BeatBanker is a new Android malware campaign targeting users in Brazil, combining banking fraud, crypto‑mining, and, in its latest wave, full device takeover via a RAT.
It spreads almost entirely through phishing pages that mimic the Google Play Store and trick victims into installing weaponized APKs disguised as legitimate apps and updates.
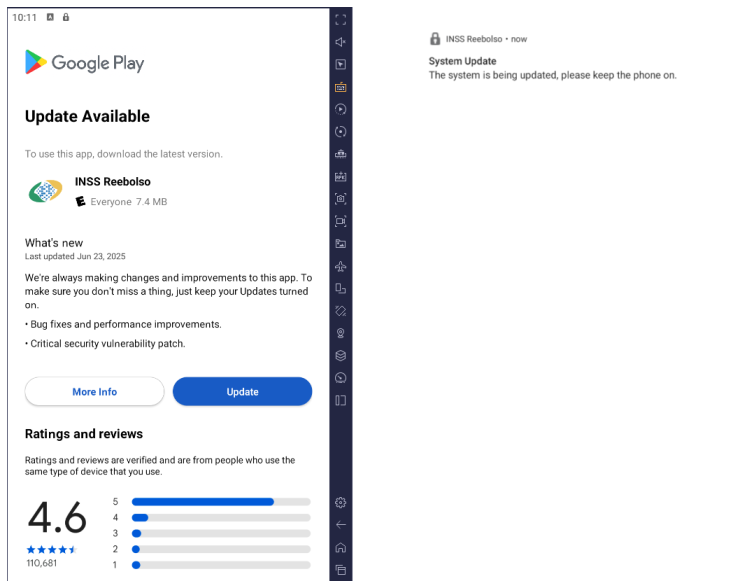
The operation starts on a counterfeit app store hosted at cupomgratisfood[.]shop that visually mimics Google Play.
There, victims are lured with an app called “INSS Reembolso,” posing as Brazil’s official social security portal for benefits, statements and service requests. By abusing this trusted brand, the attackers convince users to sideload a malicious APK that kicks off a multi‑stage infection.
The initial APK is heavily packed and uses a native library (libludwwiuh.so) to decrypt and load additional ELF and DEX components purely in memory.
Recently, uncovered BeatBanker, an Android‑based malware campaign targeting Brazil. It spreads primarily through phishing attacks via a website disguised as the Google Play Store.
To evade mobile security tools, the loader relies on dalvik.system.InMemoryDexClassLoader, anti‑emulation checks and a self‑destruct routine if it detects analysis environments.
Once running, it displays a fake Play Store “update” screen for INSS Reembolso to obtain installation permissions for more hidden payloads.
Crypto Miner, Audio “Heartbeat” and C2
When the user taps “Update,” BeatBanker retrieves an encrypted mining payload from attacker‑controlled domains such as accessor.fud2026[.]com and fud2026[.]com, then decrypts it with a key derived from the filename’s SHA‑1 hash.
ELF) named libludwwiuh.so that is included in the application. Its main task is to decrypt another ELF file that will ultimately load the original DEX file.

The final payload is an ARM‑compiled XMRig 6.17.0 miner that connects to Monero mining pools at pool.fud2026[.]com:9000 or a proxy at pool‑proxy.fud2026[.]com:9000, using TLS and NiceHash‑compatible settings.
The Trojan maintains persistence through a foreground service named KeepAliveServiceMediaPlayback that loops a nearly inaudible five‑second audio file (output8.mp3).
Because media playback keeps the service “active,” Android’s resource management is less likely to kill the process, which inspired the name BeatBanker.
For command‑and‑control, the malware abuses Google’s legitimate Firebase Cloud Messaging (FCM) to receive instructions and telemetry, including battery level, temperature, charging state and user presence, and then adjusts mining activity to avoid detection and overheating.
Beyond mining, BeatBanker drops a second APK (INSS Reebolso, package com.destination.cosmetics) that acts as a dedicated banking Trojan.
It again anchors itself via fixed foreground notifications and pushes the user to grant Accessibility permissions, gaining broad control over the interface.
The malware continuously monitors the foreground app and specifically targets Binance and Trust Wallet during USDT transactions.
When a withdrawal is initiated, BeatBanker instantly overlays the real confirmation screen with a fake HTML page stored in Base64 inside the banking module.
Its ecosystem is actively promoted across GitHub, Telegram, YouTube and dark‑web forums, where leaked source code is traded, making it easier for actors like the BeatBanker operators to integrate it as a final payload.
It captures the original address and amount, silently replaces the destination wallet with an attacker‑controlled USDT address via AccessibilityNodeInfo.ACTION_SET_TEXT, and shows the victim either the copied address (Binance) or a loading spinner (Trust Wallet) so the fraud goes unnoticed.
The module also monitors popular browsers to collect visited domains and remotely open attacker‑supplied links.
From Banker to BTMOB RAT
In a newer wave, the operators swapped the custom banking module for BTMOB, a powerful Android RAT that evolved from CraxsRAT, CypherRAT and SpySolr and is sold in a Malware‑as‑a‑Service model.
Ultimately, the modified byte array contains the original text, which is then converted to UTF-8 and returned as a string.

These samples have been seen posing as a fraudulent StarLink application and reuse the same tricks: fake Play‑style pages, looping audio, fixed notifications and bundled crypto miner.
BTMOB is heavily obfuscated but retains a rich feature set: persistent background execution, protection against uninstall and reset, real‑time screen recording, keylogging, live screen sharing, file and SMS control, and access to both cameras and GPS.
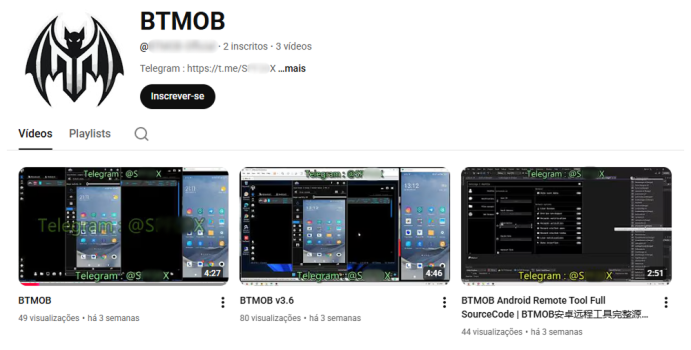
So far, all observed BeatBanker variants – both banker and BTMOB‑based – have been detected on Android users in Brazil, with evidence that some BTMOB infections also propagate via WhatsApp links alongside phishing pages.
The campaign shows how mobile threats now blend stealthy mining, financial fraud and full remote control into a single, persistent implant.
To reduce exposure, Android users should: only install apps from official stores and verify publishers, scrutinize requests for Accessibility and “install unknown apps” permissions, and keep both the OS and mobile security tools fully updated.
Enterprise defenders should also monitor for connections to the listed BeatBanker and BTMOB infrastructure and block known domains such as cupomgratisfood[.]shop and fud2026[.]com at the network layer.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.