Broken Access Control – Lab #6 Method-based access control can be circumvented | Long Version

Source link
Related Articles
All Mix →Improve your e-commerce website security – check your site with Detectify
Detectify is an automated web security scanner that helps you discover vulnerabilities and ensure your site is safe from hackers. Whether you’re running a Magento…
3-Phased Information Processing: The IT Meta-skill
Having worked in IT for a good bit of time I have thought a lot about various information technology skillsets and which will become more…
Newly added security tests, October 4, 2017: WordPress and Magento vulnerabilities
This week’s update brings more WordPress plugin vulnerabilities that Detectify now checks for as well as two Magento security tests. We have added: WordPress Authenticated…
[tl;dr sec] #200 – LLM → Tailored IR Scenario, How to Secure Your GitHub/GitLab, Cloud Storage Threat Matrix
Table of Contents 📺️ Almost…. there! 📣 Who knows what data lurks in the depths of your emails? AppSec Web Security 📣 Smart device virtualization…
Hacking and Grinding: The Balance Between Passion and Self Control
I think a lot about what makes people successful, both in a general sense and also on an individual basis. The model I’ve been working…
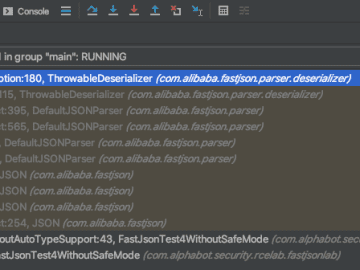
Fastjson: exceptional deserialization vulnerabilities – Alphabot Security
Table of Contents Intro Typical Fastjson RCEs (using the autoType-feature) Now it gets interesting… The global Fastjson instance How many autoType checks? But can you…