The latest campaign, they have switched to misusing a legitimate remote administration tool called NetSupport RAT.
A cybercriminal group known as “Stan Ghouls” (or Bloody Wolf) has launched a fresh wave of attacks targeting organizations across Central Asia and Russia.
Active since at least 2023, this group focuses heavily on the manufacturing, finance, and IT sectors. While they have historically attacked multiple countries, their most recent campaign has aggressively targeted Uzbekistan, claiming approximately 50 victims there.A Shift in Tactics
Security researchers monitoring Stan Ghouls have noticed a distinct change in their methods. Previously, the group relied on a specific type of malicious software called STRRAT (Strigoi Master).
By using legitimate software that IT teams actually use, the attackers hope to blend in and avoid detection while gaining full control of infected machines.
How the Attack Works
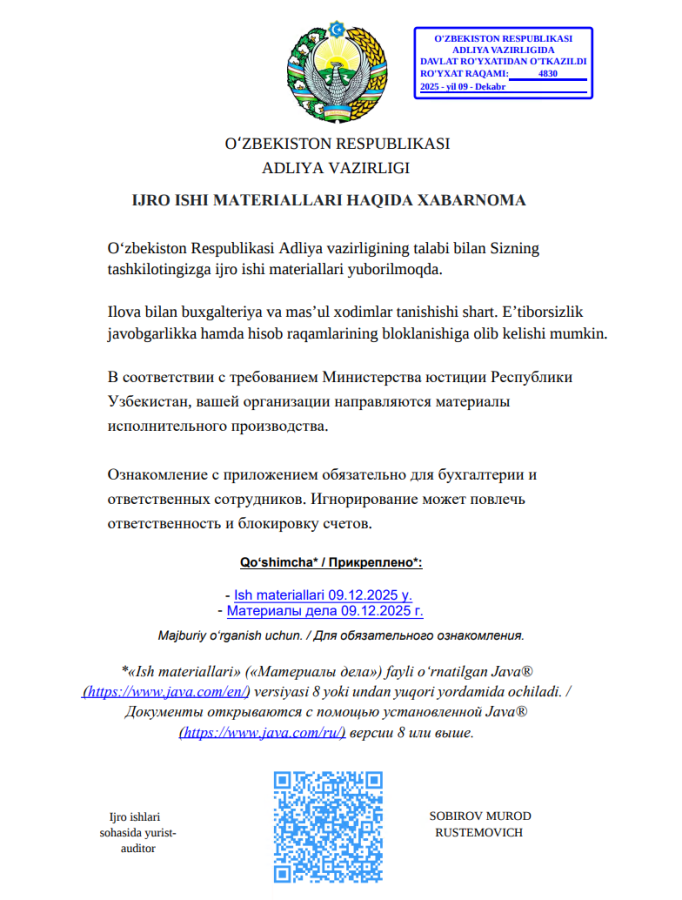
The attack begins with a spear-phishing email written in the local language of the target, such as Uzbek or Kyrgyz, rather than English or Russian.
The attachment was a malicious PDF file titled “Постановление_Районный_суд_Кчрм_3566_28-01-25_OL4_scan.pdf”.
These emails often pretend to be official government or legal notices, such as a district court order or a request for a retrial.
Attached to the email is a PDF document. When a victim opens this decoy file, they see a link claiming to contain “case materials.”
The document instructs the user that they must have Java installed to view the files. Clicking the link downloads a malicious Java file (a JAR loader) instead of a legitimate document.
Once the user runs the downloaded Java file, the malware performs several clever checks to ensure it is running on a real victim’s computer rather than a security researcher’s test environment:
- Fake Error Message: It immediately displays a fake error saying the application cannot run on the current operating system, tricking the user into thinking the file is broken.
- Limit Check: The malware counts how many times it has been installed. If it has been run more than three times, it stops working and displays an error message saying the “attempt limit is reached”.
If these checks pass, the loader connects to a malicious domain and downloads the NetSupport RAT files, including the main executable client32.exe.
Expanding to Smart Devices?
To ensure they maintain control even after the victim restarts their computer, Stan Ghouls uses three different methods to make the malware start automatically:
- Startup Folder: It drops a script into the Windows Startup folder.
- Registry Key: It adds a launch command to the Windows Registry.
- Scheduled Task: It creates a system task that runs the malware every time a user logs in.
Interestingly, researchers found evidence that Stan Ghouls might be branching out. On servers used in previous campaigns, files associated with the “Mirai” malware were discovered.
Mirai is infamous for attacking Internet of Things (IoT) devices like smart cameras and routers.
While it is not confirmed if Stan Ghouls is directly using Mirai or simply sharing infrastructure with other hackers, it suggests the group may be looking to expand its arsenal beyond standard computers.
With over 60 confirmed victims in this specific campaign alone, Stan Ghouls has proven to be a resourceful and evolving threat that requires constant vigilance from organizations in the targeted regions.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.