Apple’s “Find My” location network can be abused by malicious actors to stealthily transmit sensitive information captured by keyloggers installed in keyboards.
The Find My network and application is designed to help users locate lost or misplaced Apple devices, including iPhones, iPads, Macs, Apple Watches, AirPods, and Apple Tags.
The service relies on GPS and Bluetooth data crowd-sourced from millions of Apple devices worldwide to find devices reported as lost or stolen, even if those are offline.
Lost devices send Bluetooth signals in a constant loop detected by nearby Apple devices, which then anonymously relay their location to the owner through the Find My network.
The potential to abuse Find My to transmit arbitrary data besides just device location was first discovered by Positive Security researchers Fabian Bräunlein and his team over two years ago, but apparently, Apple addressed this problem.
The analysts have even published their implementation on GitHub, called ‘Send My,’ which others can leverage for uploading arbitrary data onto Apple’s Find My network and retrieving it from any internet-enabled device anywhere in the world.
Relaying arbitrary data
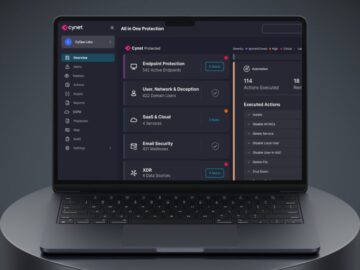
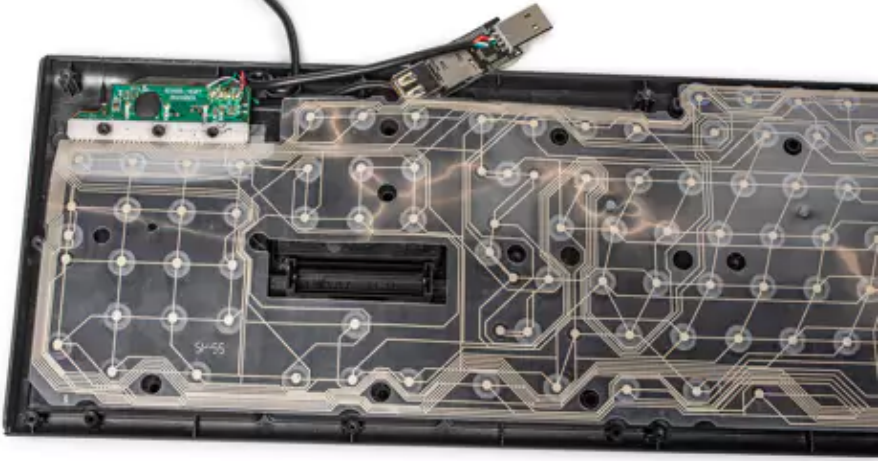
As first reported on Heise, the researchers created a proof-of-concept hardware device to better highlight the risk to the public.
They integrated a keylogger with an ESP32 Bluetooth transmitter into a USB keyboard to show that it’s possible to relay passwords and other sensitive data typed on the keyboard through the Find My network via Bluetooth.
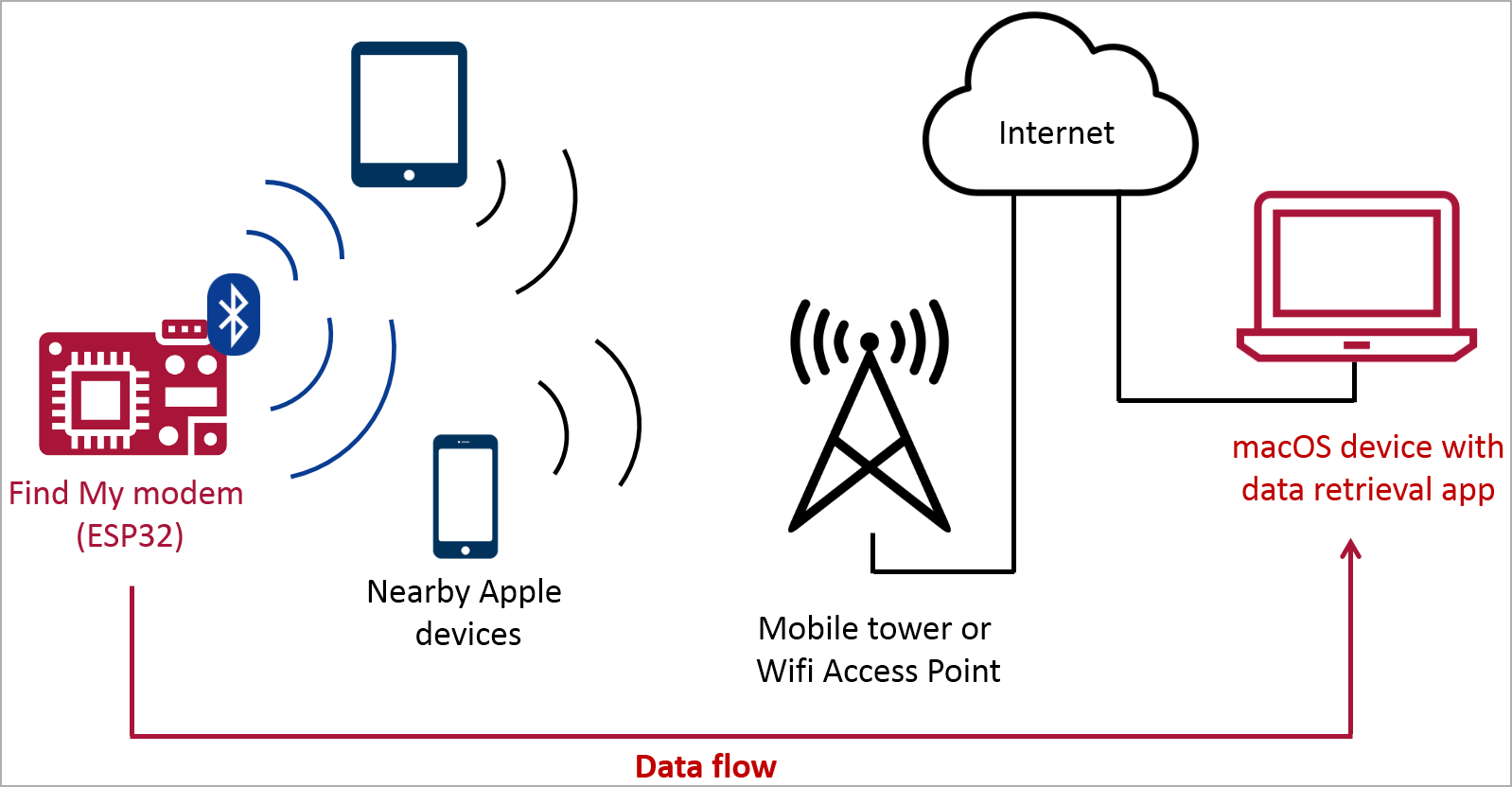
Bluetooth transmission is far stealthier than WLAN keyloggers or Raspberry Pi devices that can be easily noticed in well-guarded environments, and the Find My platform can covertly leverage omnipresent Apple devices for the relay.
The keylogger doesn’t have to use an AirTag or an officially supported chip, as Apple devices are tuned to respond to any Bluetooth message. If that message is appropriately formatted, the receiving Apple device will create a location report and upload it to the Find My network.

Source: Heise
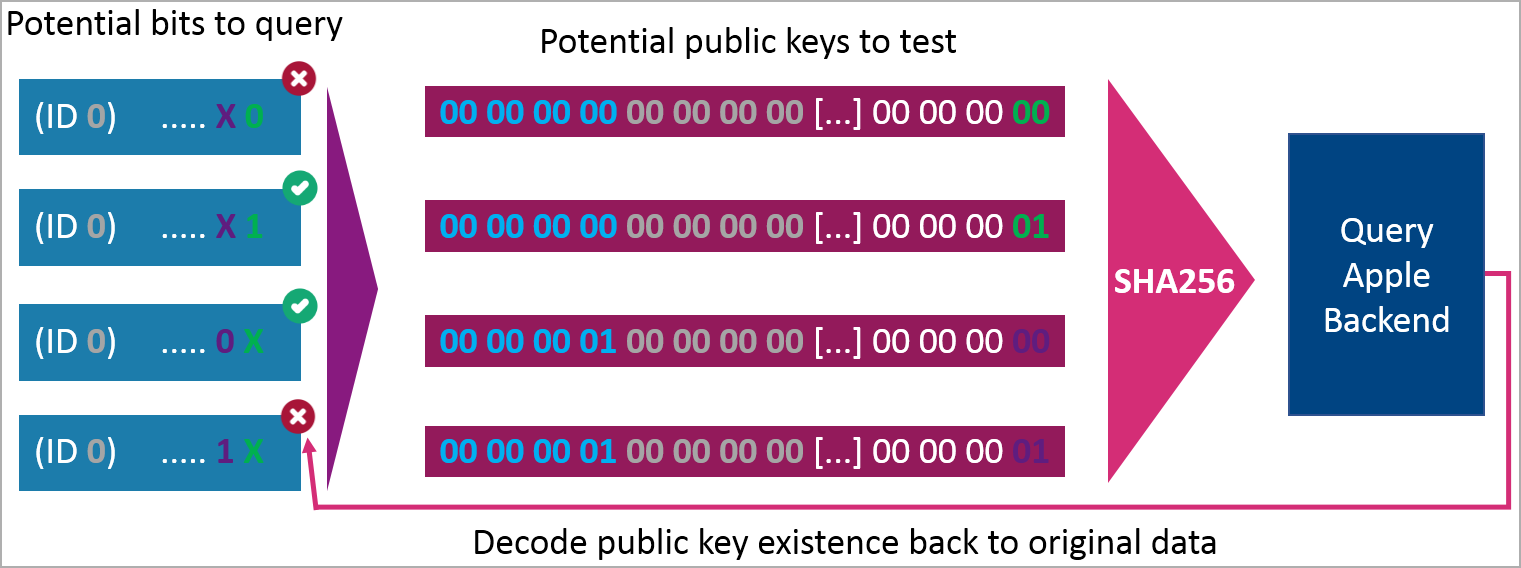
The sender needs to create many slightly different public encryption keys simulating multiple AirTags and encode arbitrary data into the keys by assigning specific bits at predetermined positions in the keys.
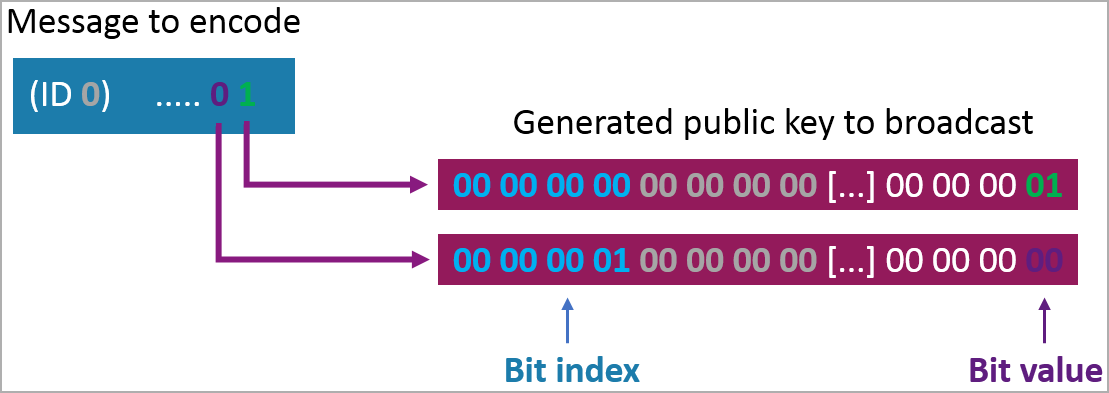
This way, the multiple reports retrieved from the cloud can be concatenated and decoded at the receiving end to retrieve the arbitrary data, in this case, the keylogger’s captures.
Bräunlein explained that the total cost of the data-siphoning contraption was roughly $50, using a Bluetooth-enabled version of the ‘EvilCrow’ keylogger and a standard USB keyboard.
The PoC attack achieved a transmission rate of 26 characters per second and a reception rate of 7 characters/sec, with a latency of between 1 and 60 minutes, depending on the presence of Apple devices at the keylogger’s range.
While this is admittedly not very fast, if recovering valuable information such as passwords is the goal, waiting for several hours or even days wouldn’t be a deal-breaker for malicious actors.
The best part is that Apple’s anti-tracking protections that notify users Air Tags might be tracking them are not activated by the stationary keylogger inside the keyboard, so the device remains hidden and unlikely to be discovered.
BleepingComputer has asked Apple for a statement on the abuse of Find My, but we have not received a response by publication time.