Breaking Into Systems With Permission AKA Pentesting

Source link
Related Articles
All Mix →A complete guide for beginners
Table of Contents 1) Hunt on a single target for an extended amount of time. 2) Map out targets on wide-scope programs 3) Read the…
UL NO. 433: China’s Flawed Strategy
Table of Contents TOC NOTES Would you be interested in buying/reading this book? MY WORK SECURITY TECHNOLOGY HUMANS IDEAS & ANALYSIS RECOMMENDATION OF THE WEEK…
How to Create Technical Documentation Using ChatGPT
Table of Contents Quality Code Basics In-Depth Documentation Inline Documentation A Few Tips Subscribe I’ve maintained for years that good code isn’t that great without…
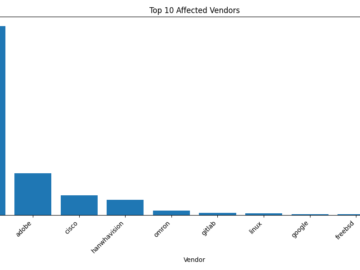
Weekly Vulnerability Trends Report – 2024-07-12 – Web Security Services
Table of Contents This Week’s Vulnerability Landscape Top Affected Vendors Severity Distribution Trending CWEs Key Takeaways This Week’s Vulnerability Landscape Welcome to our weekly vulnerability…
The Top 5 Most Common Security Issues I Discover When Reviewing Code
Table of Contents 1. Sensitive Information in Log Files 2. Poor Cryptography Choices 3. Insufficient Access Controls 4. Unsecured Caches 5. Trusting the Client Too…
Introducing The Tech Leader Docs
A new resource for software development leaders by Victoria Drake. I’m launching a brand new paid newsletter on Substack focused on building, growing, and leading…