The banking trojan “Grandoreiro” is spreading in a large-scale phishing campaign in over 60 countries, targeting customer accounts of roughly 1,500 banks.
In January 2024, an international law enforcement operation involving Brazil, Spain, Interpol, ESET, and Caixa Bank announced the disruption of the malware operation, which had been targeting Spanish-speaking countries since 2017 and caused $120 million in losses.
At the same time, five arrests and thirteen search and seizure actions occurred across Brazil. However, no information was provided on the arrested individuals’ roles in the operation.
IBM’s X-Force team reports that Grandoreiro appears to have returned to large-scale operations since March 2024, likely rented to cybercriminals via a Malware-as-a-Service (MaaS) model, and now targeting English-speaking countries too.
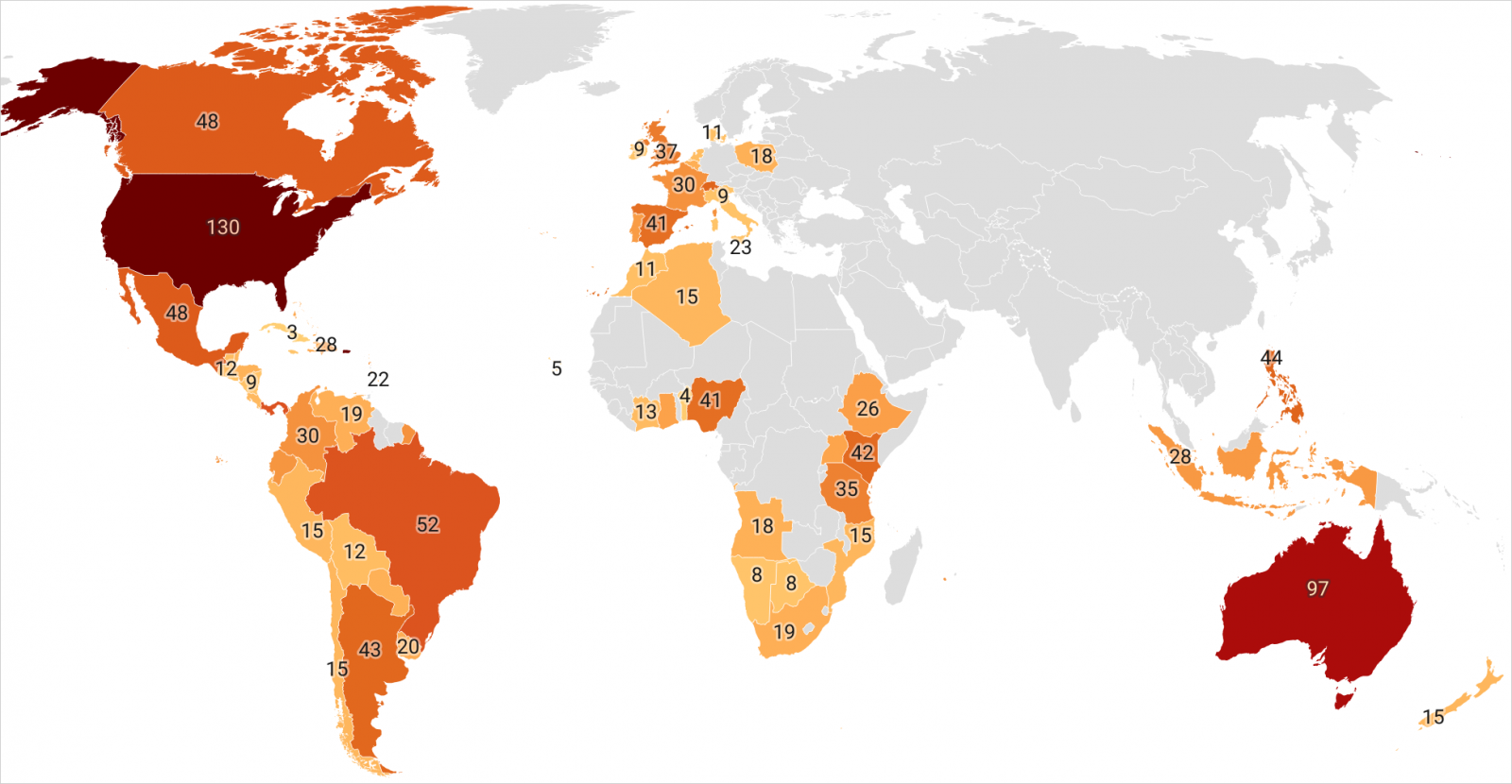
Source: IBM
Additionally, the trojan itself has undergone a technical revamp that added many new powerful features and improvements, indicating that its creators evaded arrest and weren’t deterred by the previous crackdown.
New phishing campaigns
Since multiple threat actors rent the malware, the phishing lures are diverse and crafted specifically for the organizations a particular cybercriminal is targeting.
Phishing emails seen by IBM impersonate government entities in Mexico, Argentina, and South Africa, mainly tax administration organizations, revenue services, and federal electricity commissions.
The emails are written in the recipient’s native language, incorporate official logos and formats, and contain a call to action, such as clicking links to view invoices, account statements, or tax documents.
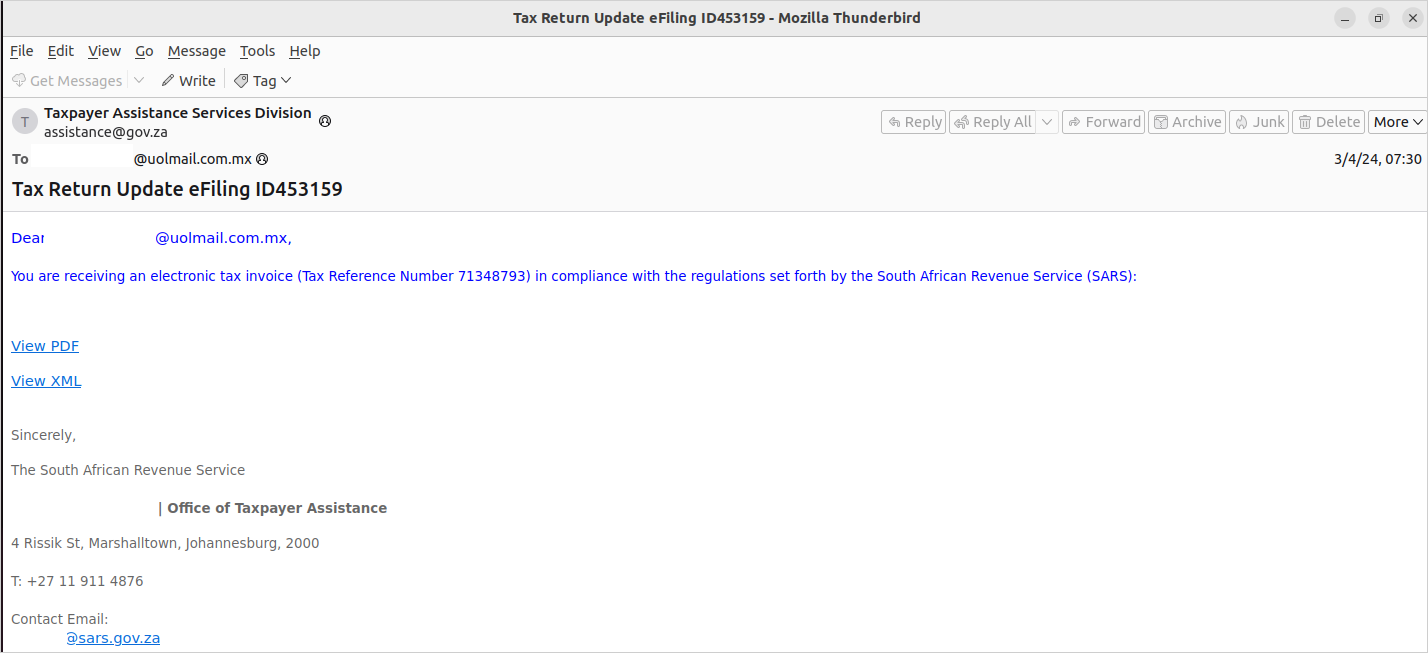
Source: IBM
When recipients click on those emails, they are redirected to an image of a PDF that triggers the download of a ZIP file containing a bloated (100 MB) executable, which is the Grandoreiro loader.
New Grandoreiro features
IBM X-Force noticed several new features and significant updates in the latest variant of the Grandoreiro banking trojan, making it a more evasive and effective threat.
These can be summarized in the following:
- Reworked and improved string decryption algorithm using a combination of AES CBC and custom decoder.
- Updates on the domain generation algorithm (DGA) which now includes multiple seeds to separate the command and control (C2) communications with operator tasks.
- New mechanism that targets Microsoft Outlook clients, disabling security alerts and using them to send phishing to new targets.
- New persistence mechanism relying on the creation of registry Run keys (‘HKEY_LOCAL_MACHINESoftwareMicrosoftWindowsCurrentVersionRun’ and ‘HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun’)
- Expansion of targeting bank applications and inclusion of cryptocurrency wallets.
- Expansion of the command set, now including remote control, file upload/download, keylogging, and browser manipulation via JavaScript commands.
Another notable new feature is Grandoreiro’s ability to perform detailed victim profiling and decide whether or not it will execute on the device, which gives operators better control of their targeting scope.
IBM analysts report that the latest version of the trojan avoids execution in specific countries like Russia, Czechia, the Netherlands, and Poland, as well as on Windows 7 machines in the United States where no antivirus is active.
The above clearly indicates that despite the recent law enforcement action, Grandoreiro is alive and kicking, and unfortunately, it looks stronger than ever.
Update: This article incorrectly said the malware was for Android.