Building a secure application in five steps | Security Simplified

Source link
Related Articles
All Mix →[tl;dr sec] #197 – Career Resources, Modern Security Podcast, Smashing the State Machine
Table of Contents 📣 Just-in-time access for your cloud infrastructure with ConductorOne Web Security 📣 Rampant cloud activity? Cloud Security Events Machine Learning + Security…
Getting Worried About Linux | Daniel Miessler
So I’m getting a little freaked out lately. I keep hearing that both the Gentoo and Debian projects are in trouble. I haven’t researched how…
Windows is IE, OS X is Firefox
Many are wondering how OS X will fare against malware once it becomes a serious target. We won’t have to wait long; OS X is…
Jwt-Hack: Reborn in Rust | HAHWUL
Table of Contents From Go to Rust: The Core Change Strengthening the Foundation Test Coverage Compatibility Expanded Features Support for More Algorithms New Key-Based Functionality…
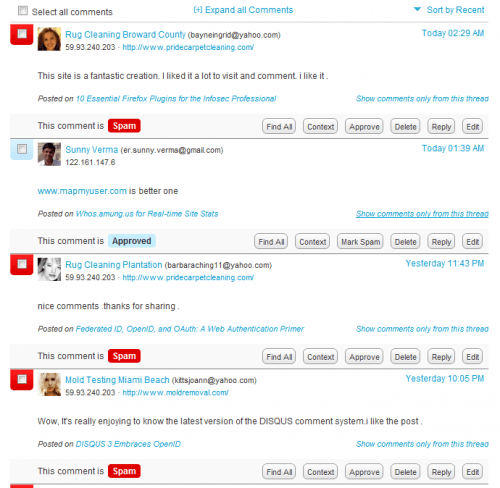
Blog Spam’s Latest Technique: Flattery
Over the last few months I’ve been noticing a trend in blog spam: The use of nice comments and outright flattery. Here are some examples:…
Learn the 3 Key Principles at Kong API Summit 2023
Table of Contents Why API Security Is Non-Negotiable Principle #1: You Can’t Protect What You Don’t Know About Principle #2: Eliminating 100% of Security Issues…