Hackers Actively Compromising Databases Using Legitimate Commands
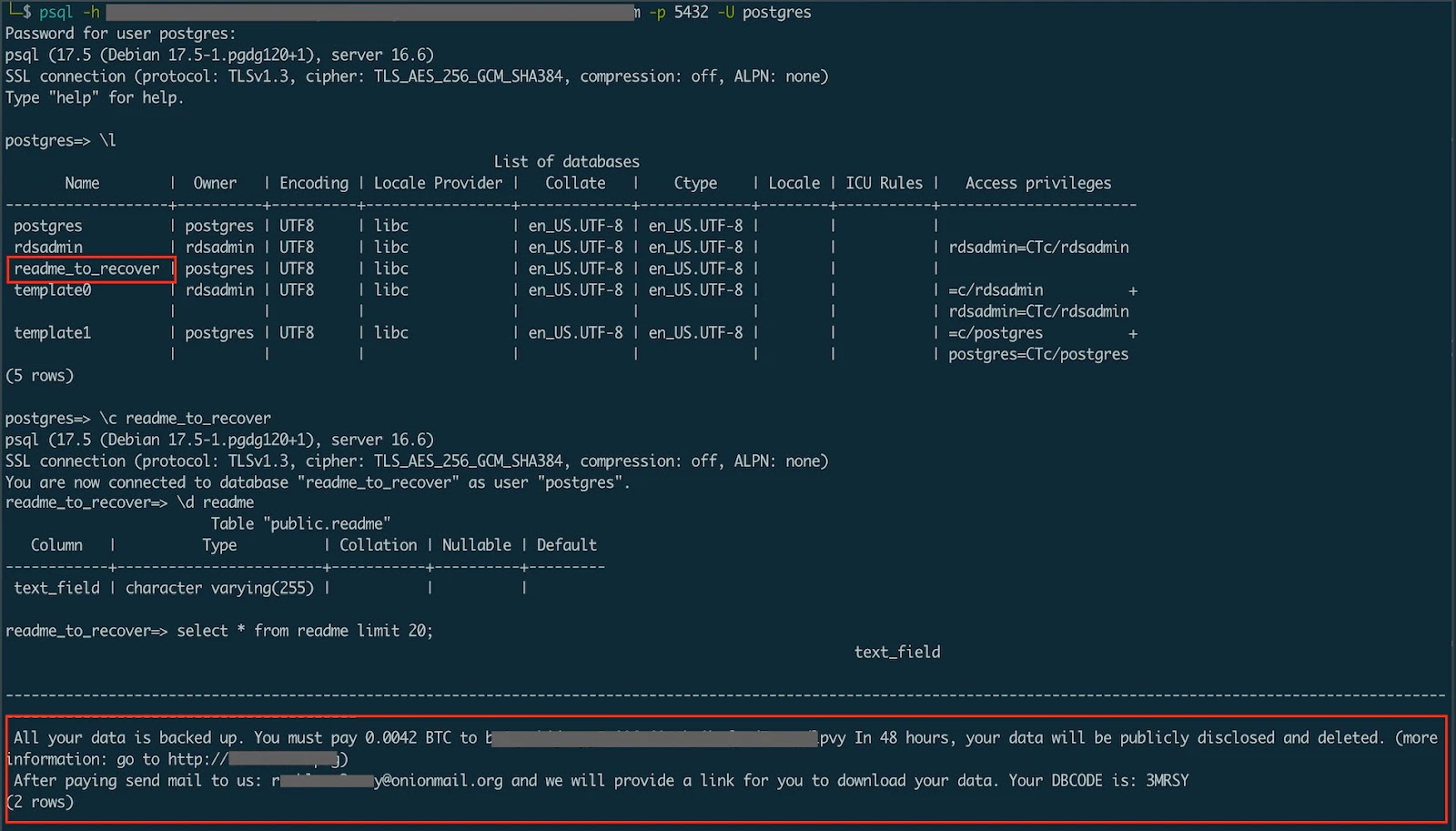
A sophisticated new breed of ransomware attacks is leveraging legitimate database commands to compromise organizations worldwide, bypassing traditional security measures through “malware-less” operations. Unlike conventional…