Broken Access Control – Lab #8 UID controlled by parameter, with unpredictable UIDs | Short Version

Source link
Related Articles
All Mix →Wallarm Research Releases Nuclei Template to Counter Threats Targeting LLM Apps
Wallarm Research has just released a powerful new Nuclei template targeting a new kind of exposure: the Model Context Protocol (MCP). This isn’t about legacy…
[Alert] New WordPress XSS Vulnerability Discovered
Are you running WordPress 4.2.0 to 4.5.1? Time to upgrade to 4.5.2! It was recently discovered that WordPress versions 4.2.0 to 4.5.1 are vulnerable against a reflected…
The Impacts of Cross-site Scripting (XSS) [With Real Examples]
Table of Contents What Is Cross-Site Scripting (XSS)? What Industries Are Impacted By Cross-site Scripting? A Real-world Example of a Cross-site Scripting Vulnerability Summary Impact…
Wireless: WPA2 Enterprise Integration With Active Directory 2008 Using NPS
Table of Contents Setup 1. Install AD and Create Users 3. Configure Your Wireless Access Point 4. Configure Your Clients Fin So I finally got…
How to send long text input to ChatGPT using the OpenAI API
A straightforward guide to sending large input to ChatGPT using Python. In a previous post, I showed how you can apply text preprocessing techniques to…
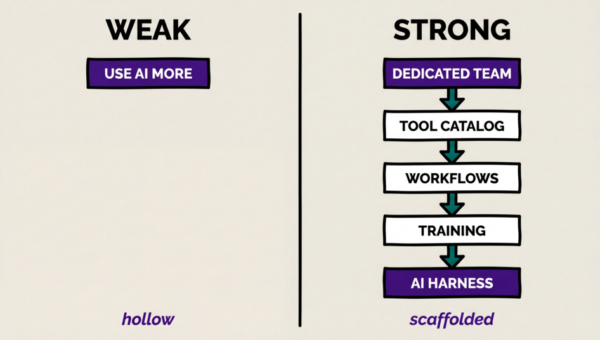
Weak vs. Strong AI Rollouts
I get to see and help with a lot of Anterprise AI rollouts. Some are brilliant, but most (even in 2026) are surprisingly bad. I’ve…