Attackers Exploit RCE Flaw as 14,000 F5 BIG-IP APM Instances Remain Exposed

Over 14,000 F5 BIG-IP APM instances remain exposed online, as attackers actively exploit a critical remote code execution flaw CVE-2025-53521.
Over 14,000 F5 BIG-IP APM instances remain exposed online, with attackers actively exploiting the critical remote code execution vulnerability CVE-2025-53521 (CVSS ver. 3.1 score of 9.8), the nonprofit security organization Shadowserver warns.
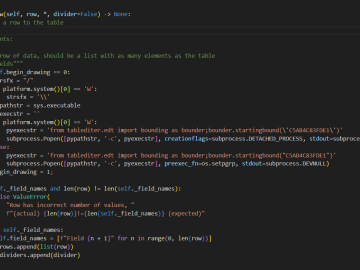
The vulnerability in BIG-IP APM allows specially crafted malicious traffic to trigger Remote Code Execution (RCE) when an access policy is enabled on a virtual server.
“When a BIG-IP APM access policy is configured on a virtual server, specific malicious traffic can lead to Remote Code Execution (RCE).” reads the advisory. “Note: Software versions which have reached End of Technical Support (EoTS) are not evaluated.”
The researchers reported the flaw five months ago, in October. The flaw was previously classified as a Denial-of-Service (DoS) issue, which has been reclassified as a critical Remote Code Execution (RCE) flaw based on new findings in March 2026. Its severity has increased significantly, with higher CVSS scores. The original fix remains effective, but the flaw has been actively exploited in vulnerable BIG-IP versions.
“We have learned that this vulnerability has been exploited in the vulnerable BIG-IP versions below.” reads the vendor’s advisory.
F5 thanks Schuberg Philis, Bart Vrancken, Fox-IT, and the Dutch NCSC for their help in investigating the issue and ensuring a high-standard coordinated disclosure.
Shadowserver now reports tracking over 14,100 IPs with F5 BIG-IP APM fingerprints exposed online, most of them are in the US (5138), Europe (4750), and Asia (2689).
It’s unclear how many are actually vulnerable to exploitation.

At the end of March, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the flaw in F5 BIG-IP AMP to its Known Exploited Vulnerabilities (KEV) catalog.
CISA orders federal agencies to fix the vulnerability by March 30, 2026.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, newsletter)