Seven new BPFDoor variants that push Linux backdoor tradecraft deep into the kernel, making them harder to spot in large telecom networks.
These implants use Berkeley Packet Filters (BPF) to quietly inspect traffic inside the operating system kernel, waiting for a “magic packet” that activates a hidden shell.
Once triggered, the backdoor blends into normal processes and network flows, giving attackers long‑term access with minimal noise.
The standout change in these variants is how command‑and‑control (C2) is handled. Instead of relying on fixed C2 servers or hardcoded IPs, the malware can treat the source of the magic packet as the C2 endpoint, turning the infrastructure into a stateless controller.
A special “Hidden IP” (HIP) field and a -1 flag allow the backdoor to ignore any embedded C2 address and call back to the sender, even if the attacker is behind a NAT or VPN.
Both the httpShell and icmpShell variants also introduce ICMP‑based relay, effectively turning infected hosts into invisible routers.
New research from Rapid7 Labs has uncovered undocumented features leading to the discovery of 7 new BPFDoor variants.
By reading an internal target IP from the HIP field, rewriting flags to “magic” ICMP values, and forwarding crafted Echo Requests, BPFDoor can laterally move across internal segments without opening traditional ports.
This piggybacks on the fact that organizations often allow ping traffic and rarely inspect ICMP deeply.
HTTP tunneling and “magic ruler”
httpShell focuses on hiding C2 inside HTTP traffic over both IPv4 and IPv6. It binds to all interfaces and lets the kernel decapsulate complex tunnels such as GRE or GTP, so the BPF logic only has to look at inner packets for specific magic markers.
A “magic ruler” padding scheme ensures the 4‑byte trigger value always lands at the same byte offset, even when proxies and WAFs add or shift headers, allowing the backdoor to survive heavy Layer 7 manipulation.
However, the IPv6 implementation has limitations. The filter assumes a simple IPv6 header without extension headers, so if extra headers are present and push the payload further down, the backdoor may never wake up.
This creates a narrow but useful detection angle for defenders who can look for BPF filters, making such assumptions in high‑value environments.
The ICMP Shell variant is designed for highly locked‑down environments where classic outbound channels are restricted.
It establishes an interactive shell entirely over ICMP, using a dynamic BPF filter that binds to the malware’s current process ID so that each run requires a different “magic knock” pattern. This breaks static firewall rules and signature‑based triggers that expect fixed magic bytes.
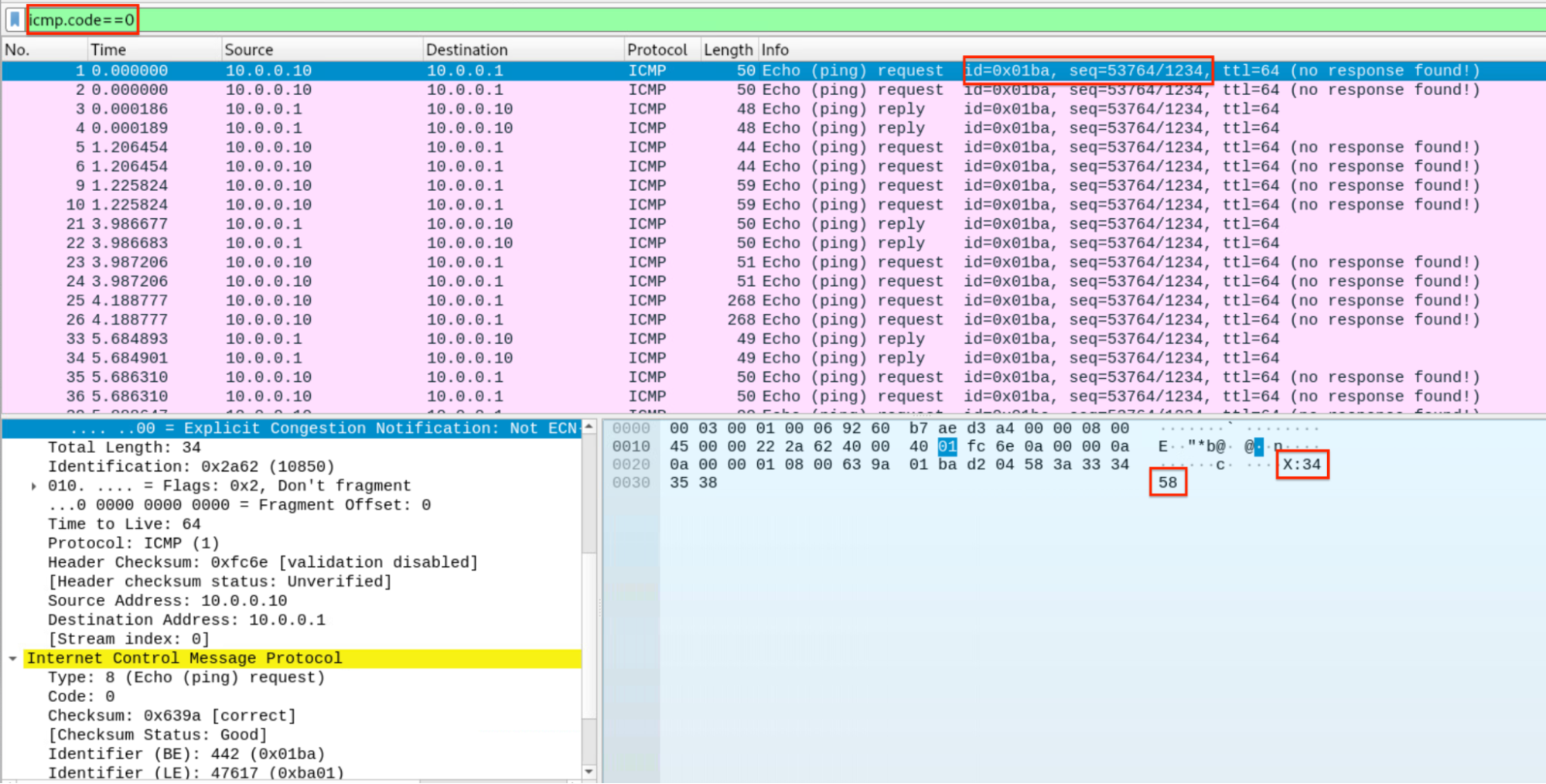
Once active, icmpShell supports bidirectional ICMP tunnels, UDP/ICMP “hole‑punching,” and RC4 encryption for returning shell output, while attacker commands may travel in cleartext with recognizable prefixes like “X:”.
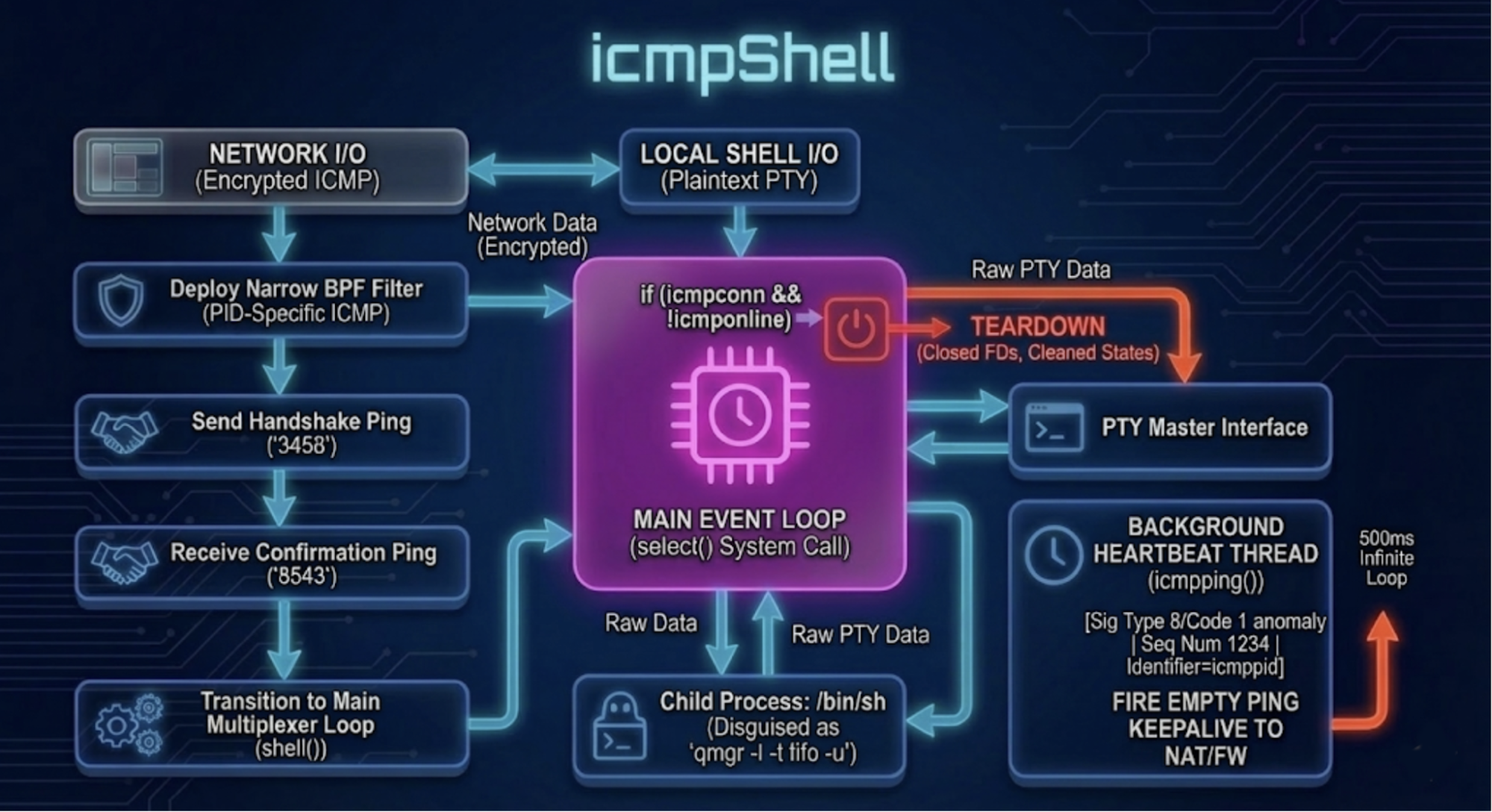
It also uses hardcoded ICMP sequence numbers and technically invalid ICMP codes for heartbeat messages, which become reliable structural markers for network intrusion detection systems tuned to watch ICMP flows.
Additional variants and active beacons
Beyond httpShell and icmpShell, Rapid7 tracks multiple lettered variants that specialize in stealth and resilience.
The tcpdump screens highlighting ICMP handshake, shell’s data encryption, attacker’s command and the usage of 1234 ICMP sequence number hardcoded in the backdoor.
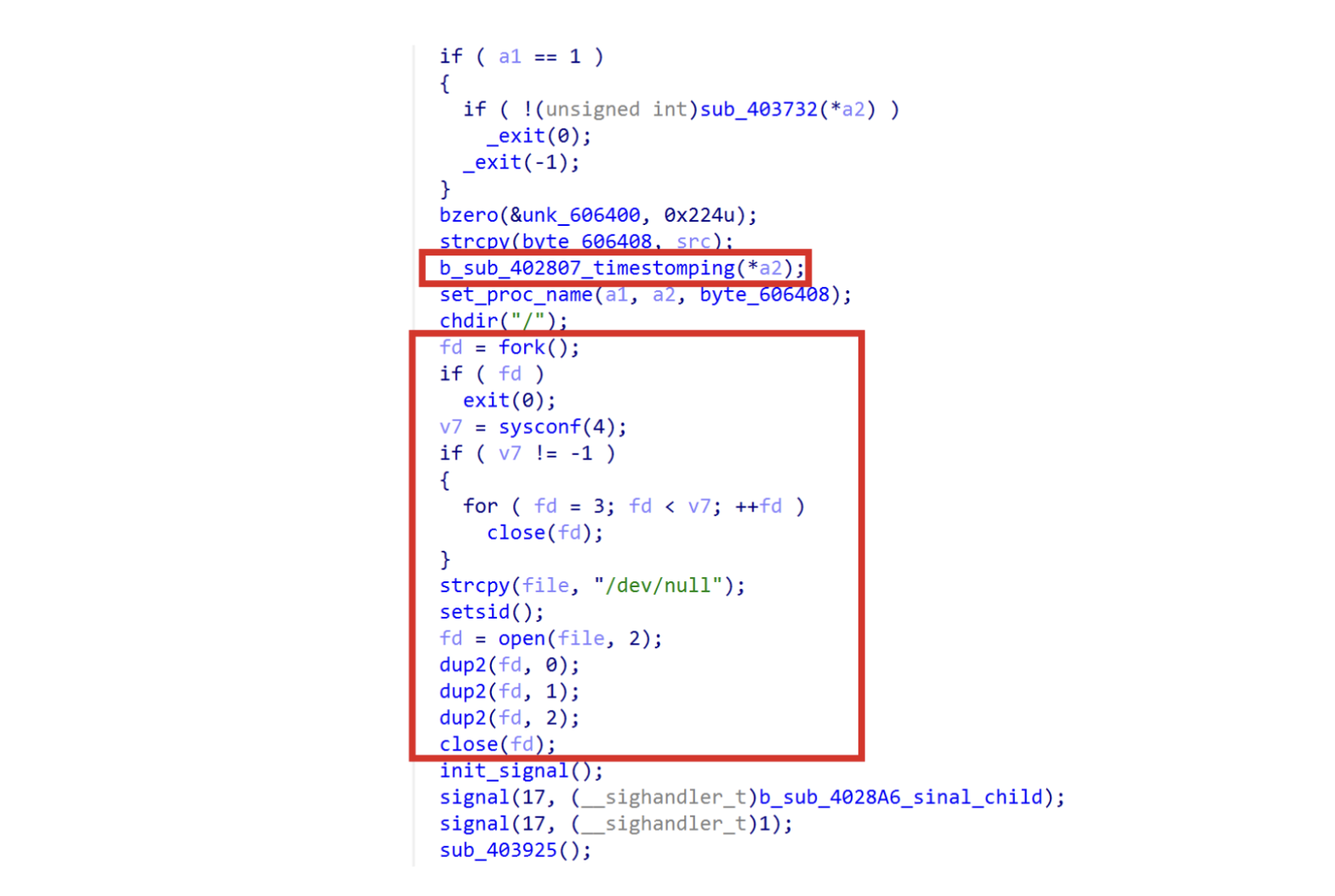
Some hide under paths like /var/run/user/0 and aggressively wipe file descriptors and timestamps to frustrate forensics, while others spawn three protocol‑specific raw sockets (TCP, UDP, ICMP) in parallel to avoid missing magic packets and to offer fallback C2 channels if one protocol is blocked.
One notable “H” variant introduces an active beacon that periodically resolves NTP‑themed domains and opens encrypted sessions over TCP 443 using legacy OpenSSL and RC4‑MD5, masquerading as time synchronization or IoT telemetry.
Most samples simply redirect output to /dev/null. This variant goes further by performing a total FD (File Descriptor) wipe.
By hiding C2 inside what looks like routine SSL traffic to plausible hostnames, the malware can maintain access even in environments that heavily filter inbound connections but allow outbound HTTPS.
Their published YARA and Suricata rules, plus a dedicated triage script to enumerate active BPF filters, aim to help teams detect both legacy and new BPFDoor variants before they become long‑term sleeper cells in telecom backbones.
Because these implants live in the kernel and depend on BPF logic, defenders must move beyond simple IoCs and payload signatures.
Rapid7 recommends focusing on structural anomalies such as unusual BPF filters on AF_PACKET or raw sockets, hardcoded ICMP sequence numbers and invalid ICMP codes, and processes that masquerade as common daemons but have suspicious execution paths.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.