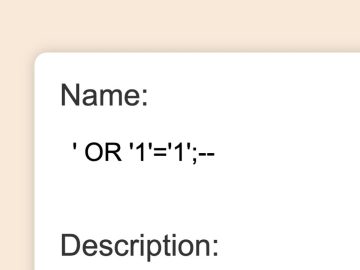
Broken Access Control – Lab#12 Multi-step process with no access control on one step | Short Version

Source link
Related Articles
All Mix →UL NO. 428: Reason to Fear; Reason to Build
Table of Contents TOC NOTES MY WORK SECURITY TECHNOLOGY HUMANS IDEAS & ANALYSIS DISCOVERY RECOMMENDATION OF THE WEEK APHORISM OF THE WEEK Continue reading online…
Say Yes To Cyber Help
In 2016, the DoD said Yes to cyber help by launching the Hack the Pentagon program. It took 13 minutes for them to receive their…
5 Cybersecurity Tips for Marketers
Table of Contents 1. Give your passwords a once-over 2. If 2-factor authentication is an option, use it 3. Update your CMS and enable auto-update…
Observations From DEFCON | Daniel Miessler
DEFCON is a Social Networking EventDEFCON makes all of the audio and video content available (for a price) afterwards, meaning you can watch all of…
The Web Exploit That Would Make Harry Potter Jealous
The Web Exploit That Would Make Harry Potter Jealous Source link
H1-702 Las Vegas Day 0: Setup
Hackers! We have made it to Las Vegas! We are here for a live hacking event (LHE). All live hacking events are amazing, but this…