Broken Access Control – Lab #11 Insecure direct object references | Short Version

Source link
Related Articles
All Mix →Say Yes To Cyber Help
In 2016, the DoD said Yes to cyber help by launching the Hack the Pentagon program. It took 13 minutes for them to receive their…
Detectify is #4 on Internetworld’s 2015 startup list
2015 ended on a high note for Detectify! Internetworld published their annual list of Sweden’s most exciting startups and we’re #4! Internetworld’s list is a…
H1–212 Capture the Flag Write up. Introduction to the challenge and… | by Alyssa Herrera
Capture the flag events are particular fun events done to challenge people and get people to really think about the puzzle they’re presented with. They…
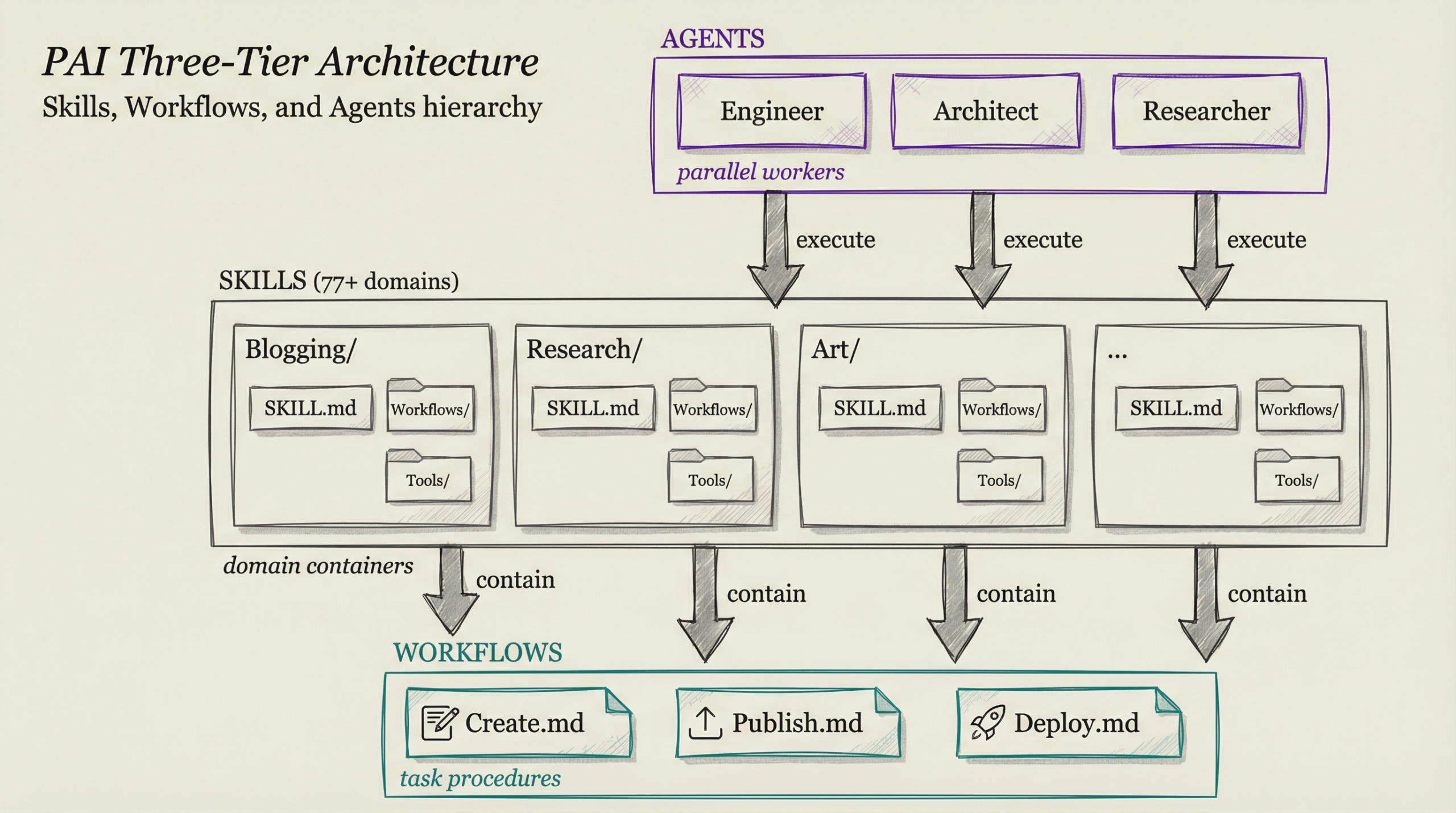
When to Use Claude Code Skills vs Workflows vs Agents
Table of Contents The Quick Answer The Hierarchy Skill Structure Skill Anatomy: SKILL.md The Three Tiers Explained Tier 1: Skills (Domain Containers) Tier 2: Workflows…
Tips for Parents Working from Home from HackerOne Employees
Table of Contents 1. Schedule Downtime 2. Prioritize Self-Care 3. Integrate Family with Work 4. Cherish Quality Moments 5. Plan Ahead 6. Know Your Limits…
Be brave and build in public
Make every day feel like Christmas when you participate in open source communities. I used to think that when I wanted to make updates to…