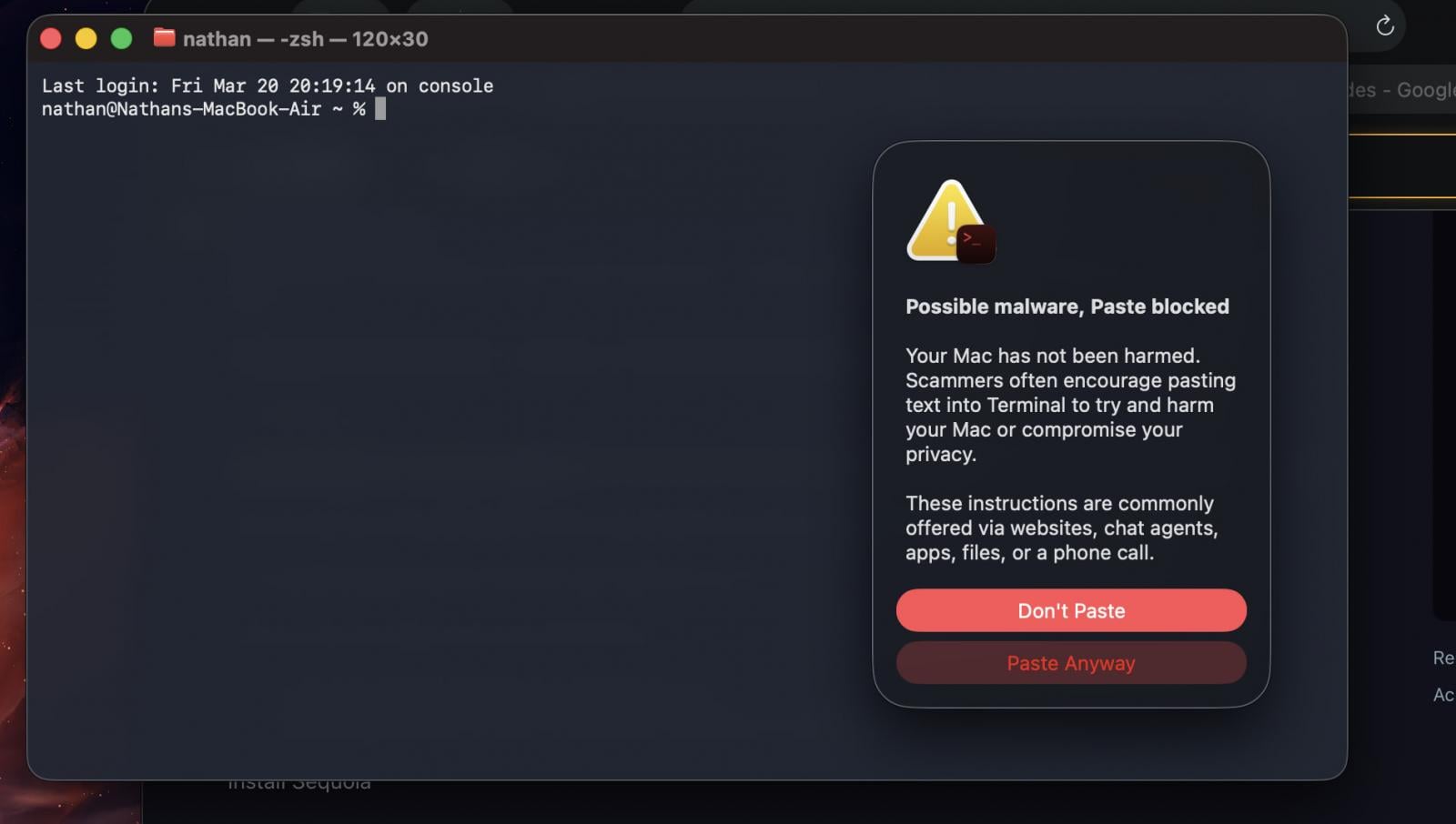
Source: Reddit
Users can choose not to paste the command if they don’t understand what it does and realize that the instructions came from an untrusted source. They can also ignore the warning and continue the action. However, the latter option is recommended only if they understand the effect of the command.
Apple has not published an official support document about this new warning system. Based on user reports, the system displays an alert when users copy commands from Safari and paste them into the Terminal.
One user concluded that these warnings are only delivered once per session, as they tested multiple dangerous commands such as sudo rm -rf /, and no alert appeared. Another suggested that some sort of analysis may occur, because pasting innocuous commands didn’t trigger the warning.
BleepingComputer has contacted Apple for more information, and we will update this post when we get a response.
To defend against ClickFix-based attacks, users of any operating system are strongly advised not to execute commands they find online and do not fully understand what they do.
Also, macOS users should not rely completely on Apple’s new alerts, as it is currently unclear how the system determines the risk of a pasted command to set off an alarm.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.