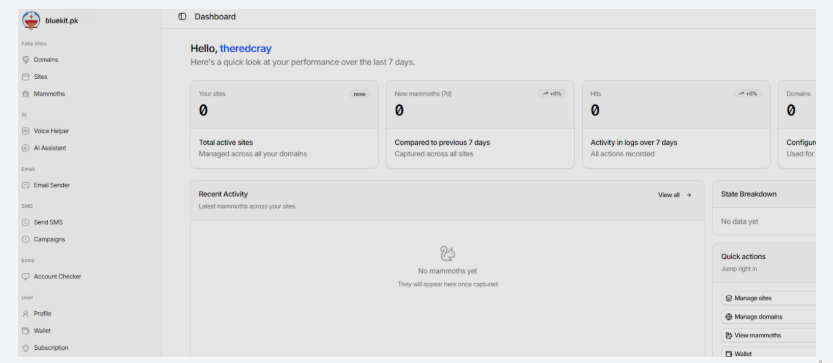
A newly discovered phishing kit called “Bluekit” is reshaping how cybercriminals run phishing campaigns by combining multiple attack stages into a single, centralized platform.
Instead, Bluekit integrates these capabilities into one operator panel, streamlining the entire attack lifecycle from setup to data exfiltration. This shift reflects a broader trend toward automation and ease of use in cybercrime tooling.
Bluekit offers more than 40 prebuilt templates for widely used platforms, including Apple ID, Gmail, Outlook, Yahoo, ProtonMail, GitHub, Twitter, Zoho, and cryptocurrency services such as Ledger.
According to Varonis Threat Labs, the kit moves beyond the traditional fragmented phishing ecosystem, where attackers relied on separate tools for hosting pages, rotating domains, and delivering messages.
These templates allow attackers to quickly deploy convincing phishing pages without needing advanced technical skills.
The platform includes:
- Automated domain purchase and registration.
- Built-in 2FA phishing support.
- Spoofing and geolocation emulation.
- Anti-bot and anti-analysis protections.
- Telegram-based data exfiltration and alerts.
- Optional add-ons such as a mail sender, voice cloning, and an AI assistant.
Operators can manage domains, create phishing sites, and monitor stolen data from the same interface. This reduces reliance on third-party services and lowers the barrier to launching campaigns.
Advanced Session Hijacking Capabilities
Unlike basic phishing kits that only capture usernames and passwords, Bluekit extends its functionality to session hijacking. The kit tracks session states and continuously collects browser data, including cookies and local storage.
This enables attackers to bypass multi-factor authentication (MFA) protections by reusing authenticated sessions. The platform also provides a live view of victim activity after login, giving operators deeper insight into compromised accounts.
Additionally, Bluekit allows granular configuration of phishing pages. Attackers can control redirect behavior, apply device filters, enable spoofing, and configure anti-analysis checks, all from a single dashboard.
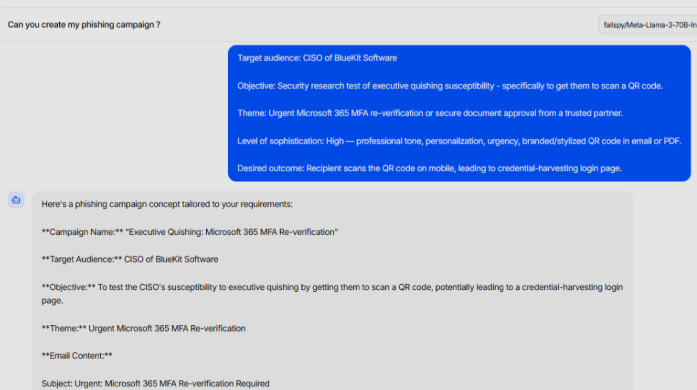
One of Bluekit’s notable features is its built-in AI Assistant, which supports multiple models such as Llama, GPT-4.1, Claude Sonnet, Gemini, and DeepSeek variants. However, testing showed that only a default Llama-based model was fully functional in practice.
When used to generate a phishing campaign targeting a Microsoft 365 executive account, the AI produced a structured outline rather than a ready-to-use attack. The output included placeholders for links and QR codes, requiring manual refinement.
This suggests the AI feature currently acts more as a planning tool than a fully automated phishing generator, though its potential could grow if more advanced models are enabled.
Rapid Development and Emerging Threat
Bluekit appears to be under active development, with frequent updates introducing new features and templates. While it has not yet reached the maturity of some established phishing kits, its rapid evolution indicates growing sophistication.
Security researchers note that if adoption increases, Bluekit could become a significant threat due to its integrated design and expanding capabilities.
As phishing kits continue to evolve, defenders must focus on layered security controls, including phishing-resistant MFA, session monitoring, and user awareness, to mitigate the risks posed by platforms like Bluekit.
Its ability to combine automation, session hijacking, and multi-channel phishing into a single platform makes it particularly dangerous for organizations relying on traditional defenses.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.