Broken Access Control – Lab #9 UID controlled by param with data leakage in redirect | Short Version

Source link
Related Articles
All Mix →What Is The Common Vulnerability Scoring System (CVSS)
Table of Contents CVSS v2 vs. CVSS v3: What Is the Difference? CVSS vs CVE Limitations of CVSS Organizations need to identify, prioritize, and remediate…
Burp AI takes on a vulnerable web app: watch Tib3rius put Burp’s new agentic capabilities to the test | Blog
Table of Contents What happens when you set Burp AI loose on a deliberately vulnerable web app? In his latest video, Tib3rius takes Burp’s new…
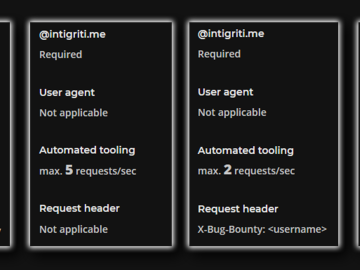
Aggressive scanning in bug bounty (and how to avoid it)
Table of Contents What is aggressive scanning? Why should you avoid it? How can you avoid it? Configuring Common Tools ffuf gobuster sqlmap burp Conclusion…
Intigriti Bug Bytes #225 – June 2025
Table of Contents New update to submission statuses Help us make Intigriti better! Blogs and Videos Exploiting CORS in 2025 Tools Resources Intigriti at FIRSTCON25…
Product comparison: Detectify vs. Qualys
Table of Contents Qualys Detectify In-depth comparison: Visibility and Context So, how do Qualys and Detectify differ when it comes to giving me visibility into…
A Unicode substitution cipher algorithm
How a fun but useless project turned into a Unicode substitution cipher algorithm. Full transparency: I occasionally waste time messing around on Twitter. (Gasp! Shock!)…