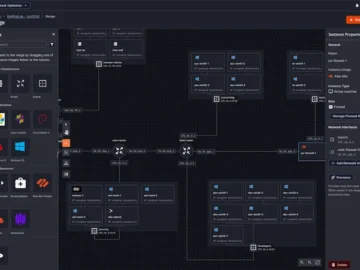
SimSpace Stack Optimizer allows organizations to measure their security technologies
SimSpace launched Stack Optimizer, designed to help organizations evaluate, test, and optimize their security and IT infrastructure. By leveraging SimSpace’s realistic simulated environments, organizations can…