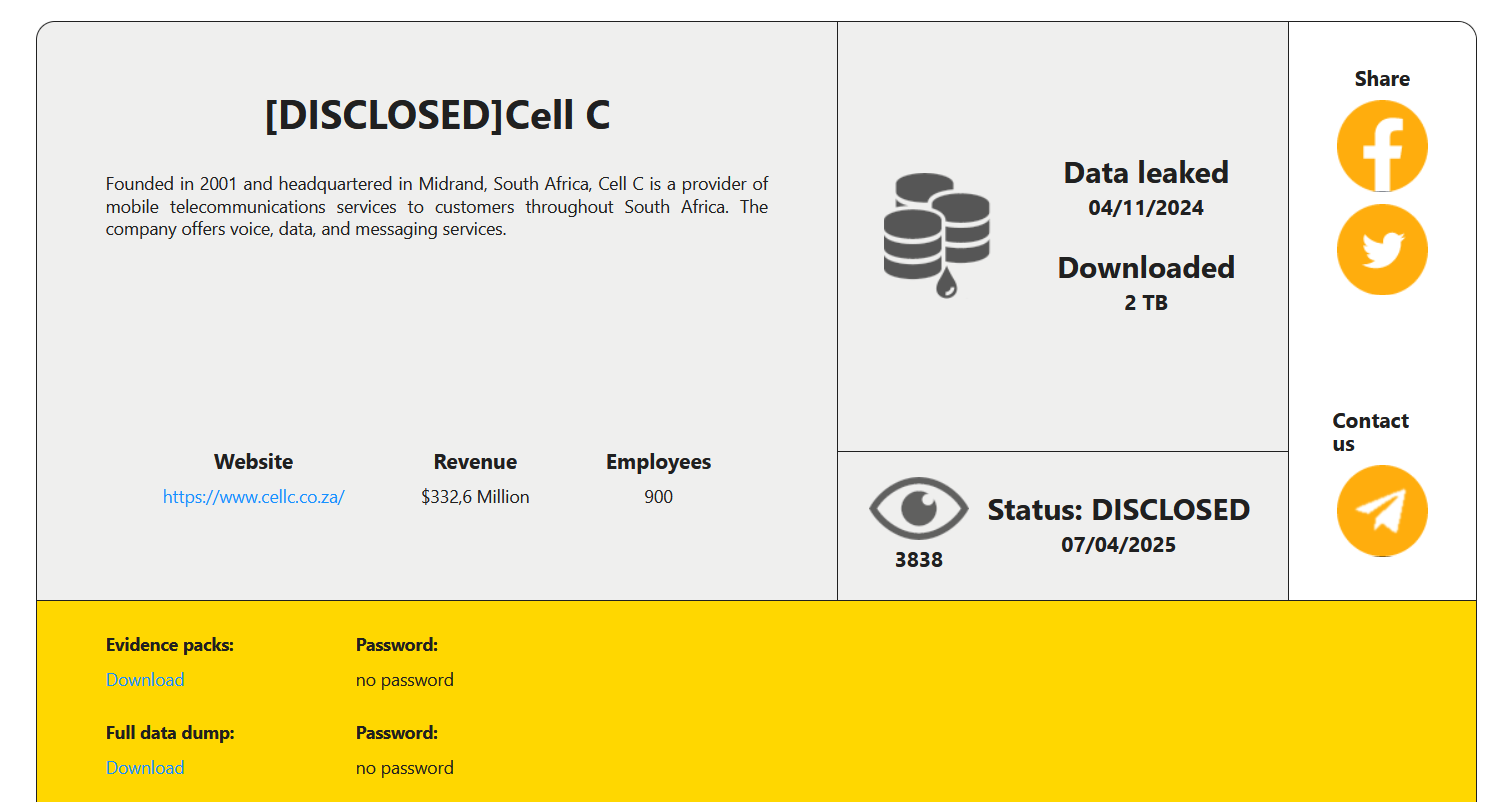
Cybersecurity Leadership in Crisis? CISO Resignations Spike After Major Breaches
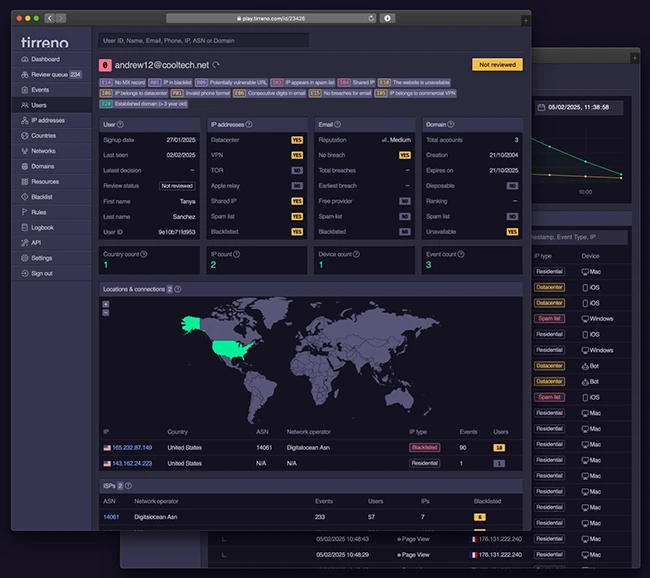
The cybersecurity landscape is witnessing an alarming trend, Chief Information Security Officers (CISOs) are leaving their positions at unprecedented rates. Nearly half of CISOs globally…