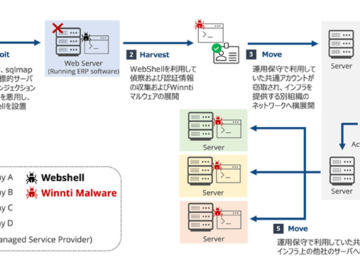
Chinese Hackers Exploit MAVInject.exe to Evade Detection in Targeted Cyber Attacks
Feb 18, 2025Ravie LakshmananCyber Espionage / Malware The Chinese state-sponsored threat actor known as Mustang Panda has been observed employing a novel technique to evade…