Broken Access Control – Lab #7 User ID controlled by request parameter | Long Version

Source link
Related Articles
All Mix →Migrating to the cloud but without screwing it up, or how to move house
Table of Contents Re-host Re-platform Re-factor A practical guide to moving to cloud services with minimal downtime, using AWS examples. For an application that’s ready…
How Planes Fly: What They Taught You In School Was Wrong
So we all know how planes fly, right? The top of the wing is rounded and the bottom of the wing is more straight. Air…
Scaling security automation with Docker
Table of Contents What is Docker? How hackers currently scale automation Docker automation scaling Making things even easier with Docker Compose How to scale automation…
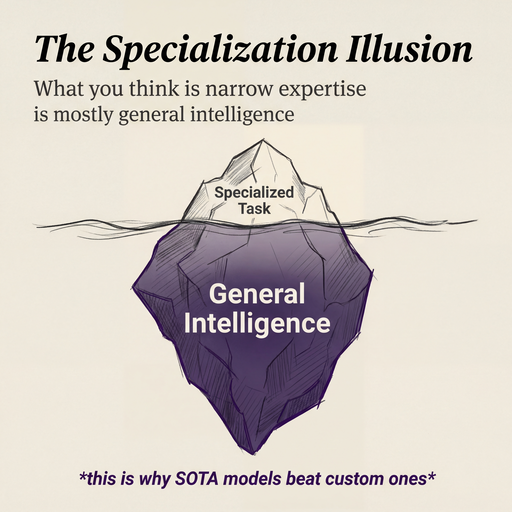
Why I believe in SOTA models over custom ones
I’ve never been a big believer in training custom models. I’ve also never believed in fine-tuning. Going all the way back to 2023, my intuition…
Computer Fraud and Abuse Act | Proposed CFAA Changes
Many security professionals, hackers, lawyers, law enforcement, and members of the media are keenly interested in the White House’s proposed changes to laws affecting Internet…
Purposelessness—Not Social Media—is Causing Our Kids’ Depression
Table of Contents Comparison as the thief of joy The explanatory power of the Purpose Problem Ok, but what do we do? Summary Social media…