Dangling DNS Attack Allows Hackers to Take Over Organization’s Subdomain
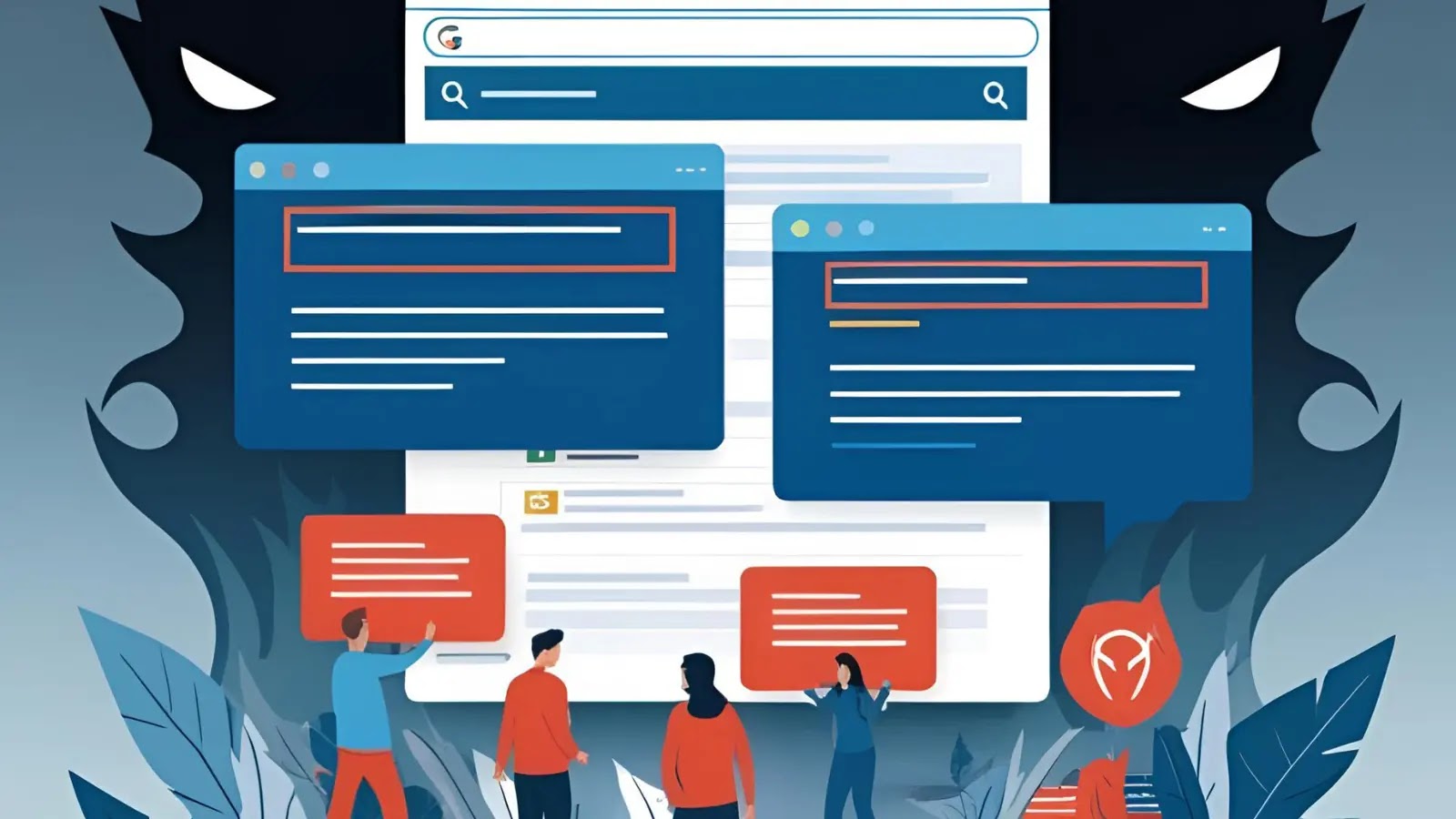
Hackers are exploiting what’s known as “Dangling DNS” records to take over corporate subdomains, posing significant threats to organizations’ security frameworks. This attack vector has…